AWS Internet Gateway and VPC Routing
An Internet Gateway is a logical connection between an AWS VPC and the Internet. It allows for internet traffic to actually enter into a VPC. We look at how to set it up.
Join the DZone community and get the full member experience.
Join For FreeIntroduction
In the previous post on AWS VPC Basics, we learned about VPC basics and we also set up a VPC with public and private subnets.
In this post, we will learn about another powerful component from AWS, the gift of the internet, The Internet Gateway. We will also learn how routing works within VPC, how to set up routes to the internet gateway and our public subnet. This setup is very common for most of the applications on AWS.
An internet gateway is a service that allows for internet traffic to actually enter into a VPC. Otherwise, a VPC is completely segmented off and then the only way to get to it is potentially through a VPN connection rather than through an internet connection.
An Internet Gateway is a logical connection between an AWS VPC and the Internet. It is not a physical device. Each VPC has only one Internet Gateway. If a VPC doesn’t have an Internet Gateway, then the resources cannot be accessed from the Internet. Conversely, resources within your VPC need an Internet Gateway to access the Internet.
In later posts, when we will be creating EC2 instances in subnets, then we will see how it is used to allow internet access.
Also, In order for us to allow the developers to connect to the VMs, to a jump server, or a bastian-host, we have to have this internet gateway first. We typically use a NAT instance or NAT Gateway for this purpose.
A Network Address Translation (NAT) enables instances in a private subnet to connect to the Internet, but prevent the Internet from initiating a connection with those instances. To do that, NAT maps all the private IP addresses assigned to the instances in the subnet to one public IPv4 address called the Elastic IP address.
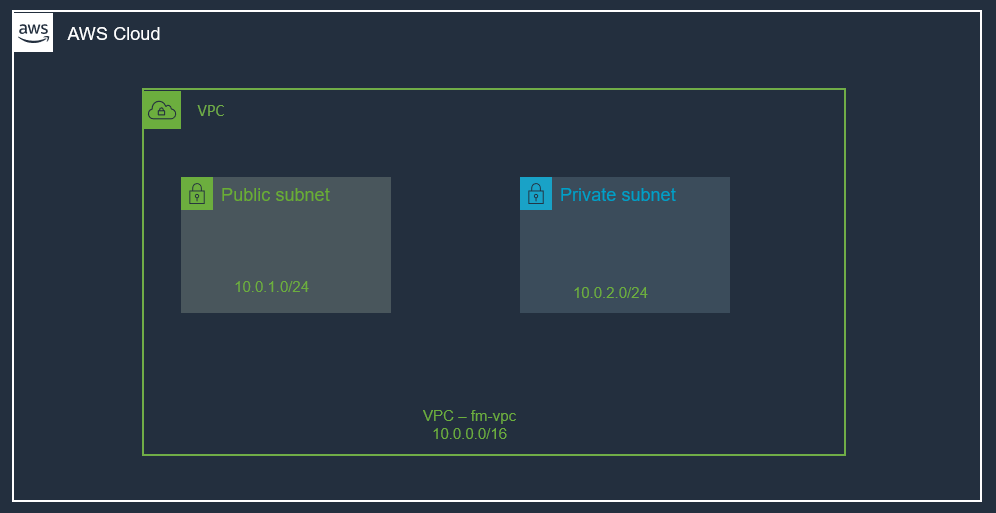
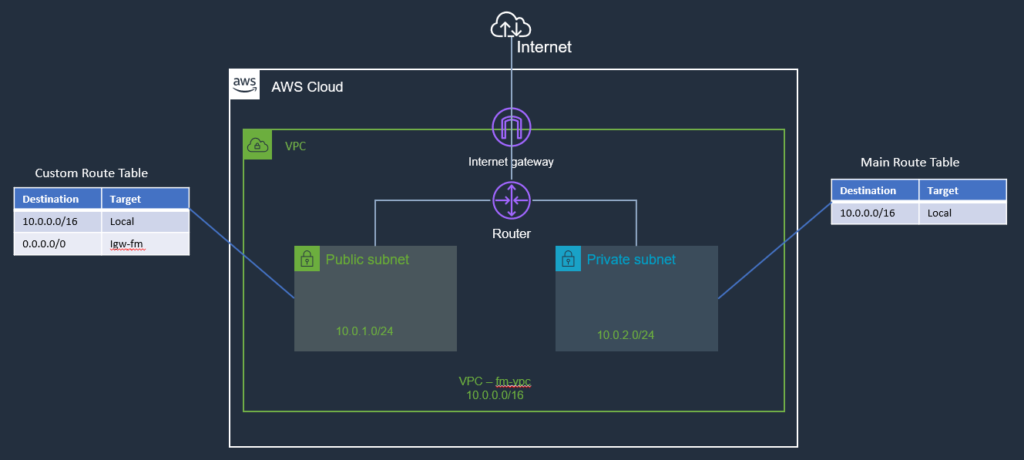
Here is how our setup looks like from the previous post:
In order to allow internet traffic to our VPC, we can use an Internet Gateway. Let’s create an internet gateway next.
Create an Internet Gateway
First things first, let's create an internet gateway. You can create an internet gateway by navigating to VPC and creating it via the AWS web console:
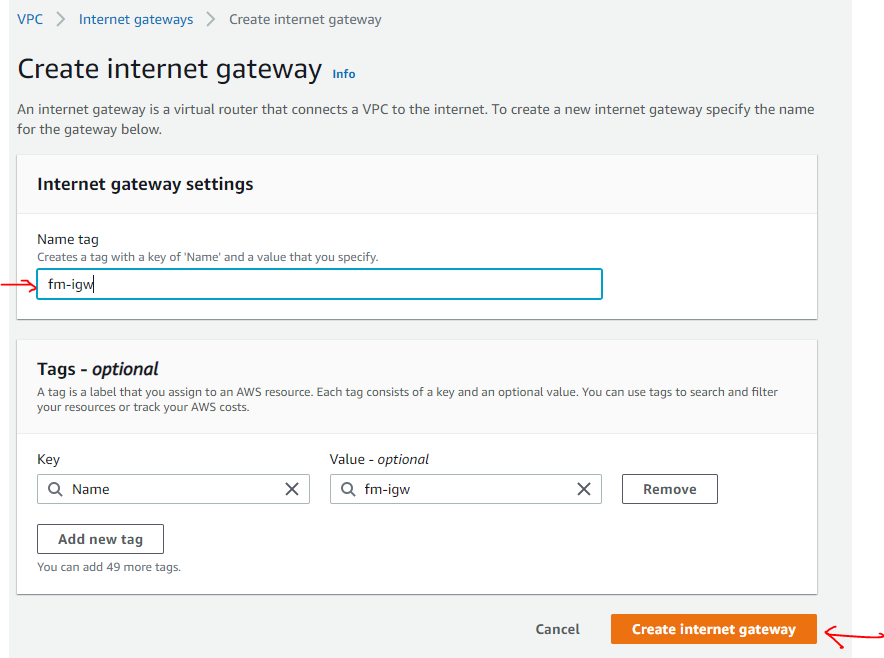
That's all it takes, providing it a name and internet gateway is created.
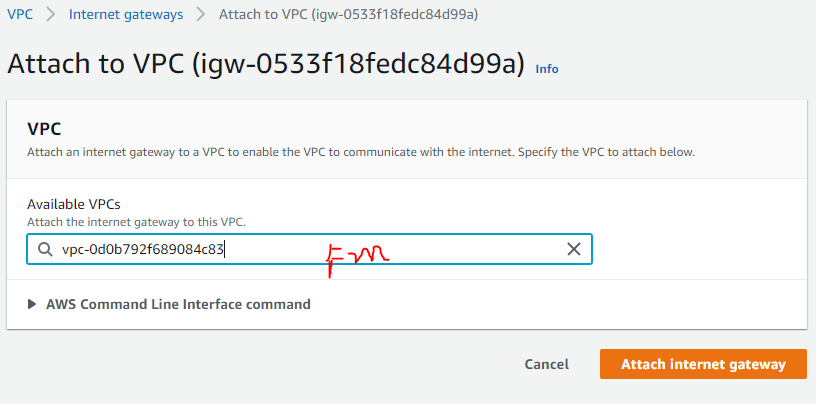
So, we created an internet gateway, but it's just sitting there by itself. It's not doing anything yet.
Remember, an internet gateway is used to allow internet traffic to VPC, so it needs to be associated with a VPC.
Select Internet Gateway Resource --> Click on Actions --> Attach VPC
(select VPC created earlier)
Here is the attached internet gateway:
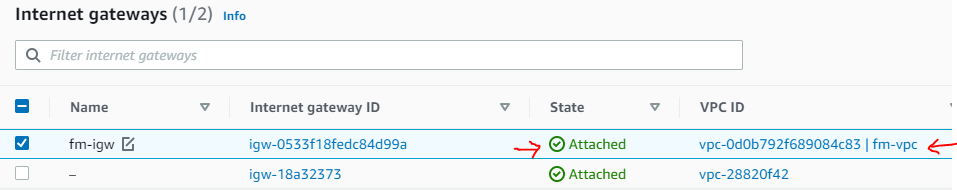
This will allow traffic to enter the VPC, but we can lock it down. That’s where Security Groups are going to come into play (we will talk about those a little bit later).
Before we continue with anything else, let's take a step back and talk about Route Tables.
Router and Route Tables
Routing is a big part of networking. In AWS, it's very easy to setup. Every VPC has an implied router, you don’t need to create it, it's already there. It routes the traffic within the VPC and then we also have route tables that contain routing entries. Normally we just work with route table entries. Think of a road and road-signs analogy; the router is the road and road-signs are the route table entries.
A route table specifies how packets are forwarded between subnets within your VPC, the internet, and your VPN connection.
A route table contains a set of rules called routes which determine where traffic has to be directed. You can create as many route tables in a VPC as you want. Route tables act at the subnet level, not the VPC level. A route table can be associated with one or several subnets. By default, all route tables in a VPC have a local route for communication within the VPC. You can add custom routes in a route table by creating a new route defining which traffic (IP destination) must go where (target).
If a subnet is associated with a route table redirecting all traffic to an internet gateway, it is called a public subnet.
If you remember from the previous post, a primary route table was created automatically by AWS when we created our VPC. If you now visit the route tables page in the AWS console, you will find a list of existing route tables. We can also create new route tables, and this is what we will do, we will create a custom route table as shown below:
Create a Custom Route Table
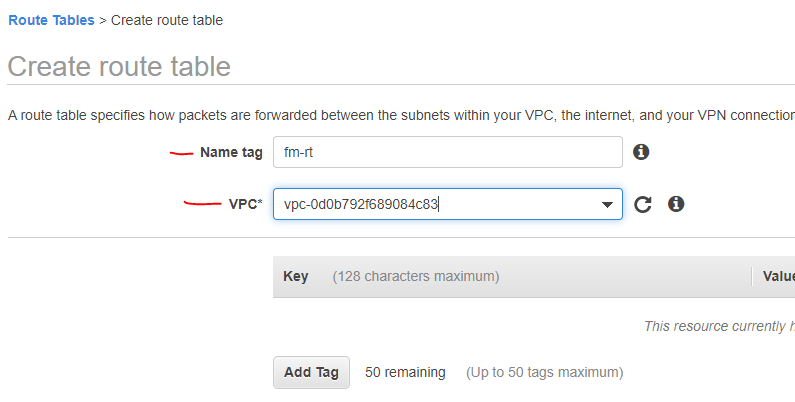
From the VPC page, select the Route Tables item and Click Create Route Table. We need to provide a name for the route table and select our VPC as shown below:
Next, we will add a route for the internet gateway to this custom route table.
Add Route for Internet Gateway to A Custom Route Table
Select the route table, and edit the routes as shown below:
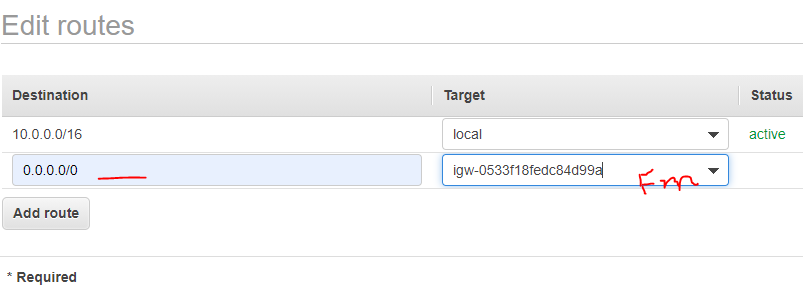
Notice that the first entry (10.0.0.0/16) is for VPC local traffic and we added a catch-all route (0.0.0.0/0) and set its target to our Internet Gateway, which we created at the beginning of this post.
Associate Custom Route Table to Public Subnet (for Internet)
Our custom route table now has a route with Internet Gateway. Next, we will associate it with the public subnet.
VPC –> Subnets –> Select Public Subnet –> RouteTables –> Edit Route Tables Association
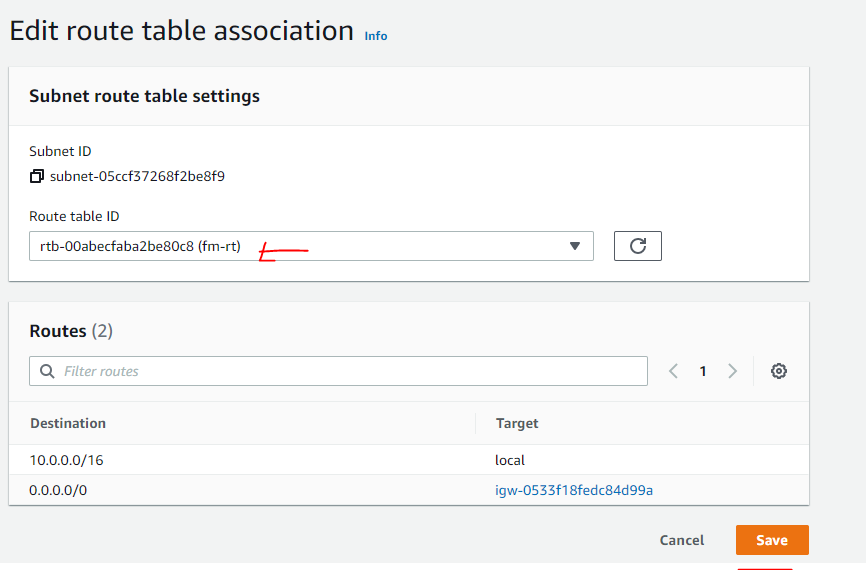
The following screenshot shows the association of the route table with the public subnet.

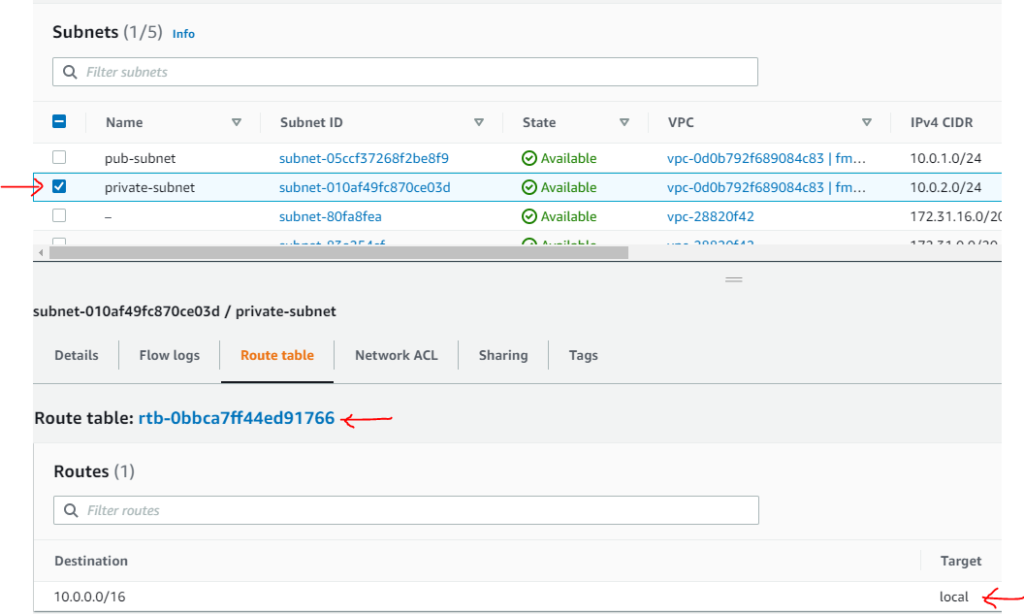
Private Subnet Route Table Association
Our Private subnet is still associated with the main route table (no internet) and that is what we want for our private subnet. So, we do not need to do anything.
A private subnet is a subnet with no direct route to an Internet Gateway (IGW). In other words, it has no public IP addresses, no publicly accessible resources, no direct internet access to/or from that subnet.
Infrastructure View
Let’s see how our infrastructure looks like now. The following picture shows these components:
Summary
In this post, we continued our journey from where we left it in the previous post on AWS VPC Basics. We have extended our infrastructure a little bit by adding an internet gateway and then set up the routing by creating a custom routing table associated with the public subnet. In the next post, we will resume our journey from this point. Let me know if you have any questions or comments. Till next time, Happy Coding!
Published at DZone with permission of Jawad Hasan Shani. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments