Get the Credential Store Framework Key Inside SOA Composite on BPEL
Often we face a scenario where the service being called does not follow the standards or uses some kind of home-made authentication, even inside the SOAP Body...
Join the DZone community and get the full member experience.
Join For FreeWe know that Oracle WSM (Web Services Manager) agents handles the Credential Store very well and is the best approach to calling secure services through client policies. For example, if we need to call a service that is secured by WS-Security Username Token, we can simply attach the “oracle/wss_username_token_client_policy” to the service reference, and then use the “csf-key” binding property to make a reference to some credential, and the OWSM agents will do the will do all the work.
Often we face a scenario where the service being called does not follow the standards or uses some kind of home-made authentication, even inside the SOAP Body. Furthermore, there are many use cases where it can be useful to get access to a CSF Credential Key inside the BPEL flow, programmatically, to get your hand on the username and password and assign them to variables to do whatever you need.
It’s possible to do this trick using the “Credential Store Framework API” (CSF API), though a “Java Embedding” activity. There are a few steps needed to accomplish this, which are described below:
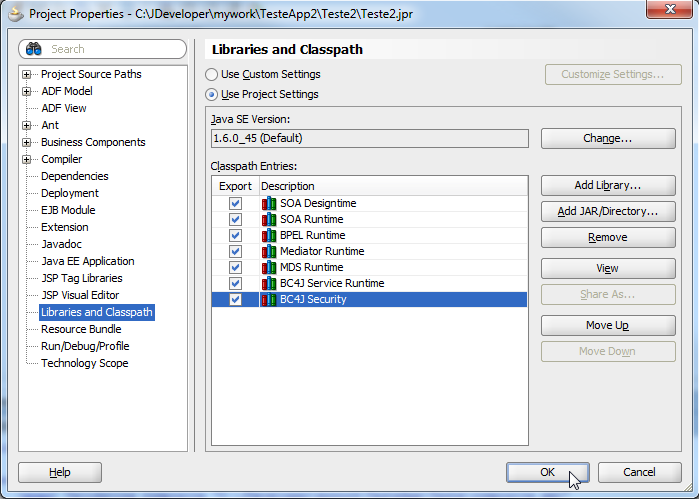
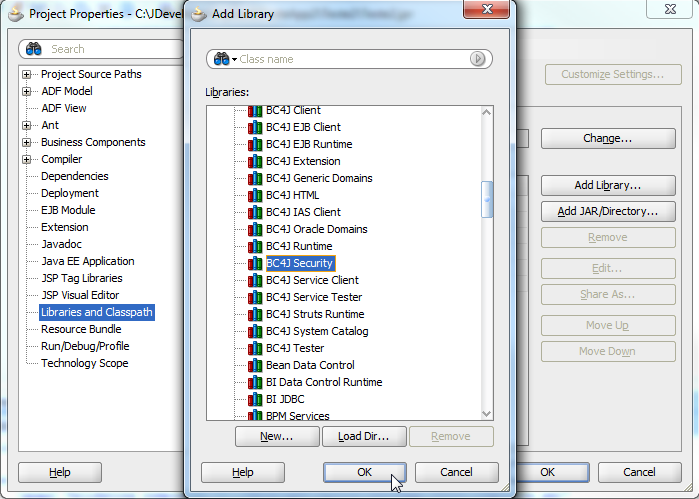
1 – Prepare your IDE, adding the library “BC4J Security” in the project’s classpath on JDeveloper: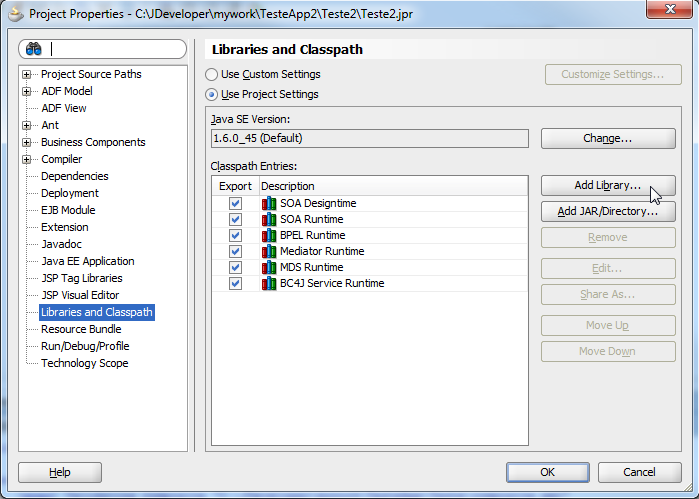
2 – Create a “Java Embedding” activity to retrieve the username and password from the credential store:
try {
oracle.security.jps.JpsContextFactory jpsCtxFactory = oracle.security.jps.JpsContextFactory.getContextFactory();
oracle.security.jps.JpsContext jpsCtx = jpsCtxFactory.getContext();
oracle.security.jps.service.credstore.CredentialStore credStore = jpsCtx.getServiceInstance(oracle.security.jps.service.credstore.CredentialStore.class);
oracle.security.jps.service.credstore.PasswordCredential cred = (oracle.security.jps.service.credstore.PasswordCredential)credStore.getCredential("test-cred-map", "test-cred-key");
if (cred == null) {
System.out.println("Credential not found.");
} else {
String username = cred.getName();
String password = String.valueOf(cred.getPassword());
System.out.println("Credential username: " + username);
System.out.println("Credential password: " + password);
}
} catch (Exception e) {
e.printStackTrace();
addAuditTrailEntry(e);
}
If you want a cleaner code, declare the imports in the beginning of the BPEL file (just before “partnerLinks” tag) and use the simple class names – be careful about the differences in the import statement between BPEL 1.0 and 2.0: http://docs.oracle.com/cd/E23943_01/dev.1111/e10224/bp_java.htm#SOASE87123
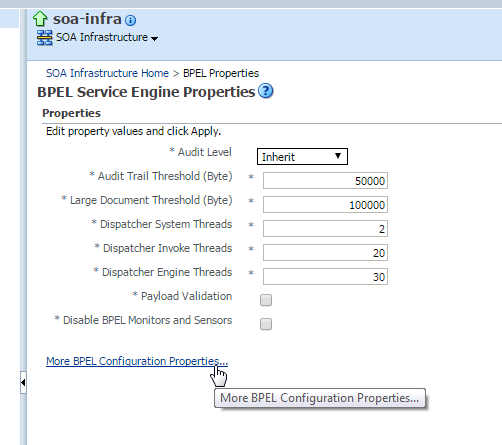
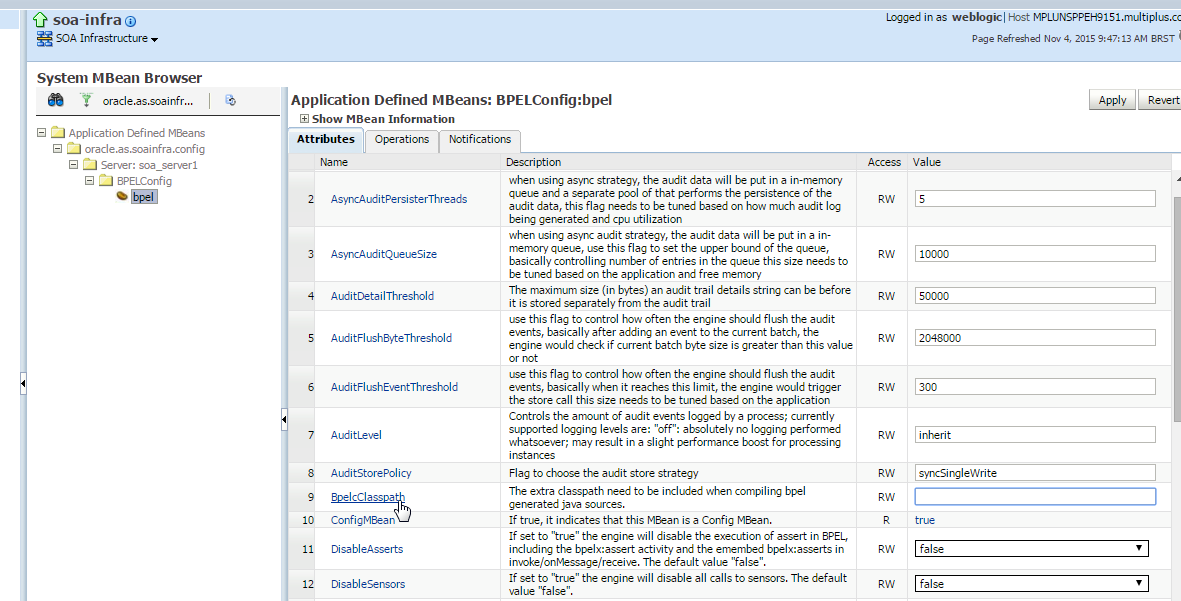
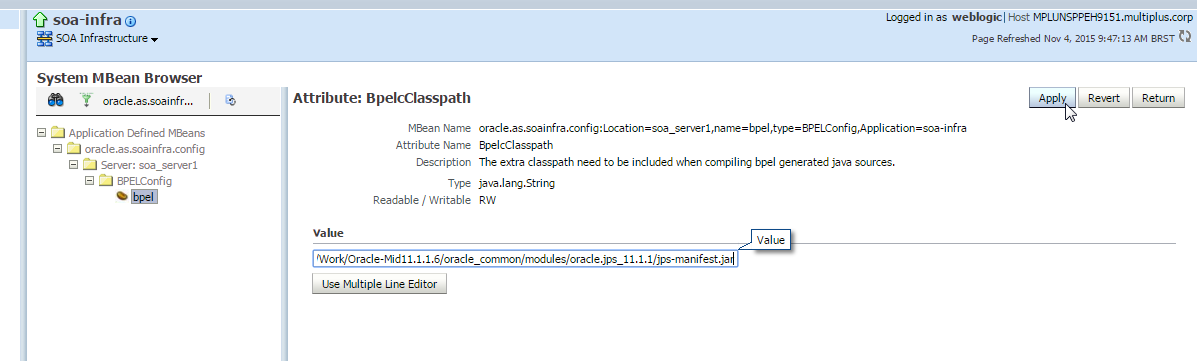
3 – Prepare the SOA environment to accept your deployment, adding the “jps-manifest.jar” file in the BPEL compilation classpath “BpelcClasspath”: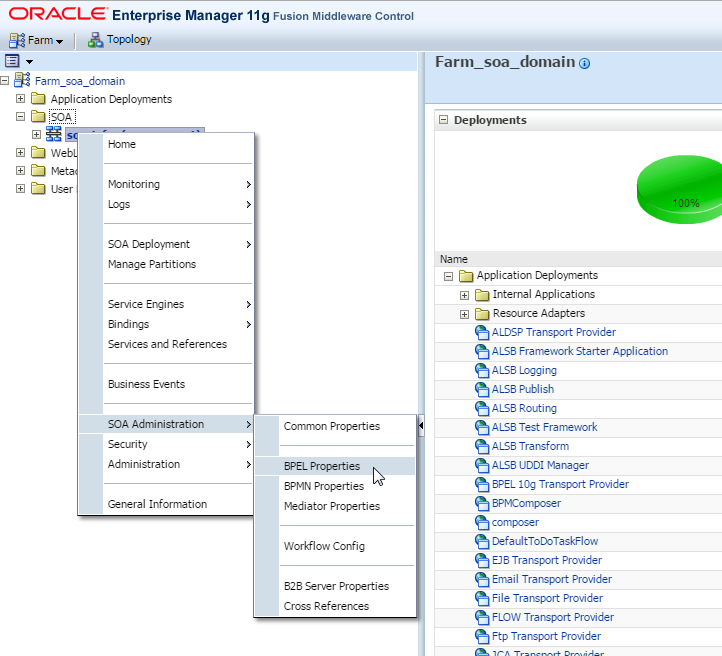
Use the full qualified path here. The common path for this library is: $DOMAIN_HOME/oracle_common/modules/oracle.jps_11.1.1/jps-manifest.jar
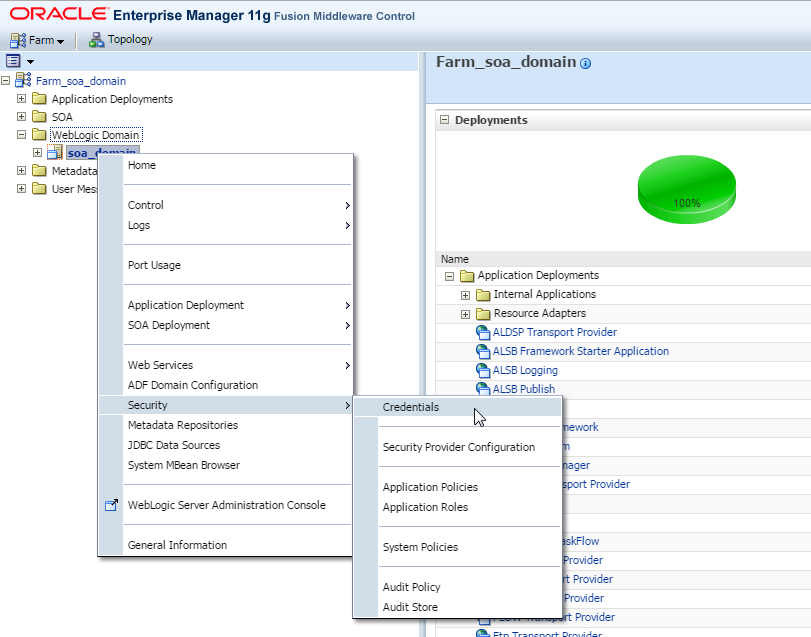
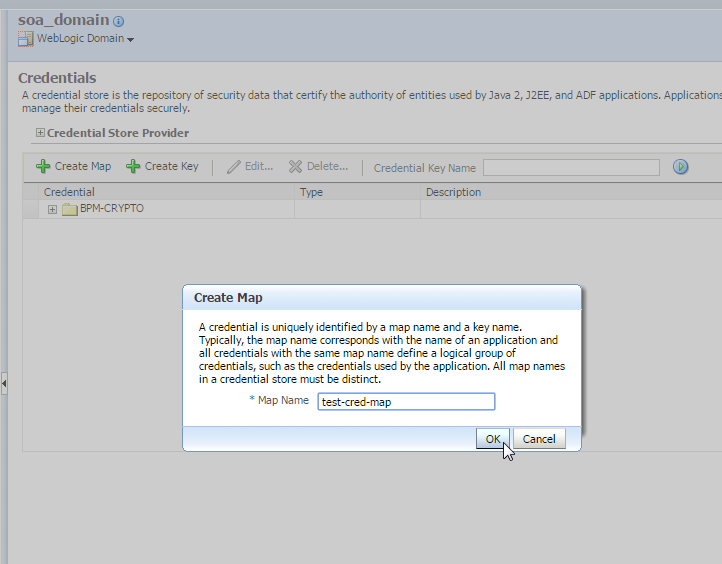
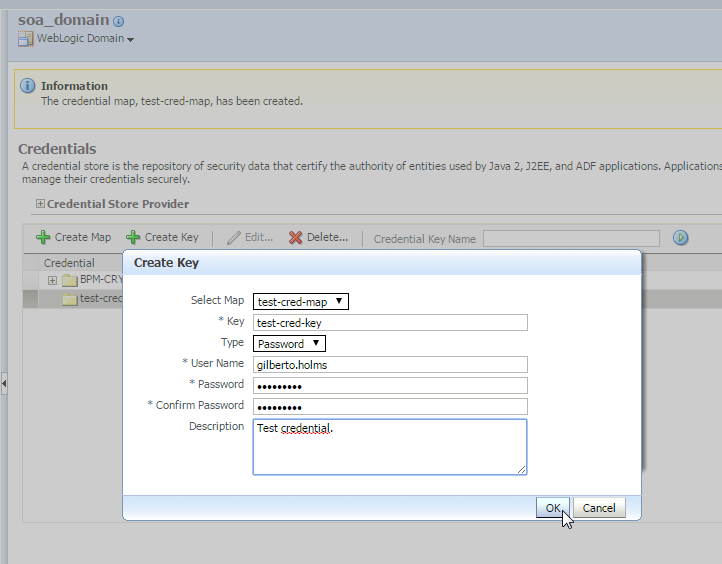
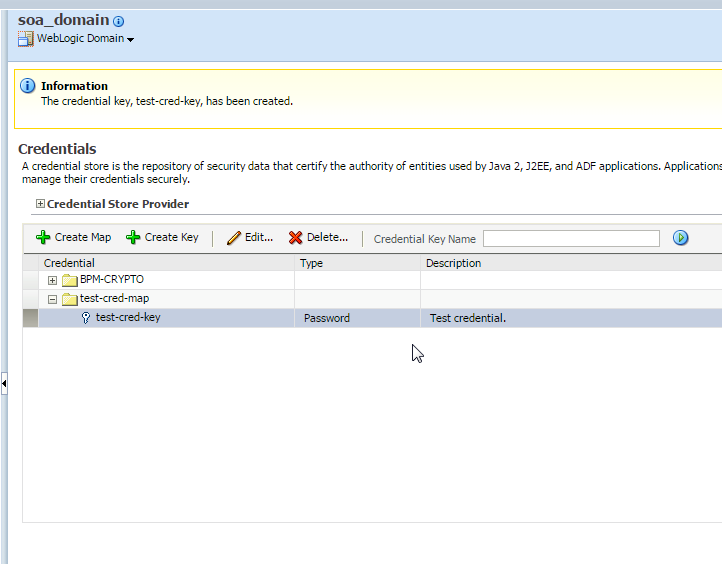
4 – Create your credential for testing the code:
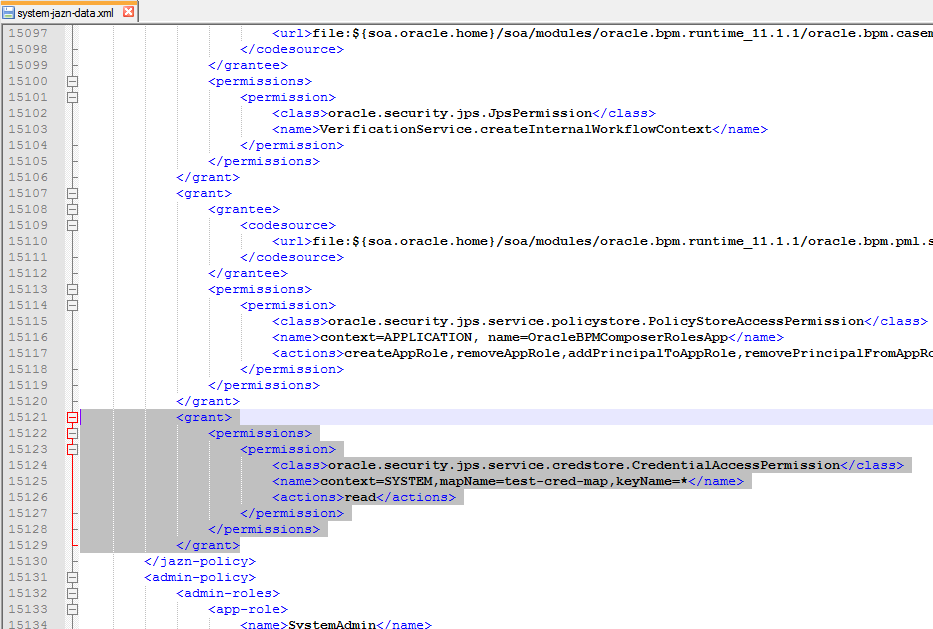
5 – Grant permission for your custom code to access your credential map and keys:
5.1 – Edit “system-jazn” file: $DOMAIN_HOME/config/fmwconfig/system-jazn-data.xml
5.2 – Add a grant permission, appending the following tag to the end of “jazn-data/system-policy/jazn-policy”:
<grant>
<permissions>
<permission>
<class>oracle.security.jps.service.credstore.CredentialAccessPermission</class>
<name>context=SYSTEM,mapName=test-cred-map,keyName=*</name>
<actions>read</actions>
</permission>
</permissions>
</grant>P.S.: omitting the “grantee” tag, any deployed code will get access to the credential map.
6 – Restart both Admin and Managed Servers so “system-jazn” update can take effect;
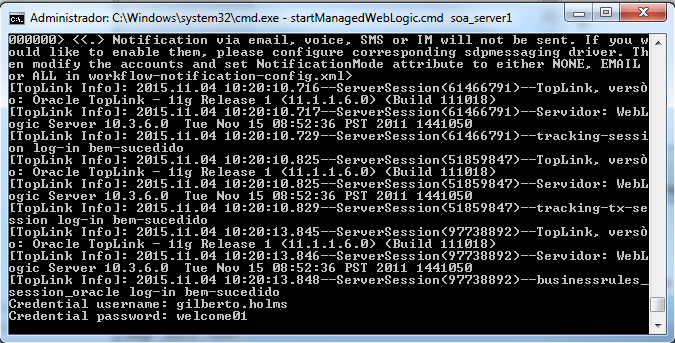
7 – Test your code and see the magic:
The approach shown in this article can be adapted to be used in other FMW technologies, like inside Service Bus (through a “Java Callout”) or some JavaEE application deployed on the WebLogic server.
Published at DZone with permission of Gilberto Holms. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments