What Is Browser Sandboxing?
This article will explore what browser sandboxing is, the benefits and importance of the different types of sandboxing, and how to implement sandboxing.
Join the DZone community and get the full member experience.
Join For FreeWith a rapidly changing business landscape, security is one of the biggest challenges for developers and testers in their modern web development cycle. The complexity of building and deploying modern web apps leads to more security vulnerabilities. As per a Cost of Data Breach report by IBM and Ponemon Institute, in 2021, data breach costs rose from USD 3.86 million (average cost in 2019) to USD 4.24 million, which is the highest average cost of this report in seventeen years.
Therefore, cybersecurity is becoming increasingly important in the software development lifecycle to ensure user data security and privacy. Wouldn’t it be great if you could develop and test websites and web apps without worrying about security vulnerabilities? Sandboxing is one technique that can help you achieve this. Sandboxing is an approach for securely isolating an application, a web browser, and a piece of code. It prevents malicious or faulty apps from attacking or spying on your web resources and local system.
In the real world, a sandbox is a play area for children enclosed by walls. It allows children to play with sand without the sand-strewn around the lawn. Likewise, the sandbox browser creates an isolated environment where users can download and install applications from third-party sources and operate them in a secure, isolated environment even if they act suspiciously. As a result, the sandbox browser protects your computer from additional security risks.
In this article, we explore what browser sandboxing is, the benefits and importance of the different types of sandboxing, and how to implement it.
Let’s begin!
What Is Browser Sandboxing?
To prevent security breaches in your system or web application, developers need to figure out how to deal with them. This is when browser sandboxing comes in handy. The browser sandbox provides a safe virtual environment to test harmful code or run third-party software without compromising your system’s data or local files.
For example, if you download a malicious attachment within the sandbox, it will not damage your system’s existing files or resources. Sandbox has a same-origin feature, which allows JavaScript to add or customize elements on a web page while restricting access to an external JSON file.
Today, popular web browsers, such as Chrome, Firefox, and Edge, come with built-in sandboxes. The ultimate goal of a sandboxed browser is to protect your machine from the risks associated with browsing. Therefore, if a user downloads malicious software from a website, the software gets downloaded into the browser’s sandbox. Everything inside it, including the harmful code, is wiped out upon closing the sandbox.
Browser sandboxing uses two isolation techniques to shield users’ web browsing activity and system hardware, local PCs, and networks:
- Local browser isolation
- Remote browser isolation
Local Browser Isolation
Local browser isolation is a conventional technique of browser isolation that runs the virtual browsers in the sandbox or the virtual machine on the user’s local infrastructure. It helps in isolating data from external security threats and unsafe browsing. For example, if a malicious element creeps in, the impact will be limited to the sandbox browser and virtual machine.
Remote Browser Isolation
Remote browser isolation involves a virtualization technique in which the browser is run on a cloud-based server (both public and private cloud). In remote isolation, the user’s local system is free from browsing activity, and the browser sandboxing, filtering, and risk evaluation take place on the remote server.
Remote browser isolation involves two ways to isolate user local infrastructure and web content:
- DOM mirroring: In this technique, the browser is not entirely isolated from the user’s local system. However, the DOM mirroring technique filters the malicious content and renders the rest of the content to the user.
- Visual streaming: This technique provides complete remote browser isolation. Visual streaming works like VDI (Virtual Desktop Infrastructure) systems where a browser runs on the cloud-based server, and the visual output is displayed to the user’s local machine.
Why Is Browser Sandboxing Important?
Modern web technologies are expanding rapidly, thereby allowing users to develop and ship websites and web apps without a hitch. At the same time, the demand for web applications is also increasing at an unprecedented pace. According to a survey by Imperva, web applications were the source of 50% of data breaches. Therefore, it is critical to have a secure, controlled environment like a sandbox browser, to perform the operations without jeopardizing your local infrastructure and system resources.
For example, a user is running a web browser in a sandbox. If a malicious code or file exploits web browser vulnerabilities, the impact is restricted within the sandbox. Also, the detonation procedure can aid in the discovery of new vulnerabilities and their mitigation in web browsers. However, if the sandbox browser is disabled, malicious programs can exploit web browser vulnerabilities and damage the user’s local system and resources.
Benefits of Sandboxing
There are various advantages to incorporating a sandbox into your web development workflow. Some of the advantages are mentioned below:
- Sandboxing saves the device and operating system from being exposed to potential threats.
- When working with an unauthorized party or vendor, it is best to use a sandboxing environment. Before deploying stuff, you can use the sandbox to test suspicious code or software.
- Sandboxing can aid in the prevention of zero-day attacks. Because developers cannot discover an instant patch for the exploits, zero-day attacks are inherently harmful. As a result, sandboxing mitigates damage by concealing malware from your system.
- Sandbox environment quarantines threats and viruses. This assists cyber experts in studying and analyzing threat trends. It enables the prevention of future intrusions and the identification of network vulnerabilities.
- Sandboxing applications are a hybrid solution that implies they can be deployed locally and remotely (cloud-based server). Hybrid systems are more secure, reliable, and cost-effective than traditional solutions.
- Sandboxing and RDP (remote desktop protocol) setups assist businesses in ensuring a safe external network connection.
- Sandboxing can be used in conjunction with antivirus or other security tools and policies to strengthen your entire security ecosystem.
What Assets Are Being Sandboxed?
The bulk of the assets we use in our daily workflow, like online browsers, web pages, PDFs, mobile apps, and Windows applications, are sandboxed.
The assets that are being sandboxed are listed below:
- Web browsers: The potentially vulnerable browsers run in sandboxed environments.
- Browser plug-ins: While loading content, browser plugins operate in a sandbox. Sandboxed browser plugins, like Java, are more vulnerable to attacks.
- Web pages: The browser loads the web page in sandbox mode. Since a web page is built-in JavaScript, it cannot access a file on your local computer.
- Mobile apps: Mobile OS, like Android and iOS, runs their app in sandbox mode. They pop up the permission box if they wish to access your location, contacts, or other information.
- Windows software and programs: Before making changes to system files, User Account Control (UAC) in Windows OS asks for your permission. UAC functions similarly to a sandbox, although it does not provide complete protection. However, one shouldn’t disable it.
Different Types of Sandboxing
In this section on browser sandbox, we discuss the different types of sandboxing. Sandboxing is divided into three categories:
- Application sandboxing
- Browser sandboxing
- Security sandboxing
Application Sandboxing
With application sandbox, you can run untrusted applications in a sandbox to prevent them from damaging your local system or stealing data. It helps create a secure environment where apps can run without the risk of damaging the system. By isolating the app from the user’s local computer, application sandboxing enhances the app’s integrity.
Browser Sandboxing
Potentially malicious browser-based applications can be executed in a sandbox to prevent them from causing harm to your local infrastructure. It leads to establishing a secure environment in which web apps can run without compromising the system. The detonation technique can aid in the discovery of new vulnerabilities in web browsers and their mitigation.
Security Sandboxing
Security sandboxing lets you explore and detect suspicious code. It scans attachments and identifies a list of potentially harmful websites, and determines whether one downloads or installs infected files.
Sandboxing With an In-Built Sandbox Browser
Sandboxes come pre-installed in popular browsers, like Chromium, Firefox, and Edge, to protect your system from browsing vulnerabilities. Let’s look at how sandboxing works in different browsers:
Chromium Browser Sandboxing
Google Chrome and Microsoft Edge are built on the Chromium browser. The broker and the target are the two processes that make up the Chromium browser sandbox. The target process is a child process, while the browser process is a broker process. The target process’s code is executed in a sandbox environment. The broker process acts between the child process and hardware resources to offer resources to the child process.
Firefox Browser Sandboxing
To protect the local system from threats, Firefox executes untrusted code within a sandbox. The Firefox browser is sandboxed by using the parent and child processes. When browsing, potentially malicious programs are run in the sandbox. The parent is a mediator between the child process and the rest of the system resources during sandboxing.
You can change the degree of sandboxing in Firefox browsers to make it least, moderate, or highly restrictive:
- Level 0: Least restrictive
- Level 1: Moderate
- Level 2: Highly restrictive
To check the level of the Firefox sandbox browser, pass the below command in the address bar:
about:configOn the page, it will load the Firefox configurable variables. Now, hit “CTRL+F” on the config page, enter the following commands in the search box, and press “Enter.”
Edge Browser Sandboxing
When you launch the Edge sandbox browser Windows 10, you’ll be presented with a fresh desktop that has simply the “recycle bin” and Edge shortcuts. It displays the “Start Menu” and other icons, but they aren’t functional in this sandboxed environment. Instead of the sandboxed Windows 10, you can access them on the standard Windows 10.
When you close the Edge browser sandbox, your browser history is no longer available. Your ISP may keep track of actions in the sandbox, but this data is not auditable.
Disabling the Google Chrome Sandbox
While performing Chrome-based sandboxing testing, you may come across a scenario where the sandbox feature can cause the Chrome browser to flash the following error: “The Application Has Failed to Initialize.”
In that case, you may need to disable the Chrome browser sandbox. Here are the following steps:
- Create a Google Chrome Sandbox shortcut if you don’t have one.
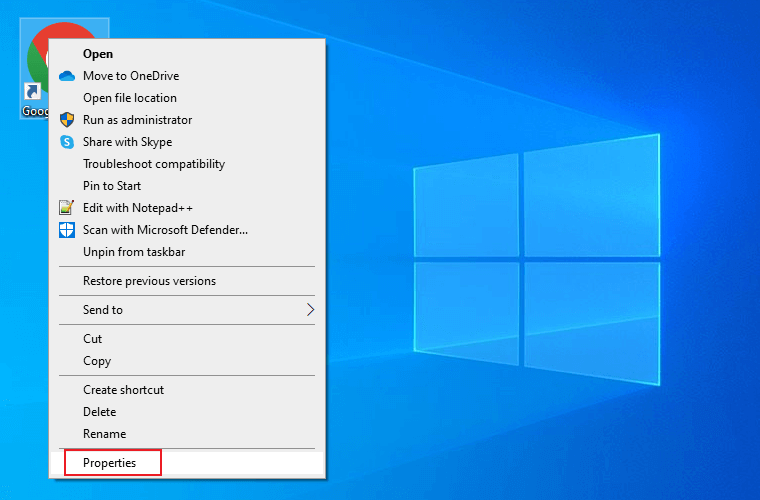
- Right-click on the shortcut and select “Properties.”
![select Properties]()
- Enter the below command to the app path provided in the Target:
--no-sandbox
4. Click “Apply,” and then “OK.”
Browser Sandboxing: Is it 100% Secure?
Most web browsers use a sandbox. However, the internet is still a source of viruses and other malware. The level of sandboxing appears to vary. Different web browsers implement sandboxing differently, so it’s hard to figure out how they work. However, this does not mean that all web browsers are unsafe. On the other hand, a browser sandbox can make them more secure.
But, if you ask whether it provides 100% security, the answer is no. Some browser components may stretch outside the sandbox if they use Flash and ActiveX.
Wrapping Up!
Businesses are attacked by Advanced Persistent Threats (APTs), and sandboxing can protect them. By seeing what’s ahead, you can prepare for unknown attacks. You can test and develop applications in an isolated environment without compromising your local system assets with sandboxing. Sandboxie, BitBox, and other sandboxing tools are available in the market. However, it takes time to set up and install different browsers in the sandbox.
This article discussed how to use LambdaTest cloud-based platform for your browser and app testing to develop and test applications in a secure remote environment without endangering your local system.
Hope you liked the article, and if you have any questions, please feel free to drop them in the comments.
Published at DZone with permission of Salman Khan. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments