Row Level Security in Hyperlambda and SQL
Row level security in Hyperlambda and SQL is a declarative feature when generating your CRUD backend. One simple dropdown list, and it’s done!
Join the DZone community and get the full member experience.
Join For FreeWe’ve always had row-level security in Hyperlambda. However, as of today, row-level security in Hyperlambda and SQL is a declarative feature when generating your CRUD backend. Look at the below screenshot to understand.
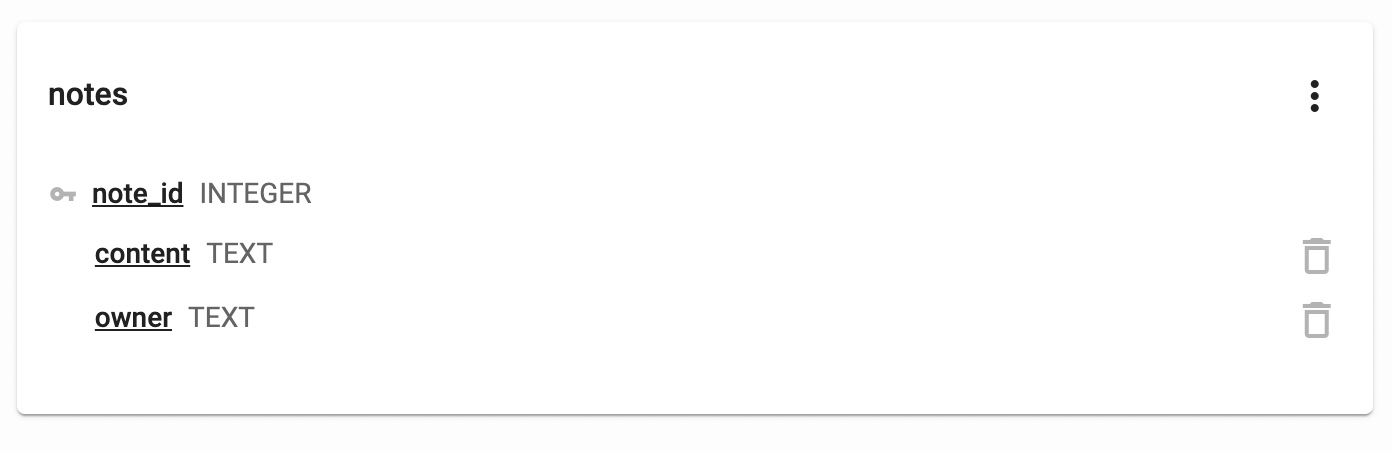
The above is a simple table I added to the Aista CRM plugin using SQL Studio. The idea is to have a single table where each user can store notes for later. The “owner” field is the username of who’s note the particular record belongs to. No users should have access to other users’ notes. This idea is called “row level security”. If you reproduce the above database table in SQL Studio then go to the CRUD Generator, and select your database and table, you’ll see something like this if you expand the “owner” column.
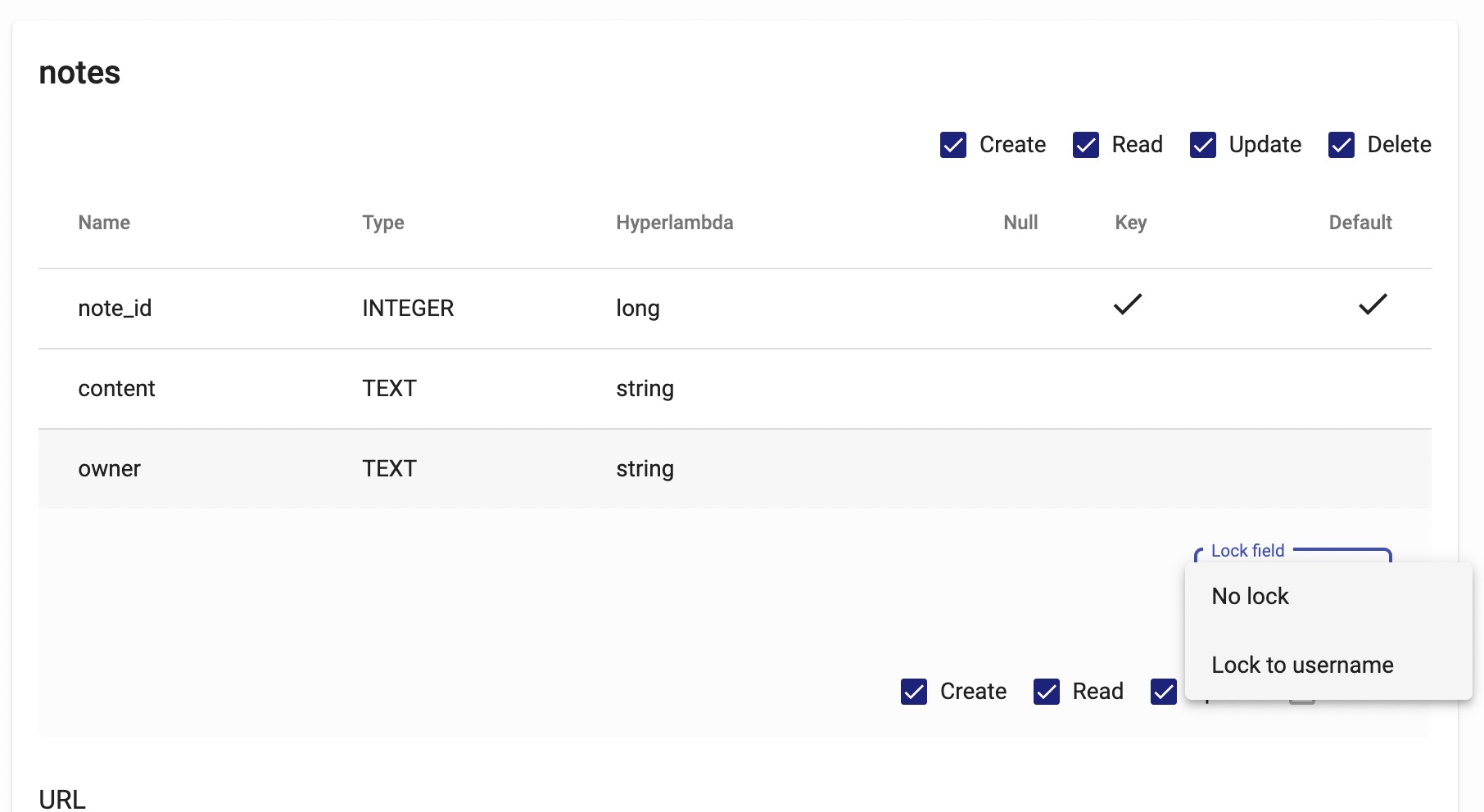
The above dropdown list allows you to “lock” your field to the username of the authenticated user. This feature will automatically generate all the code required to ensure row-level security on all CRUD operations. Creating records will automatically “inject” the username. The read will only return records belonging to the user. An update will only allow for updating records belonging to the user. And delete till only delete records belonging to the user.
This is a highly useful feature, and the CRUD Generator simply takes care of everything automatically for you. No coding is required from your side.
How Does It Work?
I must have said this a million times before, but it’s impossible to create something resembling our CRUD Generator without a meta-programming language. My reasons for repeating this, are because the first question people ask me when they see Aista Magic Cloud is; “Why didn’t you use PHP or Python? Why this ‘Hyperlambda’ thing?”
My answer is always the same; “It’s not possible without a meta-programming language. As far as I know, Hyperlambda is the only modern meta-programming language in existence.”
The reason is that the tiny dropdown list thing you see in the above screenshot will actually “dynamically inject” Hyperlambda code into a “Hyperlambda template”. This is only possible if you can treat code the same way you treat data. Implying you allow for querying the code semantically, to understand how it works. This process resembles the same process you’re following as you’re injecting HTML elements into your DOM. HTML is a “semantic” language, meaning it’s got no “compilation” occurring. Fundamentally HTML is simply a tree structure. Hyperlambda shares this trait with HTML, it’s just a tree!
This allows the CRUD Generator, and other concepts for the record, to semantically inspect the Hyperlambda, and dynamically inject additional snippets at the correct place, according to your instructions.
Doing this with PHP, Python, C# or Java is not even possible in THEORY!
Below is the SQL necessary to recreate the above table in SQL Studio for your reference.
CREATE TABLE notes(
note_id integer not null primary key autoincrement,
content text not null,
owner text not null
);Published at DZone with permission of Thomas Hansen. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments