AI-Genetic Algorithm in Malware Detection
Genetic algorithms can evolve signatures and detection patterns for identifying malware and malicious code within large datasets.
Join the DZone community and get the full member experience.
Join For FreeWhat Is a Genetic Algorithm?
Genetic algorithms are considered a subset of artificial intelligence (AI).
Artificial intelligence broadly refers to the simulation of human intelligence processes by machines, including learning, reasoning, problem-solving, perception, and decision-making. Genetic algorithms fall under the category of computational intelligence, which encompasses AI techniques inspired by biological processes.
Genetic algorithms are a type of optimization algorithm inspired by the process of natural selection and evolution in biology. They use concepts such as mutation, crossover, and selection to search for optimal solutions to a given problem by mimicking the process of natural selection. In summary, while genetic algorithms may not exhibit all aspects of human-like intelligence, they are a powerful AI technique used for optimization and search problems.
The core idea behind genetic algorithms is to simulate the process of natural selection to iteratively evolve potential solutions to a given problem. This is achieved by representing candidate solutions as individuals in a population, typically encoded as strings of symbols (often binary, but can be other types as well).
The typical steps involved in a genetic algorithm include:
- Initialization: A population of individuals (potential solutions) is randomly generated to start the optimization process.
- Selection: Individuals from the population are selected for reproduction based on their fitness, which is determined by how well they perform according to a predefined objective function.
- Recombination (Crossover): Selected individuals (parents) undergo recombination, where their genetic material is combined to produce new individuals (offspring). This is usually done by exchanging segments of genetic material between parent individuals.
- Mutation: Occasionally, random changes are introduced into the genetic material of offspring individuals to maintain genetic diversity and explore new areas of the search space.
- Evaluation: The fitness of the newly created individuals is evaluated based on the objective function.
- Survivor Selection: The next generation of individuals is formed by selecting individuals from the current population, often based on a combination of their fitness and other criteria like elitism.
- Termination: The algorithm continues iterating through these steps until a termination condition is met, such as reaching a maximum number of generations or finding a satisfactory solution.
Genetic algorithms can evolve signatures and detection patterns for identifying malware and malicious code within large datasets. By analyzing the characteristics and behaviors of known malware samples, genetic algorithms can generate efficient detection rules that can be used to identify similar threats.
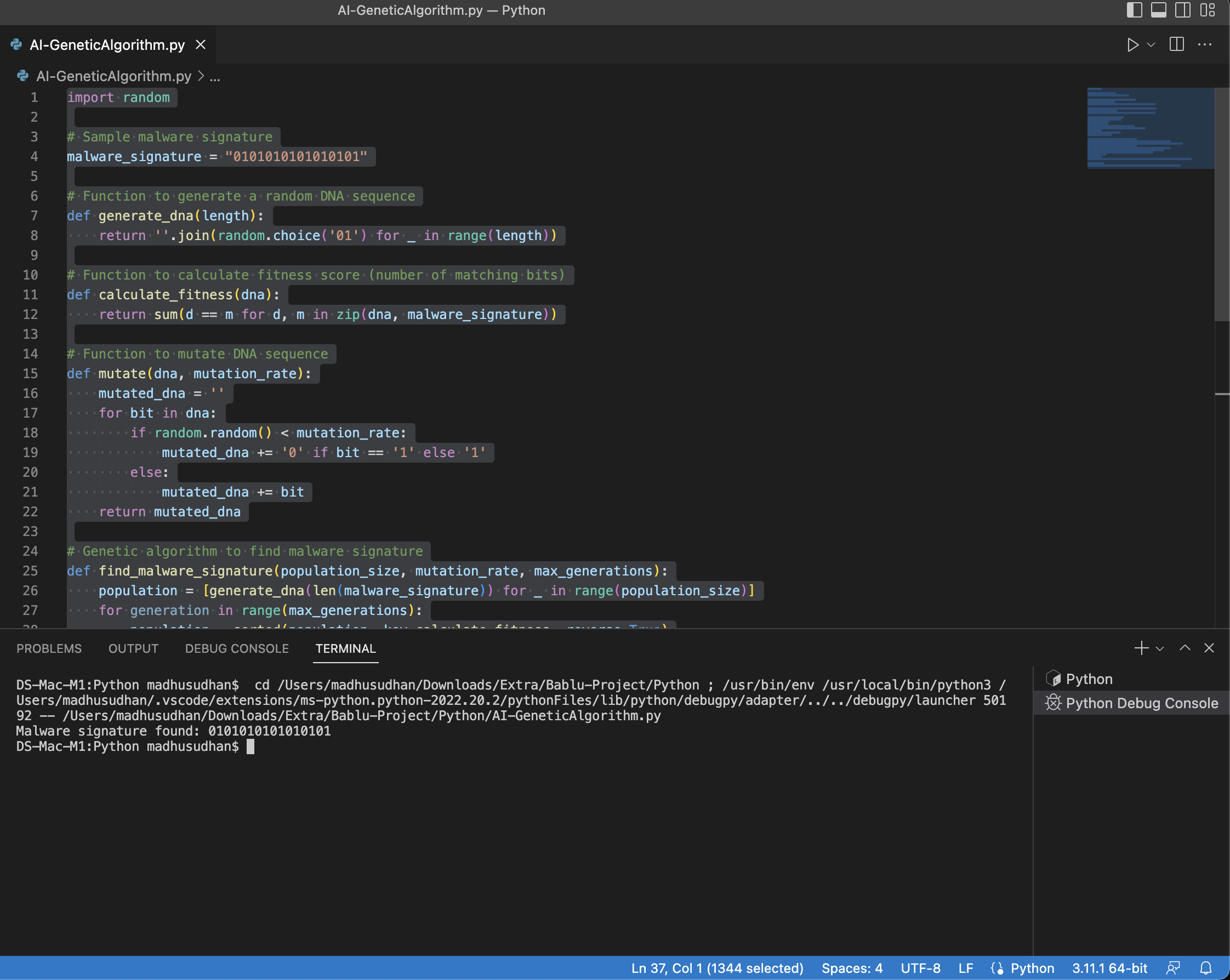
Code Block
import random
# Sample malware signature
malware_signature = "0101010101010101"
# Function to generate a random DNA sequence
def generate_dna(length):
return ''.join(random.choice('01') for _ in range(length))
# Function to calculate fitness score (number of matching bits)
def calculate_fitness(dna):
return sum(d == m for d, m in zip(dna, malware_signature))
# Function to mutate DNA sequence
def mutate(dna, mutation_rate):
mutated_dna = ''
for bit in dna:
if random.random() < mutation_rate:
mutated_dna += '0' if bit == '1' else '1'
else:
mutated_dna += bit
return mutated_dna
# Genetic algorithm to find malware signature
def find_malware_signature(population_size, mutation_rate, max_generations):
population = [generate_dna(len(malware_signature)) for _ in range(population_size)]
for generation in range(max_generations):
population = sorted(population, key=calculate_fitness, reverse=True)
if calculate_fitness(population[0]) == len(malware_signature):
print("Malware signature found:", population[0])
break
else:
population = [mutate(population[0], mutation_rate) for _ in range(population_size)]
# Example usage
find_malware_signature(population_size=100, mutation_rate=0.01, max_generations=1000)
In this example:
- We start with a random population of DNA sequences (binary strings).
- The fitness score of each sequence is calculated based on how many bits match the malware signature.
- We select the top-performing sequences and mutate them to generate a new population.
- This process continues until we find a sequence that matches the malware signature or reaches the maximum number of generations.
This is a basic example, and in real-world scenarios, you would use more sophisticated techniques and larger datasets. Additionally, you would need to consider factors such as the diversity of malware samples and the performance of the detection algorithm.
Opinions expressed by DZone contributors are their own.

Comments