GCP Made Easy
A host of flowchart graphics and tables can help answer a lot of the questions you may have about GCP.
Join the DZone community and get the full member experience.
Join For Free
I believe GCP endeavors to be simple to use, but inevitably there will be times when choices will have to be made about what path or product is right for your use case. Thus, flowcharts are a thing that comes it comes to owning when a decision needs to be made.
GCP has produced a number of flowcharts this year (2017) covering a variety of use cases. Not sure how to manage your encryption keys, which interconnect path to use, or which compute or storage type you require? GCP has a flowchart to help. I have a few favorites but they are all well worth looking at.
Here I’ve collected a few of my favorite GCP flowcharts for your perusal. Plus I wanted to have one place I could find them. I’ve included a link to the original doc or blog that accompanied each flowchart. So not dillying or dallying hope you find this collection of flowcharts as handy as I do.
Attribution: All graphics & flowcharts ( apart from the original authentication flowchart that has now been replaced) cheerfully copied from the Google Cloud platform or blog site.
Which Compute Option?
GCP has a continuum of compute options which can be graphically depicted as:

It may be obvious at either end of the continuum which option you choose but the decision becomes less straight forward in the middle so flowchart to the rescue :
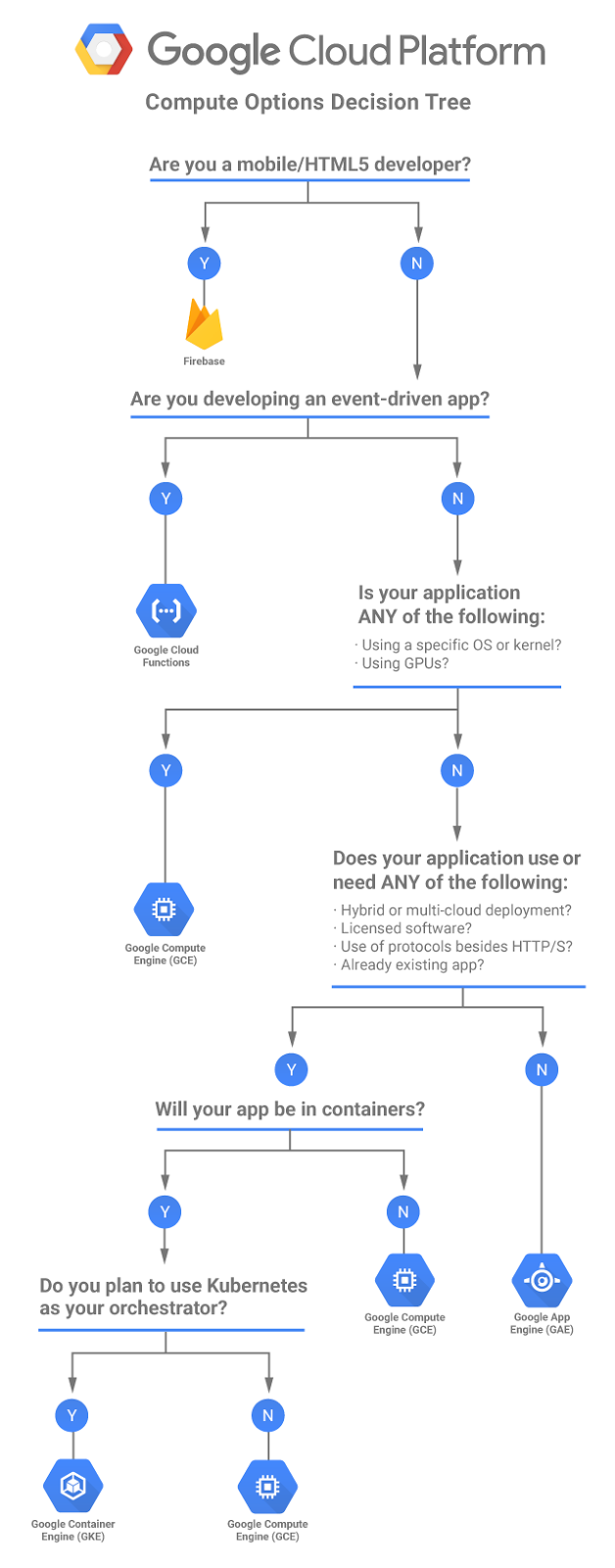
The compute flowchart with accompanying description can be found here and a nice table comparing the compute options is here.
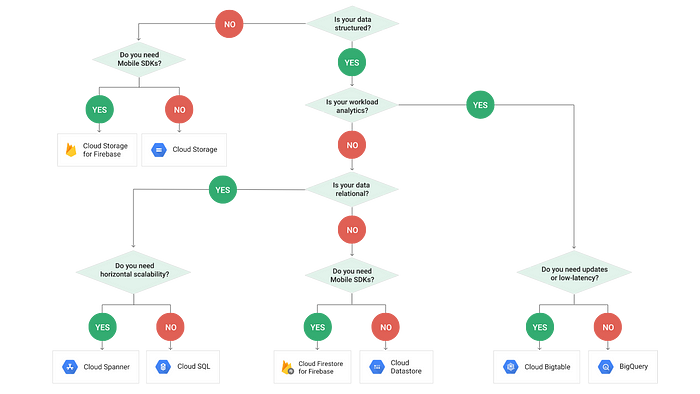
What Storage type?
Data data data data data! (sung to the 60’s Batman theme songs). I struggle to think of any application where data isn’t a thing. The myriad ways you can store your data is probably after considering the security controls needed the most important decision you need to make. GCP has your back with a great flowchart and tables (I love tables, too) which can be found here.
Which Network Tier?
GCP’s network is fantastic but it’s recognized that not every use case needs to optimize for performance and cost may be the driver. So welcome to network tiers.
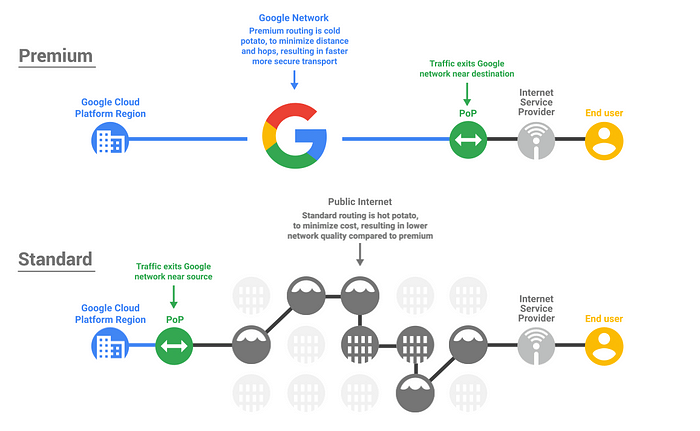
You can see the funky animated gif for the above image here.

The description that go with the above can be found here. There are some useful tables there, too.
How to Manage Encryption Keys
GCP has a continuum of ways for you to manage your encryption keys graphically depicted as

Yes, I know that the continuum graphic alone is probably all you need, but when the announcement for the KMS service was made, they produced a flow chart and I just had to include it here.

The description that go with the above can be found and a nice table that compliments the flow chart can be found.
The description that goes with the above can be found here and a nice table that compliments the flow chart can be found here at the Encryption at rest landing page. Everything you ever wanted to know about Encryption at rest on GCP and more!
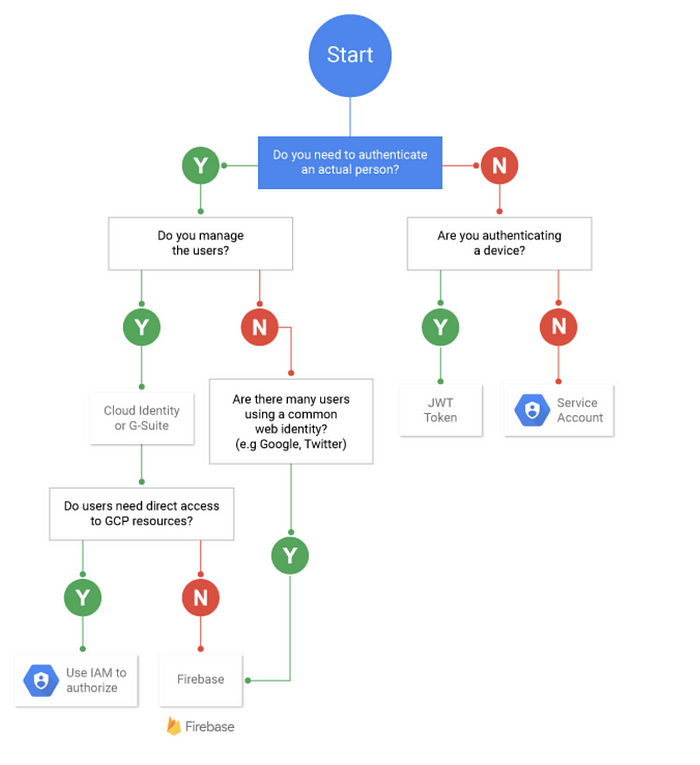
Which Authentication Option?
I’m going to sneak in a flowchart of my own as GCP doesn’t have one for this yet.
So just to make sure we are on the same page, authentication identifies who you are. This flowchart is focused on whether its identity goes to the application (deployed on GCP) or direct access to GCP.
Opinions expressed by DZone contributors are their own.

Comments