Spring Boot Secured By Let's Encrypt
In this post, learn how to use the Let's Encrypt tool with Spring Boot to generate HTTPS certificates and automatically renew them.
Join the DZone community and get the full member experience.
Join For FreeIn this article, we will learn how we can do the following:
- Generate a valid certificate for free
- Configure a Spring Boot app with it
- Renew it when it expires
In my previous blog post, we became familiar with the configuration of a Spring Boot Application with a self-signed certificate (See the code in Git). Self-signed certificates are good for specific purposes such as test and development. But, if one needs to ship his application to production, certificates should be signed by known and legitimate Certificate Authorities (CA).
These types of certificates are usually expensive. If you want to harden your application with TLS, you need to purchase one of them. The price and complex configuration of application servers made a barrier for many web applications to use secure connections. DZone’s previously covered how to create a wildcard certificate.
In the post-Snowden era, no one needs to convince us that having a secure connection using HTTPS is a must. There are lots of efforts to increase the awareness of developers and IT administrators to employ such technologies for every single website they make. But how?
Let's Encrypt projects aims at bringing HTTPS to the World Wide Web not only for free but also with the simplest way of configuration.
In this article, we cover:
Issuing a certificate and Spring Boot integration
How to generate certificates with Let's Encrypt
How to generate PCKS#12 files from PEM files
Configuration of your Spring Boot application
Renewing an (about-to) expired certificate
Renewal process
Preparation for Spring Boot
How to Generate Certificates With Let's Encrypt
Let's Encrypt has several plugins for some application servers such as Apache and Nginx. In this section, as our target is Spring Boot Application (with an embedded Jetty/Tomcat), we just generate the certificates and later on integrate with our application.
If you're using a firewall or any other security mechanism at your server or Cloud provider, you should relax it for a couple of minutes, especially port 80 and port 443.
Port 80 should be open and free to use as Let's Encrypt runs a small HTTP server behind the scene to prove whether you control your domain address (ACME protocol). It’s a simple process to check which applications are using port 8080.
- You need to fetch the source code of Let's Encrypt on your server on which your domain address is pointing. This step may take a couple of minutes.
Remark: Python 2.7.8 (or above) should be installed beforehand.
$ git clone https://github.com/certbot/certbot $ cd certbot $ ./certbot-auto --help - By executing the following command in your terminal, Let's Encrypt generates certificates and a private key for you.
Keys are generated in /etc/letsencrypt/live/seeld.eu.
$ ./certbot-auto certonly -a standalone \ -d seeld.eu -d www.seeld.eu
Remark: 'certonly' means that this command does not come with any special plugin like Apache or Nginx. 'standalone' means that Let's encrypt will automatically create a simple web server on port 80 to prove you control the domain.
How to Generate PKCS12 Files From PEM Files
Certificates and private keys are generated in two steps for free, which shows the simplicity of Let's Encrypt. All of these generated materials are with PEM extension, which is not supported in Spring Boot. Spring Boot does not support PEM files generated by Let’s Encrypt. Spring Boot supports the PKCS12 extension. Using OpenSSL, we convert our certificate and private key to PKCS12.
To convert the PEM files to the PKCS12 version:
- Go to /etc/letsencrypt/live/seeld.eu.
- We convert the keys to PKCS12 using OpenSSL in the terminal as follows.
$ openssl pkcs12 -export -in fullchain.pem \ -inkey privkey.pem \ -out keystore.p12 -name tomcat \ -CAfile chain.pem \ -caname rootThe file 'keystore.p12' with PKCS12 is now generated in '/etc/letsencrypt/live/seeld.eu'.
Configuration of Your Spring Boot Application
Now we want to configure our Spring Boot application to benefit from the certificate and the private key, and eventually have the HTTPS thingy ready. At this moment, we already generated our certificate and private key. Then we converted the keys to PKCS12 extension which is ready to be used for a Spring application.
- Open your 'application.properties'
- Put this configuration there.
Remark'require-ssl' - means that your server only processes HTTPS-protected requests.
server.port: 8443 security.require-ssl=true server.ssl.key-store:/etc/letsencrypt/live/seeld.eu/keystore.p12 server.ssl.key-store-password: <your-password> server.ssl.keyStoreType: PKCS12 server.ssl.keyAlias: tomcat
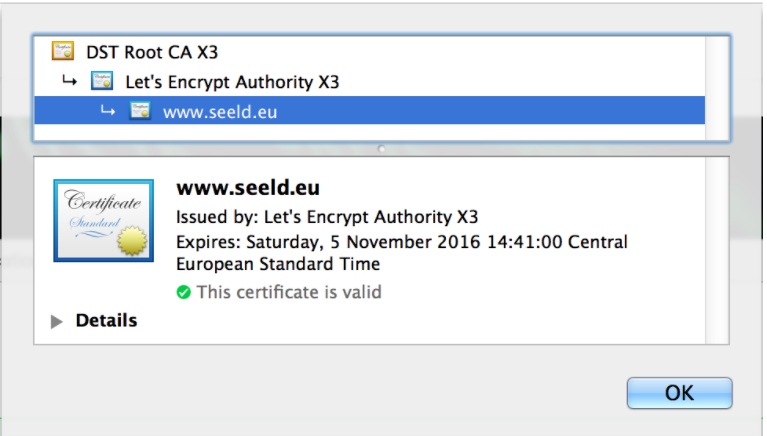
If you visit https://seeld.eu:8443, you can see that HTTPS is successfully configured and, most importantly, working. For the sake of our project, we did some additional steps to have HTTPS working with port 80. You can browse it with the https://seeld.eu URL.
Renewal Process
Let's Encrypt certificates are only valid for 90 days. Some may say 3 months is too short in comparison to the validity period of certificates offered by other providers. They have two motivations for this strict decision: limiting damage from key compromise or mis-issuance and encouraging automation. So let's get started!
- Open your Let's Encrypt client directory, I mean the certbot. Remarks: On the same machine that certificates and keys are located. Please read all of the remarks from sections, such as having python installed, having port 80 open, etc.
- Run the renew command as follows.
This command checks the expiry date of certificates located in this machine (managed by Let's Encrypt) and renews the ones that are either expired or about to expire.
$ sudo ./certbot-auto renew
We have new certificates, as simple as that!
As discussed in the section: Spring Boot does not support PEM files generated by Let’s Encrypt. Spring Boot supports the PKCS12 extension. Using OpenSSL, we convert our certificate and private key to PKCS12.
Preparation for Spring Boot
Let's create a PKCS#12 key store!
- Go to /etc/letsencrypt/live/seeld.eu
- We convert the keys to PKCS12 using OpenSSL in the terminal as follows.
The file ‘keystore.p12’ with PKCS12 is now generated in ‘/etc/letsencrypt/live/seeld.eu’.
$ openssl pkcs12 -export -in fullchain.pem \ -inkey privkey.pem \ -out keystore.p12 -name tomcat \ -CAfile chain.pem \ -caname root
But wait!
I assume the machine that you're working on is the one with running Spring Boot. It means that we're not done yet! The previous ‘keystore.p12’ is still in the memory, meaning that you need to restart your application!
It's not always viable to simply restart a running application. There might be other ways to update it without restarting, but it's not in the scope of this post.
The Take-Home Message
In this post, we saw how to issue, renew a Let's Encrypt certificate, and most importantly, integrate it with Spring Boot. If you really don't unnecessarily play with configurations, it takes less than 5 minutes to have all things ready.
Let’s Encrypt is a great solution, but we’ve covered other tutorials on how to set up an SSL in a Spring Boot application.
The main takeaway message for me is that Let's Encrypt makes (re-)issuing certificates incredibly fast, easy, and cheap for everyone, no matter how many services you manage! You should start having HTTPS as soon as possible.
Opinions expressed by DZone contributors are their own.

Comments