Introduction
Industrial Internet
While the “regular” Internet is a “network of networks” that connects people with information, the Industrial Internet (sometimes refered to as Industrial IoT or IIoT) networks machines, systems, people, and physical industries—via the Internet—in order to collect, organize, and analyze the world’s industrial data, enabling the next generation of data-driven Digital Industrial companies.
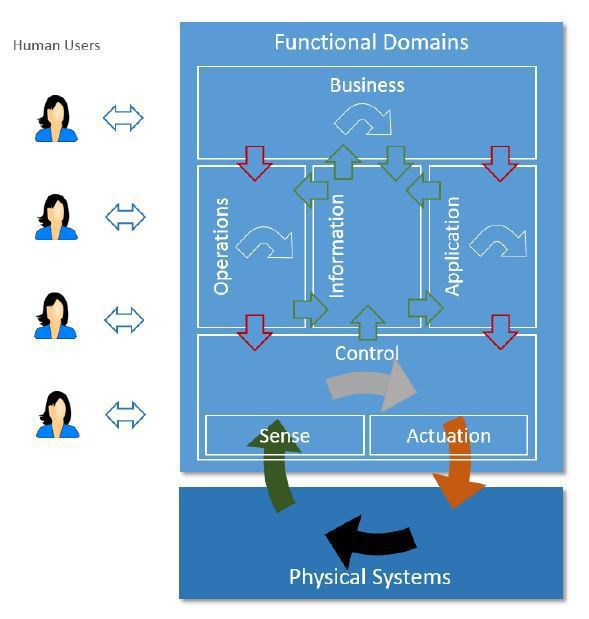
Operational Technology (OT)
Operational Technology (OT) describes a piece of software or hardware that directly interacts with the physical world. It either receives information about the environment outside of itself through sensors; or, using actuators, it can make alterations to that environment. OT components represent the data sources ingested into the Industrial Internet, the points of connection between the physical and the digital. If the Internet, as a network that relays information, is a central nervous system, with the cloud acting as a brain, then operational technology makes up the body. It gives the Internet eyes and ears, arms and fingers, so that it can gather information for itself and act upon that information. Still, OT components have local autonomous decision and execution capabilities.
IT/OT Convergence
The convergence of information technology (IT) and operational technology (OT) is reshaping long-standing processes in virtually every industry to allow complex systems to monitor, maintain, control and optimize themselves, removing the necessity for human involvement (and thus reducing the possibility for human error) in a growing number of tasks and actions.
IT/OT convergence refers to two distinct trends: First, established IT best practices (for software development, deployment and operations) are being applied to increasingly software-defined OT systems. Second, legacy IT systems (such as ERP accounting or inventory management systems) are being interfaced with business-critical OT systems and Industrial Internet platforms, enabling end-to-end automation of processes such as asset repair and maintenance.