Guidance on Oracle July 2018 Critical Patch Update
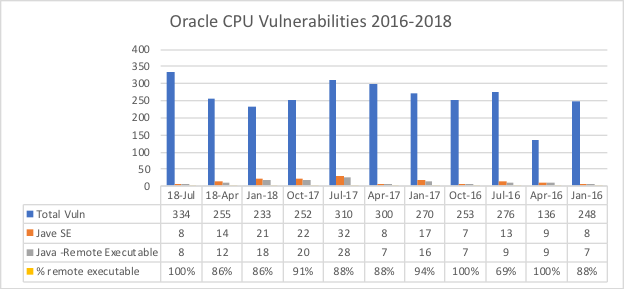
100 percent of the Java SE flaws in the Oracle July 2018 Critical Patch Update (CPU) can be exploited remotely. Learn more below.
Join the DZone community and get the full member experience.
Join For FreeThe Oracle July 2018 Critical Patch Update (CPU) fixes eight (8) Java SE-related vulnerabilities, all of which can be remotely exploited by hackers without user credentials. Five (5) new critical Java vulnerabilities were also fixed in the WebLogic Server, all of which are remotely exploitable without authentication.
Other highlights from the release include:
- The Q3 release patches flaws in Java SE versions 6u191, 7u181, 8u172, and 10.0.1. CVE-2018-2972 affects Java 10 and CVE-2018-2942 affects deployments on Windows.
- Half of the Java SE flaws affect server deployments and half affect client-side deployments. 75 percent of the Java SE vulnerabilities affect a system's confidentiality and 75 percent affect system availability.
- This CPU fixes more new deserialization vulnerabilities in the JDK.
Application Functionality Is at Risk
Several actions taken to fix Java SE vulnerabilities in the July CPU are likely to break the functionality of certain applications. Application owners who apply binary patches should be extremely cautious and thoroughly test their applications before putting patches into production.
The risks of the July updates breaking functionality include:
The fix for the most critical Java SE vulnerability in the July CPU – CVE-2018-2938 – removes the vulnerable component (Java DB) from the JDK. Users that depend on this component must manually obtain the latest Apache Derby artifacts and rebuild their applications.
Waratek Patch customers are unaffected by this JDK component removal. Waratek Patch customers can obtain the virtual patch for CVE-2018-2938 from Waratek, eliminating the need to obtain the latest Apache Derby artifacts and rebuild their applications. Waratek virtual patches are applied in real-time with no downtime or source code changes.
The July CPU release changes the algorithms used in endpoint identification of LDAPS. Applications that us LDAP over TLS connections may stop functioning properly. If backward combability issues arise, Oracle recommends to disable endpoint identification using a new system property.
com.sun.jndi.ldap.object.disableEndpointIdentification.
Waratek Patch customers are not affected by this potentially backward incompatible change of the JDK.
- New deserialization controls in the JDK limit the object creation phase of deserialization. These new security controls may break reflective frameworks that make use of JDK-internal APIs. These security checks can be disabled to allow these reflective frameworks to work normally by setting the system disableSerialConstructorChecks to the value “true”.
By disabling these security checks, attackers can potentially exploit this attack vector.
Waratek Enterprise users are already protected against this deserialization attack vector while allowing reflective frameworks to work as expected.
WebLogic is still plagued by Java deserialization vulnerabilities (CVE-2018-7489). Note that there are claims by a security researcher on Twitter that more zero-day Remote Command Execution (RCE) deserialization vulnerabilities have been reported to Oracle for WebLogic that were not fixed in the July CPU.
Waratek Enterprise users are already protected against these new deserialization vulnerabilities in WebLogic.
For more information about how the July 2018 Oracle Critical Patch Update may impact your applications or how we can help patch and protect your applications with no downtime or source code changes, please contact Waratek.
Published at DZone with permission of John Matthew Holt. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments