4 Ways to Control Access to Spring Data REST
This article looks at four ways to allow or restrict access to Spring Data REST using RepositoryDetectionStrategies methods.
Join the DZone community and get the full member experience.
Join For FreeThis post looks at four ways to control access to Spring Data REST using RepositoryDetectionStrategies.
This post forms part of a series looking at Spring Data REST –
- Introduction to Spring Data REST
- Spring Security and Spring Data REST
- Securing Spring Data REST with PreAuthorize
RepositoryDetectionStrategies
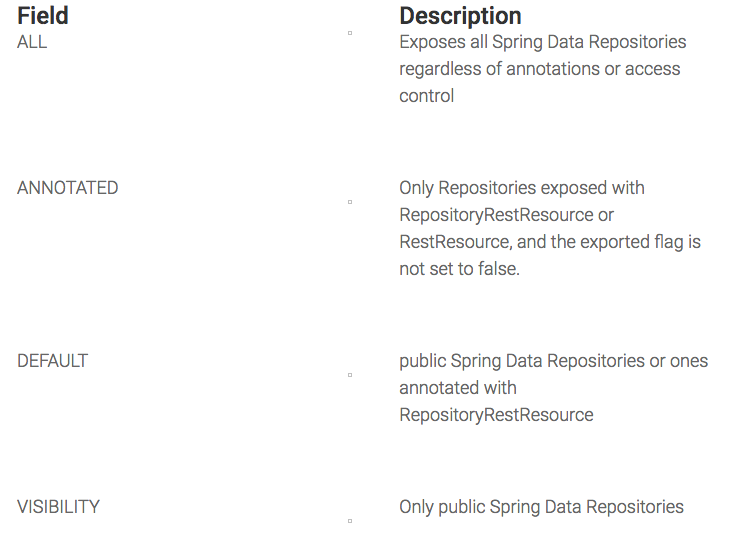
You can control access to Spring Data REST using the four RepositoryDetectionStrategies:
Source Code
- https://github.com/farrelmr/introtospringdatarest/tree/5.0.0
- https://github.com/farrelmr/introtospringdatarest/releases/tag/5.0.0
You can run the examples with
mvnw spring-boot:runExamples
I've created a Spring Rest Configuration class for this example:
@Component
public class SpringRestConfiguration extends RepositoryRestConfigurerAdapter {
@Override
public void configureRepositoryRestConfiguration(RepositoryRestConfiguration config) {
config.setRepositoryDetectionStrategy(RepositoryDetectionStrategy.RepositoryDetectionStrategies.DEFAULT);
}
}All of the examples will be changing the enumerated value of RepositoryDetectionStrategy.RepositoryDetectionStrategies, and testing what REST endpoints are exposed.
I have also annotated one of our Spring Data Repositories:
@RepositoryRestResource
@PreAuthorize("hasRole('ROLE_USER')")
public interface ParkrunCourseRepository extends CrudRepository<ParkrunCourse, Long> {
@Override
@PreAuthorize("hasRole('ROLE_ADMIN')")
ParkrunCourse save(ParkrunCourse parkrunCourse);
}RepositoryDetectionStrategies.default
A default setting RepositoryDetectionStrategy detects public interfaces annotated with RepositoryRestResource or RestResource.
So, with our example, we would expect to see both interfaces exposed as REST endpoints.
We can confirm this by calling http://localhost:8080/rest/profile –
curl -u user:user -X GET http://localhost:8080/rest/profile
{
"_links" : {
"self" : {
"href" : "http://localhost:8080/rest/profile"
},
"secrets" : {
"href" : "http://localhost:8080/rest/profile/secrets"
},
"parkrunCourses" : {
"href" : "http://localhost:8080/rest/profile/parkrunCourses"
}
}
}
RepositoryDetectionStrategies.annotated
Annotated will only detect interfaces annotated with RepositoryRestResource or RestResource, and an exported flag that is true(default). In our test case, we would only expect to see the end point for ParkrunCourseRepository to be exposed, as it is annotated with @RepositoryRestResource.
We can test and confirm this –
curl -u user:user -X GET http://localhost:8080/rest/profile
{
"_links" : {
"self" : {
"href" : "http://localhost:8080/rest/profile"
},
"parkrunCourses" : {
"href" : "http://localhost:8080/rest/profile/parkrunCourses"
}
}
}RepositoryDetectionStrategies.visibility
VISIBILITY will only detect REST and expose repertories based if they are publicly exposed.
Let's make a change to SecretRepository to leave the interface with default visibility –
interface SecretRepository extends CrudRepository<Secret, Long> {
}We would not expect to see this end point, and would only expect to see the ParkrunCourseRepository end point. This is confirmed when we call the rest/profile –
curl -u user:user -X GET http://localhost:8080/rest/profile
{
"_links" : {
"self" : {
"href" : "http://localhost:8080/rest/profile"
},
"parkrunCourses" : {
"href" : "http://localhost:8080/rest/profile/parkrunCourses"
}
}
}RepositoryDetectionStrategies.all
Finally, if we use RepositoriesDetectionStrategies.ALL with SecretRepository at default access, then we would expect to see both the parkrunCourses and Secret’s end point. All will also expose endpoints that have an exported false attribute.
Restart the server and test –
curl -u user:user -X GET http://localhost:8080/rest/profile
{
"_links" : {
"self" : {
"href" : "http://localhost:8080/rest/profile"
},
"parkrunCourses" : {
"href" : "http://localhost:8080/rest/profile/parkrunCourses"
},
"secrets" : {
"href" : "http://localhost:8080/rest/profile/secrets"
}
}
}Conclusions
This post looked at four ways to control access to Spring Data REST using RepositoryDetectionStrategies allow or restrict access to the underlying Spring Data JPA repositories. The options are – ALL, ANNOTATED, VISIBILITY or DEFAULT.
Published at DZone with permission of Martin Farrell. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments