SAFe Delivery of Enterprise Cloud Initiatives
Introduce your enterprise's cloud initiative with a mix of old and new ways of working with SAFe.
Join the DZone community and get the full member experience.
Join For Free
In my line of work, I have become familiar with many enterprise cloud programs. While organizations have different levels of cloud adoption maturity and belong to different industry verticals, many cloud initiatives have something in common. Those are the questions that are constantly looming: what is the value of your cloud initiative for the enterprise? What will this cloud initiative deliver next? If cloud services were supposed to provide faster time to market for Line of Business (LOB) applications, why has that not been the case with your initiative? Responding to these questions can be tricky, especially if you spent a few months automating the deployment of a cloud application, only to be informed that your infrastructure solution does not meet enterprise security standards. Or that your newly-configured monitoring solution is not the one that the IT operating team is willing to support.
As time progresses, it becomes increasingly complex to identify the next steps to address internal stakeholders’ expectations. Should you build a private network connectivity solution for a new cloud region? Add new security controls to align with internal and external security requirements? Provide web applications hosting, or, perhaps, deliver content management capabilities? There are many line-of-business programs and applications that have competing deadlines and priorities, all of which are looking at the enterprise cloud initiative for enablement and support. The cloud initiative multi-discipline teams have all the necessary skills and are working hard, but growing complexities and dependencies require constant re-work and refactoring. This frequently lowers the actual delivered value to the point where the direction and objective of the cloud initiative are being questioned.
What Is Your Cloud Initiative Delivery Methodology?
Why is this happening? For the answer, let’s examine delivery methodologies. In many cases cloud initiative teams utilize delivery frameworks that are based on the popular Agile methodologies, such as Scrum and Extreme Programming (XP), and look similar to the following:
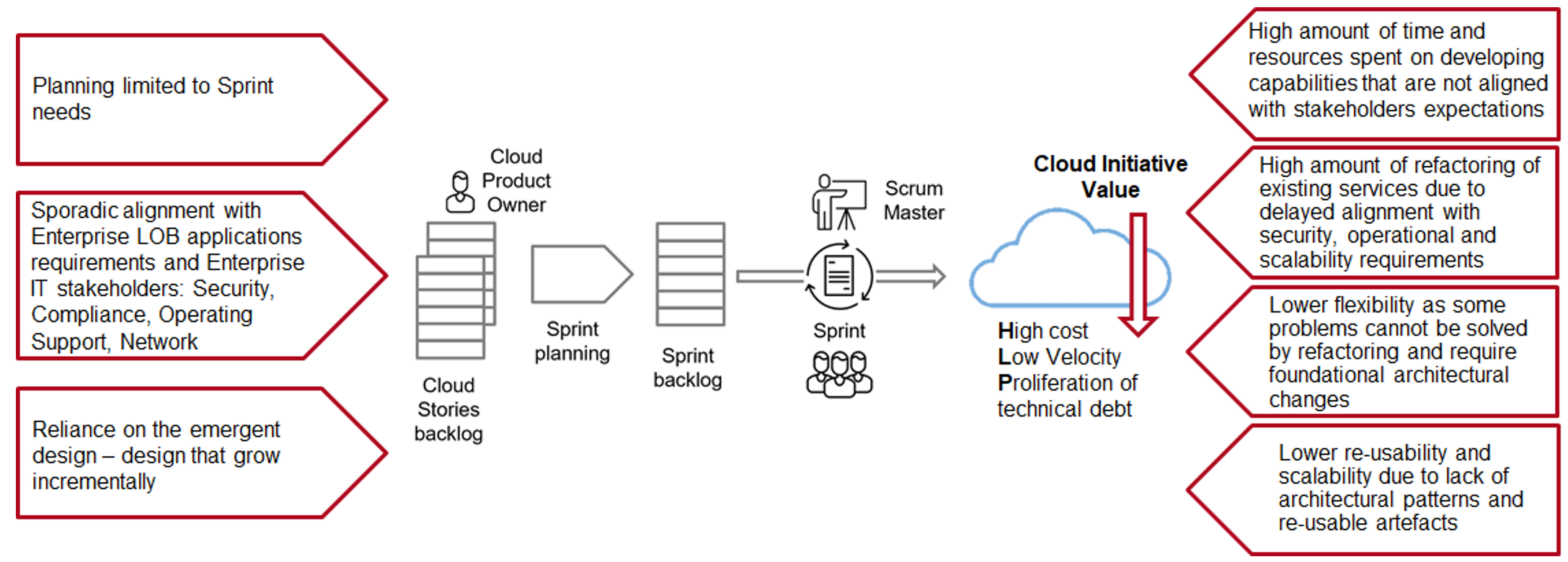
Using a Scrum-based delivery framework fixes Waterfall shortcomings in one part of large-scale delivery processes, but falls short in another. These frameworks do not provide much help when it comes to alignment with enterprise business objectives, handling dependencies outside of Scrum teams, and complex requirements. Frequent re-designs associated with Scrum techniques are very costly for cloud initiatives.
Here is a real-life situation. Functional requirements that are of high-value to cloud LOB applications are typically dependent on non-functional requirements and architecture. A Scrum team would build a shared cloud DMZ that provides security for all network connectivity into the cloud, including intrusion detection, WAF, and other network security functions. But a few weeks later, the team may find that the upcoming business-critical LOB application requires higher throughput than the 1 Gbps that is supported by the current DMZ firewall solution, and addressing this requirement would necessitate re-architecting and re-building the existing DMZ services. To make things even more complex, the existing cloud DMZ may be already used by other applications. With this approach, the team increasingly finds itself facing more and more complex reworking tasks and progressively brittle cloud infrastructure architecture.
Cloud initiatives that would like to alleviate these risks may want to consider using a delivery methodology that allows them to widen the scope of functional and architectural planning beyond one Sprint iteration and provide meaningful alignment to business and customer context while leveraging the benefits of Scrum on a team level. Scaled Agile Framework (SAFe) takes the success of Scrum achieved on small, less complex projects and adds a wide array of Agile, Lean, and System thinking practices to improve the outcomes of large, high value, mission-critical initiatives. This makes SAFe a suitable foundation and end-to-end guiding template for delivering enterprise cloud initiatives:
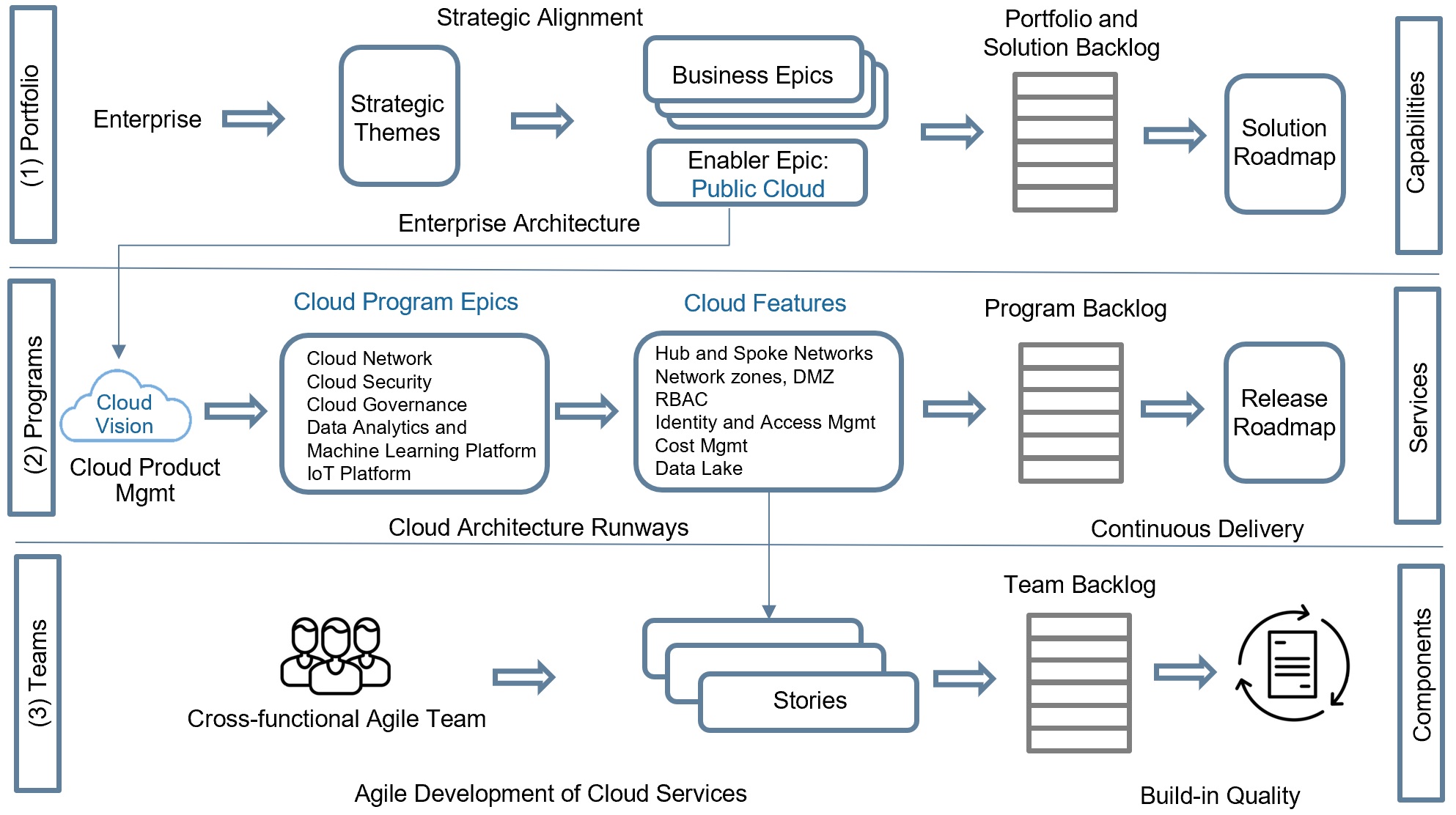
SAFe introduces additional levels: Portfolio, Large Solutions (optional) and Program on top of the Teams level that is similar to Scrum.
The Portfolio level provides strategic alignment between enterprise LOB and cloud initiatives that is critical for identifying cloud directions and services that deliver value to an enterprise and support its business goals. It helps to alleviate the usual obstacles such as fragmented requirements funneled from businesses to IT, the perception of IT as a budget item rather than a business enabler, and misaligned business and IT KPI’s. SAFe Portfolio managing techniques, such as Strategic Themes, allow for clear links between business objectives and differentiators with Portfolio Epics and Program Visions, provide context for decision-making and budgeting.
For example, for healthcare organizations, the Strategic Theme pertained to improving the accuracy of medical predictions and diagnoses is a driver for introducing machine learning and predictive analytics capabilities. Consequently, cloud initiative (represented as Portfolio Epic on the diagram above) would include a platform for machine learning and analytics (represented on the diagram as Program Epic). In its turn, machine learning and analytics program would have a data lake Feature.
The Program level connects the Portfolio level with Agile Release Trains that continuously deliver solutions. At the core of the Program level are Program Epics and Features that provide an incremental decentralized implementation for Portfolio Epics. Every cloud initiative normally has network, security, and governance Program Epics that are Enablers for other cloud capabilities. Machine learning and analytics platforms, IoT platforms, and cloud application migration programs are also examples of Epics, that usually exist on Program level.
In SAFe, a Feature is a service that fulfills a stakeholder need. Hence, in the context of the Cloud Network Enabler Epic, there are typically Features like private network connectivity to cloud and cloud network segmentation. The Cloud Governance Enabler Epic typically includes an RBAC Model, a Resource Tag Model, and Cost and Asset Management Features.
The other important aspect of the Program level is the emphasis on establishing continuous delivery and release on demand. Even though an organization may have a mature Continuous Delivery strategy, cloud initiatives require defining specialized pipelines for network and security resources. The drivers for establishing cloud infrastructures pipelines are different lifecycles and changing cadences between shared infrastructure resources and applications, support for Separation of Duties (SoD), and regular security and networks infrastructure validation checks.
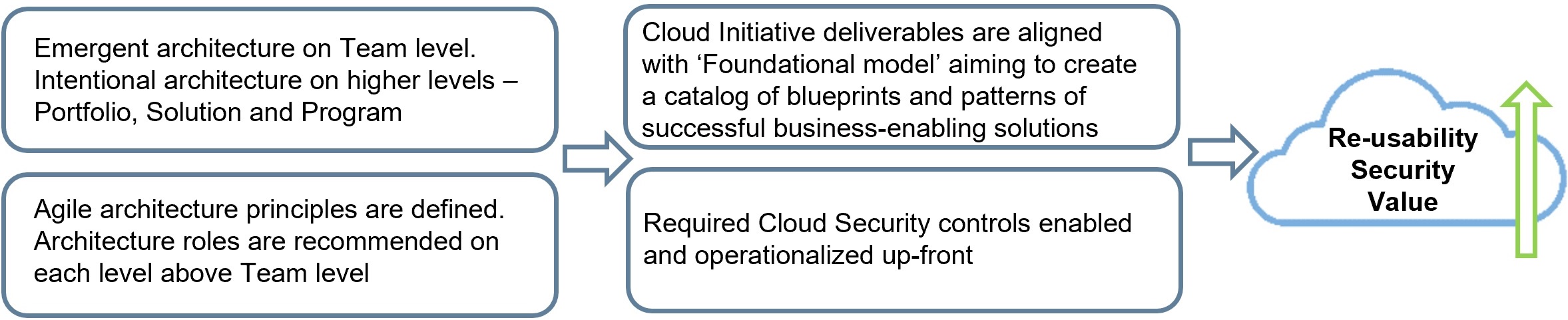
The Program level also addresses the need for balancing emergent design and intentional architectural practices for architecturally significant requirements. SAFe provides specific guidance on leveraging architecture in large-scale initiatives to enable continuous value flow. The notion that considerable effort should be dedicated to planning ahead of implementation is especially valuable for cloud initiatives where significant resources are often invested in cloud infrastructure automation without having enough understanding of the end goals. Cloud initiatives require new strategies, approaches, architecture, design, and tools to address the challenges associated with establishing new Cloud services SLA’s and Cloud Security models. IT services SLA’s are no longer under full control of the organizational IT teams. When it comes to security controls, then some traditional enterprise security controls either do not function or only partially function in cloud environments. Additionally, there is a need to address cloud-specific security risks, hence any cloud initiative would benefit from defining and prioritizing cloud security enabler epics responsible for implementation of cloud security controls.
The impact of applying SAFe Agile architecture principles to Cloud initiatives:
The Team level is similar to a Scrum setup since SAFe aims to maintain the advantages of Scrum that allow teams to be self-managing and self-organizing while delivering at speed. However, there is an important difference — the Product Owner is not a key stakeholder anymore. Product Owner is given primarily a proxy role associated with working with Agile teams and focusing on quality control. To achieve the necessary scalability, SAFe essentially delegates product ownership to Product Management, that in collaboration with architects, define the vision and features. I have seen organizations that attempted giving a single architect a Product Owner role, responsible for all the functionality of cloud initiative, including the network, security, and operational model. This approach has not worked well due to the challenges associated with alignment, scale, security, and conflicts of interests. The cloud initiative inherently has different streams of work and benefits from having scalable product management processes and close alignment with enterprise business and IT stakeholders.
Best Practices Applying SAFe to Increase the Value of Cloud Initiatives
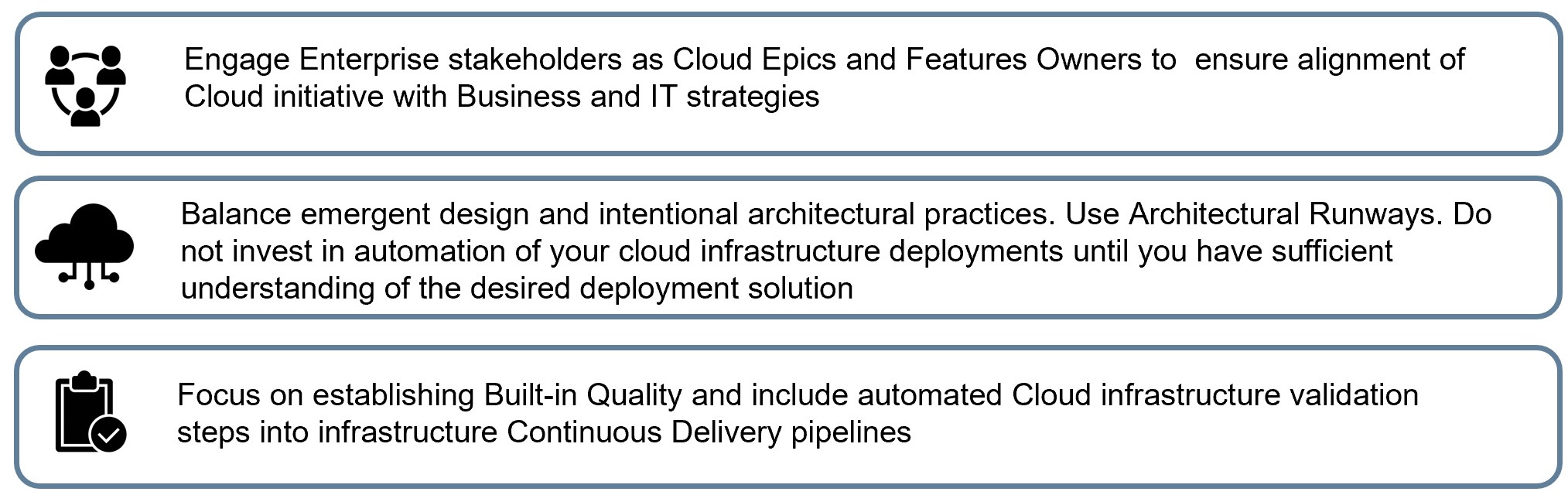
It is important to allow cloud initiative teams to continue to work within Scrum sweet spots, but it is also critical to recognize problems that current practices cannot solve. Adding business context and addressing specific issues associated with large-scale development using SAFe methods allows cloud initiatives to deliver real business value while maintaining necessary agility.
Opinions expressed by DZone contributors are their own.

Comments