DevOps Security Best Practices for Your SaaS Application
Discover the top ten best practices for securing AWS DevOps in this blog. These practices can be applied not only to AWS but also to other cloud environments.
Join the DZone community and get the full member experience.
Join For FreeDevOps security is a set of practices that integrate security processes, people, and DevOps security tools into the development pipeline, enabling organizations to deliver software in a secure environment continuously. Whether you call it DevSecOps, network security, cyber security, DevOps and security, security compliance, or just hardening the cloud infrastructure, security is a critical component in today's dynamically changing cloud environments. This blog covers the top ten AWS DevOps security best practices. That said, these practices apply to other cloud environments as well.
Different Types of IT Security
Information technology security can be classified into the following types:
- Information Security: A process of protecting information against unauthorized access, cyber-attacks, and malware.
- Hardening IT: A security measure that reduces the surface of system vulnerabilities.
- Penetration Testing: A security method that simulates a cyber attack on a system in order to identify any exposed vulnerabilities.
- Vulnerability Assessments: A systematic review of a system's security weaknesses.
- DevSecOps: A method that integrates security with development and operations teams, thus sharing security responsibility throughout a product's lifecycle.
Where Does DevOps Security Come Into Play?
DevOps combines developers and operations teams to coordinate and contribute to software development projects seamlessly. When this methodology was first launched in 2008, many organizations were apprehensive about adopting it due to a lack of proper understanding of the concept. DevOps means different things to different people. However, now that businesses have started noticing the amazing results of DevOps-enabled organizations, they are aggressively embracing it. Today, DevOps integrates every department into cross-functional teams making every team member responsible for the entire lifecycle of an application or service. AWS Security DevOps practices are about integrating security into the CI/CD pipeline.
Now, without further ado, here are the top ten AWS DevOps security best practices applicable to organizations of all sizes and natures and the DevOps security tools you need.
Which Are the DevOps Security Best Practices?
1. Hardening Your IT Resources
Hardening IT resources is the process of securing IT resources by identifying and mitigating vulnerabilities in configuration, design, implementation, and administration with the objective of making them hack-proof. By reducing the attack surface, administrators can minimize potential flaws hackers exploit. In addition to providing a higher level of security, hardening your systems improves system functionality and simplifies audit and compliance tasks.
First, you must secure your operating system and Nginx/PHP servers. If you're using containers, secure everything within the container. For a cloud instance, secure the software and services running inside the instance. When special services are used, such as Jenkins, secure them as well.
- Server and OS: Besides a strong password policy, multi-factor authentication, and AES encryption, we recommend applying the latest updates and patches from the OS developer and enabling security features. Other methods include privilege-based access, restricting peripherals connected to the server, host drive encryption, secure boot, biometrics, updating drivers, and deleting unnecessary ones. Whether you use LAMP (Linux – Apache HTTP Server – MySQL – PHP ) or MERN (MongoDB – ExpressJS – ReactJS – NodeJS), make sure to secure all servers, apps, and services involved in the project.
Securing your JavaScript is crucial. Cross-Site Scripting (XSS) is a common security vulnerability in JavaScript environments. Cross-Site Request Forgery (CSRF) is another important vulnerability that should be addressed. In addition, do your best to eliminate browser plugin code vulnerabilities, sandboxing issues, and client-server trust relationship issues. When it comes to Node.js, check for Command Injection and SQL Injection issues.
Most common attacks on Linux systems happen on an unsecured kernel. Even though the kernel possesses an in-built defense system, it's important to effectively secure the kernel by frequently applying security patches, enabling secure boot Full or Thorough Mode, implementing kernel module signing and loading rules, enabling kernel lockdown, hardening the Sysctl.conf file, etc. You also need to implement strict permissions and perform ongoing monitoring.
- Network: Network hardening includes firewall configuration and firewall security with iptables or ufw, network traffic encryption, removal of unnecessary services, protocols, open ports, access lists, and secure remote access points. Moreover, network segmentation is highly recommended. Network segmentation is about breaking down a network into multiple subnets or segments such that these smaller networks can be monitored using granular policies. A public subnet can be accessed from the Internet gateway, while a private subnet isn't accessible from the Internet. You should place your databases and Redis servers in the private subnet and all other resources in the public subnet. Using virtual private networks for sensitive traffic is recommended.
Also, Secure Socket Shell (SSH) enables public-key-based authentication and facilitates encrypted connections between two endpoints in a network. Generating SSH keys to access containers and servers is highly recommended. Sometimes, Cpanel and Bitnami deploy multiple third-party software/services that aren't needed. This is why we do not recommend deploying your SaaS applications with graphical admin interfaces like Cpanel, WHM, bitnami, and Plesk. Finally, Fail2ban is a powerful IPD framework that can help you mitigate bot attacks.
- Containers: When it comes to container security, restrict network port accessibility, limit the image size and build data and use network segmentation to deploy containers in different subnets based on the data they operate. Try executing one process per container. Furthermore, be careful when sharing host namespaces, and make sure to limit containers from acquiring new privileges.
2. Add a CDN Firewall Such as Cloudflare to Mitigate Common DDoS Attacks
A content delivery network (CDN) helps you accelerate your application delivery speed, deliver content faster, and increase your SaaS application performance. Cloudflare is a popular CDN that offers globally-distributed servers to improve application performance with reduced load times. As static files are cached and served from the nearest location, Cloudflare facilitates superior app performance. A notable feature is the developer mode, which lets you turn off the caching option when making changes to your application. CDN Cloudflare is free, easy to set up, and integrates seamlessly with existing infrastructure.
Cloudflare CDN also has a security functionality, which acts as an intermediary between the end-user and applications and thereby mitigates common DDoS attacks and malicious web attacks, combining DevOps and security.
With data centers in 250 cities across 100 countries, Cloudflare offers a massive network scale that is five times more performant than its competitors and bigger than any DDoS attack. This means Cloudflare operates your applications in a secure environment wherein the majority of cyber-attacks are obstructed at the name-server level, thus protecting your applications from comment spam, DDoS attacks, and SQL injections. Blocking out malicious and unwanted traffic allows you to save on bandwidth. What makes Cloudflare unique in comparison to other CDNs is that its bandwidth has no limit, unlike Amazon Cloudfront or other CDNs, which charge you based on bandwidth.
Cloudflare offers useful apps that help you deliver a superior user experience. Moreover, the in-depth analytics features provide clear insights into website performance. With CDN, Web Application Firewall, and DDoS, Cloudflare is a comprehensive platform that runs your applications in a secure environment with optimal performance. The free version allows you to use the CDN and other interesting features. On the other hand, upgrading to a paid version allows you to leverage the web application firewall feature.
3. AWS Security
While AWS offers various DevOps security tools, identity, and compliance, it's important to protect your workloads with identity theft protection, data, and user accounts by implementing AWS DevOps security best practices.
- Limit access to AWS resources for systems and users who strictly require access using the Identity and Access Management (IAM) system. An IAM system comprises users, groups, roles, credentials, and policies. Applying policies to groups instead of individual users allows you to manage security while gaining network operations visibility quickly.
- A root user is the user who created the AWS account and the email associated with it. As such, the root user has more privileges than an administrator and can make or break the entire system. Therefore, only use the root user account in exceptional circumstances. Furthermore, make sure to use a strong and complex password and multifactor authentication and delete the root user access keys.
- When you use access keys instead of IAM roles, ensure that the access keys are regularly rotated, at least every three months, using the IAM credentials report.
- Amazon Key Management System (KMS) is a fully-managed encryption tool offered by AWS that helps you efficiently manage keys for AWS resources.
- An AWS security group is a virtual firewall that controls the outbound and inbound traffic for EC2 instances. AWS virtual private clouds come with a default security group. Depending on the protocols and ports, you can add policies and rules to each security group that governs the entire VPC or certain resources within the VPC. Security groups are stateful, which means when specific inbound traffic is allowed, the corresponding outbound traffic is also allowed by default.
- Multi-factor authentication is an easy way to protect your devices from unauthorized access. Ensure that the AWS console, a web app enabling you to manage AWS resources, is MFA-enabled.
- To securely connect to on-premise, remote, and client devices, use the AWS Virtual Private Network (VPN) solutions, which are available in two forms: AWS Client VPN and AWS Site-to-Site VPN. While the client VPN connects end users with AWS resources, AWS Site-to-Site VPN connects Amazon VPCs with your network.
4. Host and Network Firewall
A firewall shields your device and network to protect them from malicious or unwanted traffic. They can be configured to block specific apps, data, ports, and locations based on IPs and more. Firewalls can be hardware devices or software programs.
Network Firewall
A network firewall is installed between the Internet and the protected LAN for the purpose of filtering traffic. Network firewalls are mostly hardware devices. A notable network firewall is Amazon Security Group.
Amazon Security Group
It is a virtual firewall that filters traffic to your AWS resources. When a virtual private cloud is created, AWS creates a default security group. You can configure the security group to protect each VPC or each resource in the VPC. The traffic is filtered based on port numbers and protocols. Amazon Security Group also helps you control traffic to your cloud network, specifically to EC2 instances.
Host Firewall
A host firewall is typically a software program that is installed on the host machine and protects the individual host device. Host firewalls offer mobility but are difficult to scale. That said, setup is easy. We recommend having a network firewall and a host firewall as a second level of defense.
IPtables is a Linux firewall that enables administrators to filter malicious and unwanted traffic and redirect packets to alternate ports and IPs while protecting the system against DDoS attacks. Iptables is a Linux firewall that provides the lowest level of access to the Linux kernel, thus making it the most reliable and robust firewall on the market. This utility is very versatile and can easily be configured and controlled from the command line. While the rich feature set is an advantage for advanced users, beginners will have to go through a learning process. Iptables have been deprecated; however, the underlying netfilter is still in operation, and the user interface for the Netfilter is now offered as nftables.
UFW, or uncomplicated firewall, is another Linux firewall that is built on iptables but simplifies iptables usage complexities. You definitely need a deep knowledge of TCP/IP and expert knowledge of the kernel to use iptables effectively. UFW makes it easy to configure and use firewalls. ConfigServer Security and Firewall is a server security firewall that controls server traffic, tracks network connections and prevents DDoS attacks. It can be easily managed via a web interface or a secure shell.
CFW or Convergent Firewall is a comprehensive product that combines multiple converged security solutions, including a secure web gateway, a data center firewall (DCFW), a Gi/SGi integrated with Carrier Grade NAT (CGN), and DDoS, an IPSec site-to-site VPN with a centralized management console that efficiently manages SDN, as well as Cloud and NFV environments. That said, it comes with a price tag.
5. Intrusion Monitoring System / Threat Intelligence System
Intrusion Detection System (IDS)
It is a network security solution that assists administrators in detecting network vulnerabilities. It listens to traffic and reports the results to administrators. On the other hand, an Intrusion Prevention System (IPS) takes things one step further by not only detecting malicious network attacks but also preventing them.
Moreover, a threat intelligence system gathers information about known threats and possible cyber attacks to analyze and build effective mechanisms to help organizations effectively combat and mitigate these threats. The IDS/IPS security tools can use this information to identify and block traffic from any specific source, such as an IP address.
Amazon GuardDuty
It is an intelligent threat detection service from AWS which offers organization-wide visibility into suspicious activities and malicious traffic. This IDS tool continuously monitors your AWS accounts and workloads and automatically triggers responses when a threat is detected, thus helping you mitigate threats as soon as possible.
Wazuh
It is a popular, highly scalable open-source security tool that combines Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) functionalities to detect and prevent most types of threats quickly. Furthermore, Wazuh is free to use and comes with a rich feature set, including vulnerability detection, intrusion detection, incident response, security analytics, log data analysis, file integrity monitoring, configuration assessment, regulatory compliance, and more. Indeed, Wazuh allows you to use a single tool for ID/IPS and threat intelligence tasks. It also integrates easily with third-party solutions. As such, small and medium-sized organizations can highly benefit from the cost savings that come with Wazuh.
AWS CloudTrail
Although not an intrusion detection system, AWS CloudTrail is a log-recording and API call monitoring service by Amazon. It can be configured to work with SIEM and XDR tools, therefore making audit and compliance easy and effective.
If your organization uses AWS, we recommend using GuardDuty and CloudTrail. If your organization doesn't use AWS, Wazuh is a good choice. You can also use Elastic Stack (ELK), which comes with ElasticSearch, Logstash, and Kibana.
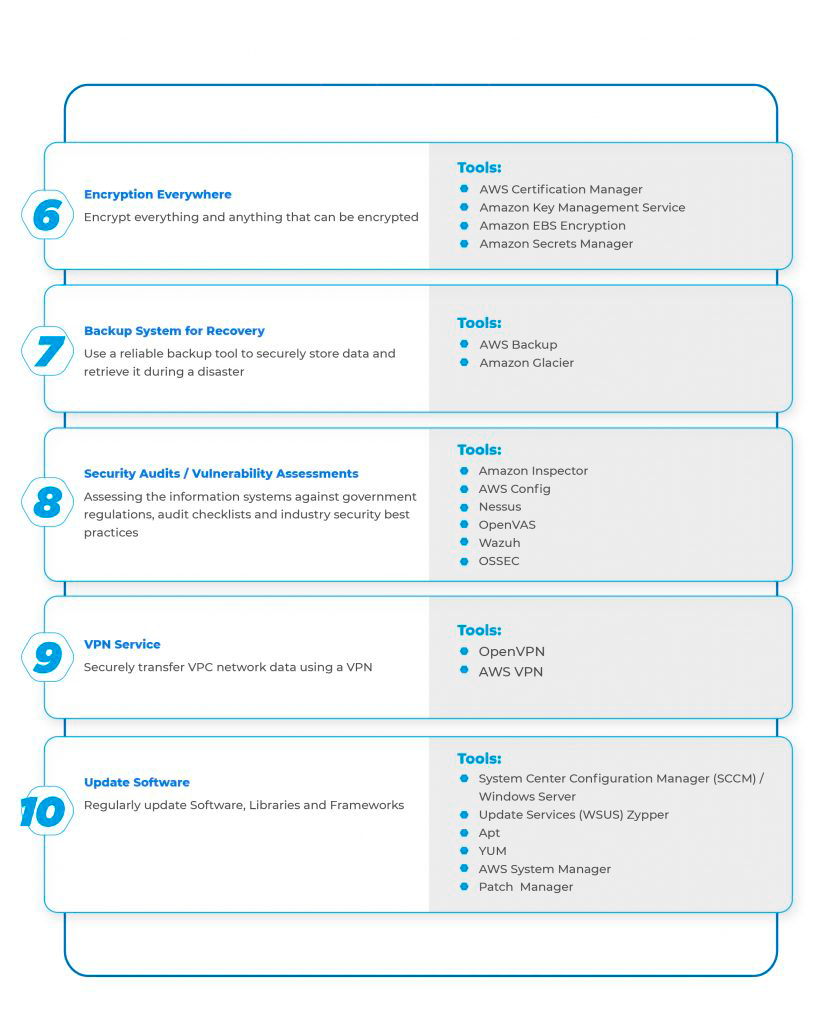
6. Encryption Everywhere
These days, encryption is no longer an option but rather a necessity. The idea is to encrypt everything and anything that can be encrypted. When it comes to website encryption, we recommend using HyperText Transfer Protocol Secure (HTTPS). HTTPS is an extension to the regular HTTP protocol wherein the Transport Layer Security (TLS) protocol is used to encrypt the communication protocol. Firstly, you must identify all API calls, services, and web servers hosted in the cloud, a remote location, or on-premise that should be encrypted and obtain relevant certificates from a commercial certificate authority, for example, Comodo Code Signing. Secondly, install the SSL certificates, configure HTTPS encryption, and enable web servers to use HTTPS. In addition, be sure to administer and monitor encrypted websites continuously. Encrypt ports range from 80 to 443.
AWS Certificate Manager (ACM)
It is another handy tool from Amazon that governs the complex tasks of creating, storing, deleting, and managing private and public SSL/TLS certificates for your AWS resources. You can import certificates into the ACM system from third-party sources or have them directly issued from the ACM.
Amazon Key Management Service (KMS)
It is a tool designed to create, delete and manage cryptographic keys across all AWS services used in the infrastructure. It offers a centralized dashboard that defines and controls usage policies from a centralized view. AWS KMS can be accessed via the KMS CLI, SDK, or AWS IAM dashboards. Moreover, it's a fully-managed service, which means AWS handles security, maintenance, and infrastructure availability. Also, KMS uses the envelope encryption method wherein a data key is used to encrypt data and resources while a customer master key (CMK) is stored in AWS. Both keys are required to decrypt data.
For an optimal level of Security DevOps practices, be sure to implement the methods below:
- To ensure greater protection for logs, encrypt log files such that hackers won't be able to edit them without the encryption key. Without the key, hackers can only delete the log file, which can easily be noticed by the administrators. For encryption purposes, you can use CloudWatch, which encrypts log group data by default, or Amazon KMS to encrypt log data.
- Use Amazon EBS encryption to encrypt the EBS resources of your EC2 instances. It uses Amazon KMS to automatically encrypt volumes and snapshots during the creation stage and manage them. It also allows you to define custom encryption policies.
- Amazon Secrets Manager is a powerful service that manages your secrets, API keys, and database credentials throughout their life cycles. It allows you to access data using fine-grain policies, safely rotate secrets, and centrally audit, all while only paying for the number of secrets managed in the system.
- Always encrypt API calls. Ensure that all data traveling between the API server and the user is encrypted. For REST APIs that use HTTP protocol, you must implement the TLS protocol to encrypt REST API communications and web pages.
- Lastly, encryption is required in order to comply with government regulations. For instance, the Health Insurance Portability and Accountability Act (HIPAA) requires Protected Health Information (PHI) and ePHI to be encrypted when you save such data on a USB drive, hard disk, or in the cloud. For PCI DSS compliance purposes, AES is the preferred method of encryption.
7. A Backup System for Disaster Recovery
Disaster recovery does not fall into the DevOps security category. However, it helps with protecting and preserving data. AWS Backup is a perfect place to centralize data management and automate data protection across all AWS services in the infrastructure. It's a fully-managed and user-friendly service that allows you to easily back up all types of data from a single pane. The data is stored in S3 buckets by default. You can also easily define backup policies and retention periods depending on your workload requirements. Finally, AWS Backup automates the entire process for all services with backup policies for each service. All of this being said, the only downside is that you are required to pay for the cost of snapshot storage.
In addition to the above, EFS data can be moved to cold storage. Amazon Glacier is a low-cost data backup and archiving service that's great for cold storage. It allows users to store unlimited data and retrieve it within three to four hours. AWS securely stores this data using 256-bit advanced encryption and regularly monitors data to ensure data integrity. Furthermore, seeing as data is stored in multiple facilities, data redundancy is guaranteed.
Next, let's talk about snapshots. First off, it's important to note that snapshots are different from backups. Elastic Block Store (EBS) is a point-in-time snapshot that references data stored in the storage volume while the backup performs write activities to the live storage volume. It is a read-only snapshot that helps admins restore data when need be. Automated EBS snapshots also permit you to capture backup at the same point in time which allows for crash consistency.
When it comes to backing EC2 instances, AWS offers multiple options. EBS volume is a block-level storage device that acts as a physical hard drive when attached to an EC2 instance. EC2 instances use EBS volume by default for persistent storage.
Another solution is to implement Infrastructure as Code (IaC), wherein the infrastructure is managed via scripts stored in a central repository. Terraform and CloudFormation are the two most popular IaC tools available on the market. When the infrastructure is managed as code and stored in a repository, using Bitbucket, GitHub, or AWS Code Commit will grant you the luxury of versioning the infrastructure. As such, not only can you automate infrastructure provision, but you can also instantly relaunch a previous version of deployment in the event of a disaster.
8. Security Audits – Vulnerability Assessments
A security audit is a process of assessing the information system of an organization against audit checklists, government regulations, and industry security best practices. The audit covers the software, applications, physical components, network vulnerabilities, and how employees collect and manage data. As a general rule, it is recommended that you audit your cloud infrastructure, as well as vulnerability assessments and misconfigurations in your applications and infrastructure, at least once every quarter.
Amazon Inspector
It is a popular automated vulnerability management tool that was launched by Amazon in 2015. It continuously scans AWS workloads to identify and quickly resolve security issues. In 2021, the tool was relaunched with a new architecture in order to accommodate a wider range of resource types and support massive deployments. The new tool integrates easily with AWS Security Hub, Event Bridge, and container-based workloads. It automatically discovers EC2 instances and ECR-based container workloads and assesses the security status.
Moreover, when a workload configuration change occurs, it automatically rescans the image. Amazon Inspector comes with a configuration scanning and activity monitoring engine and a built-in content library of reports and rules. Finally, it can be configured through an API enabling security implementation in DevOps environments.
AWS Config
It is another handy tool for inventory management and asset tracking in cloud-based AWS environments. This tool helps administrators identify why a resource or service isn't working properly. It uses Amazon SNS to notify admins of configuration changes along with the details of the IP address and the person requesting the change. You can check the recorded historical resource configurations using a CLI, SDK, or AWS management console. When integrated with AWS CloudTrail, AWS Config lets you gain deep insights into API calls.
Concerning vulnerability scanning, Nessus and OpenVAS are two popular security tools that lock horns. Nessus is a vulnerability scanner developed by Tenable Inc. The tool was launched in 1998 as a free remote security scanner. However, Tenable Inc. became the owner of a proprietary license and changed the license to proprietary in 2005. Not only does Nessus detect vulnerabilities by searching for 47000+ Common Vulnerabilities and Exposures (CVEs) with minimal false positives, but it also offers suggestions to resolve them.
Furthermore, it offers built-in scan templates and real-time visibility into security posture. The tool updates the database within 24 hours. It's easy to use and offers customer support 24/7. Tenable Inc. offers a trial version for non-commercial use and a paid version for$2500 a year. It is to be noted that there is a learning curve when it comes to leveraging the advanced features of the tool.
OpenVAS is a fork in the open-source Nessus tool, which was called GNessUs before it was renamed OpenVAS. This open-source tool is free and offers great functionality in the vulnerability scanner segment. Moreover, the tool can be customized to suit your organizational security needs. The CVE coverage is around 26,000, and the tool offers extensive documentation and tutorials. That said, OS support is limited to Unix-based environments.
Next, let's take a look at which technologies work best for threat intelligence and intrusion prevention systems. First off, Wazuh is a good option. Then we have OSSEC, which is another host-based IDS system developed by Daniel B. OSSEC is an open-source tool that comes with a cross-platform architecture that enables administrators to monitor different systems from a central dashboard. The tool offers comprehensive IDS services, including rootkit monitoring, windows registry monitoring, log analysis, integrity checking, time-based alerting, and more.
9. VPN Service for Your VPC Network
A virtual private network (VPN) is a security measure that transmits data between a remote server and the end-user machine via an encrypted tunnel and thereby shields your data from hackers and unauthorized access. It also helps with safe browsing by masking the IP address and browsing activity.
AWS offers a VPN service called AWS Client VPN. It's a fully-managed VPN service that allows remote users to access AWS resources and workloads securely. It automatically scales up on-demand and offers advanced authentication features. AWS Client VPN also offers the flexibility of connecting to the cloud from any location. Finally, the high availability of AZs is a useful advantage.
OpenVPN is another popular VPN service that offers interesting features. OpenVPN is a site-to-site or point-to-point VPN service developed by James Yonan in 2001. The tool is written in C language and uses the TLS protocol and OpenSSL encryption library to facilitate secure communications in remote facilities and bridged/routed configurations.
AWS Client VPN vs. OpenVPN, Which Is Better?
AWS offers a fully-managed VPN, but it comes with a price tag of around $0.10 per endpoint and $0.05 per hour, which comes out to approximately $72 per month per device. OpenVPN is open-source and free. However, it's not a managed service. As such, you need expertise in VPN concepts and must spend considerable time installing, configuring, and managing the service. A simple mistake in this process can result in security vulnerabilities and downtimes.
Moreover, this VPN leaves it up to you to manage any scalability and availability issues. Time spent by engineers on this task should therefore be considered when choosing the best option for your organization. To reduce AWS costs, as an alternative, you can install OpenVPN on a running EC2 instance and write a Lambda trigger to verify inactive connections, remove any endpoints, and shut down the databases and other resources used by the instance in question.
10. Constantly Update Your Software, Framework, and Libraries
It's highly recommended to keep your software, frameworks, and tools always updated. The first thing you need to keep updated is your operating system. Apply patches and updates regularly. When it comes to Windows OS, Microsoft offers the System Center Configuration Manager (SCCM), which is a feature-rich tool for deploying patches to stateful servers. SCCM comes with an annual licensing fee. If you are looking for a free option, Windows Server Update Services (WSUS) may be exactly what you need.
Linux patching is easy compared to Windows. Zypper, YUM, and Apt are some of the popular patch management tools for Linux distributions. Also, Amazon offers the AWS System Manager Patch Manager, which automatically scans your Linux and Windows instances and applies patches. AWS System Manager enables administrators to view and manage the IT infrastructure on AWS. Patch Manager is a feature of System Manager that performs patch management for both operating systems and applications. It covers VMs, on-premise devices, as well as a fleet of EC2 instances, and edge devices.
You only need to pay regular EC2 instance charges for AWS SMPM; there is no additional charge. The tool uses existing Windows and Linux OS update methods and the same AWS SDKs and AWS CLI. This means you can use the same frameworks for patching that you use for automation jobs and scripts. Moreover, customized patching is supported, and you can monitor everything from a central dashboard. On the downside, AWS SMPS doesn't remediate non-patch vulnerabilities, which means you need to use security threat intelligence tools to scan and mitigate software vulnerabilities.

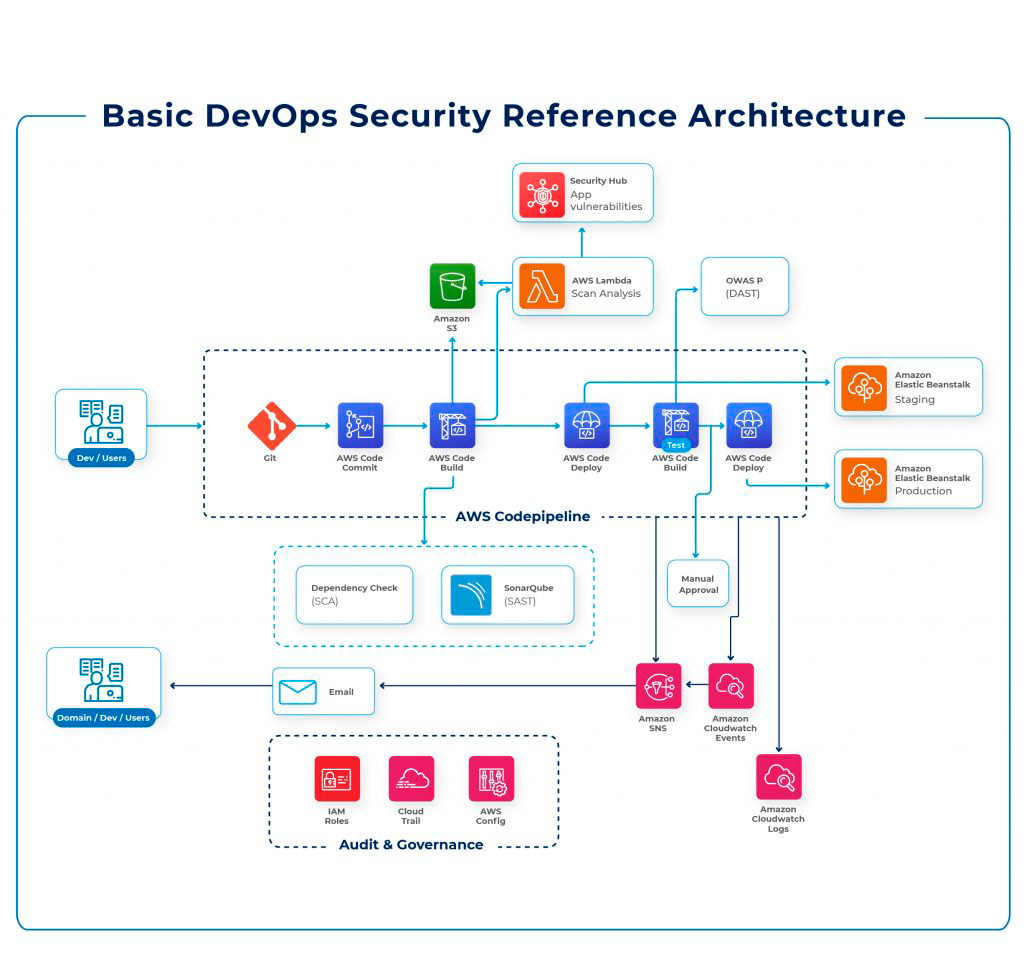
11. DevSecOps (Bonus)
Note: DevSecOps is not mentioned in the top 10 DevOps security best practices because it is a totally new paradigm and a complex concept. Not everyone business or startup can outrightly implement it. You should thoroughly understand the concept and work with a good CI/CD pipeline and the right DevOps security tools before embracing DevSecOps.
As the name implies, DevOps serves the purpose of integrating developers and operations teams so that they can coordinate and work together throughout the product life cycle. Over time, DevOps' methodology was extended to other departments. DevSecOps aims to bring security into the DevOps CI/CD pipeline, making it a shared responsibility throughout the product life cycle.
In traditional development environments, security is incorporated at the final stage of development and managed by an isolated team. However, this outdated approach is inefficient in DevOps environments wherein the software is developed in smaller units in an incremental fashion using microservices and cloud-native architectures. By integrating security to the left of the DevOps pipeline, organizations can manage infrastructure and application security from day one. When security moves to the left of the CI/CD pipeline, everyone involved in the development will share security-related responsibilities and have a sense of awareness concerning security fundamentals. Security assessments conducted early in the development lifecycle help organizations prevent vulnerabilities from appearing in production environments.
It's important to be aware that implementing DevSecOps is not an easy task. People and culture will play an important role. Modern production environments are dominated by containers that instantly spin resources up and down. Therefore, using the right DevOps security tools which support automation and integrate well with CI/CD pipelines is a challenge. When you jump into DevSecOps, you will be impressed by the amazing security benefits of the shift-left approach and face various challenges. For instance, most cyber-attacks happen in the production environment. As such, thoroughly monitoring apps in the production environment is important to mitigate zero-day vulnerabilities. Monitoring application performance delivers more insights than scanning source code. Moreover, some apps may not go through the development environment and might miss out on security scanning. This is why your shift-left approach should also consider shift-right needs.
Here are some best practices to help you implement DevSecOps:
- Security Automated Testing: Security is the key bottleneck for smaller and faster deployment. With security automation, organizations can deploy code faster and more securely. Ensure that every code change triggers a security scan that generates a report that prioritizes vulnerabilities based on the impact level. It should also trigger a ticket to the developer along with the results. Every Code commit should follow applicable security policies. Once apps run in production environments, you must continuously analyze the performance and security vulnerabilities. Synk is a developer-friendly application security testing tool developed by a Boston-based cloud security company named Synk. With Synk, organizations can easily secure code in the IDE, secure containers, connect to repos, and integrate CI/CD pipelines. It supports Java, JavaScript, Golang, Ruby, Objective-C, Python, Scala, .NET, Bazel, and PHP.
- Static Code Analysis is the practice of debugging source code before a program is executed. It's a white box testing model that offers speed and accuracy for testing by performing in-depth analysis. Checkmarx is a popular static code analysis tool developed in 2006 by Maty Siman of Checkmarx, a software company located in Ramat Gan. It detects various bugs and covers Codebashing, Infrastructure as code security testing, SAST, and IAST. Reporting is a key feature of Checkmarx, which can be easily shared with developers. Furthermore, the language support is good, and the tool is easy to learn and use. On the downside, it lacks support for Swift, and built-in rules for mobile apps could be improved.
- Dynamic Code Analysis is the practice of scanning running applications to analyze performance and security vulnerabilities. It's basically a form of black-box testing that helps organizations quickly identify production incidents and improve their overall security posture. In addition, it allows you to gain better visibility concerning app issues. Moving on, OWASP Zed Attack Proxy (ZAP) is a popular open-source tool for dynamic code analysis with a flagship status in OWASP projects. It's highly scriptable, and the automatic scanning works well and is easy to use. It comes with a Jenkins Plugin, enabling easy integration with CI/CD tasks. Other useful features include Ajax Spidering, WebSocket Testing, and Fuzzing. Moreover, you can communicate with the tool via REST APIs, and scan policy management is flexible and easy to use.
- Considering the extensive usage of containers in production environments, it's important to review container security continuously. Review the security of the container host, networking environment, and management stack, and build pipelines and applications. In addition, scan containers for malware and known vulnerabilities. Project teams' communications concerning app dependencies should be reviewed as well. Nexus Container is a developer-friendly software supply chain security platform offered by Sonatype. From build to ship and run, Nexus helps you find and fix container vulnerabilities and compliance issues throughout the container lifecycle. Furthermore, the policy engine is good and allows for defining various policy violation types. You can also block any unwanted uploads to the repos, and the software integrates well with the CI/CD pipeline.
12. Web Application Firewall (Bonus)
A Web Application Firewall (WAF) acts as a security shield between Internet traffic and the web app, enabling organizations to monitor and filter data packets. You can use cloud-based, network, or host-based WAFs installed as cloud services, network appliances, or server plugins. WAFs are mostly deployed via reverse proxies.
While WAFs are useful for every business, they are essential for organizations that process critical data. For instance, financial institutions that process sensitive card transactions can use a WAF to protect data and prevent information leakage. Moreover, WAFs help in complying with PCI CSS compliance. WAFs should be integrated with existing IDSs for comprehensive security monitoring. They come with features such as application profiling, customization of security policies, AI-based traffic pattern analysis, attack signature databases, DDoS protection, and CDNs.
AWS WAF
It is a popular cloud-native and on-demand web application firewall from Amazon. It's a stable and highly scalable solution that is flexible enough to customize WAF rules and offers basic WAF features by default. The security features can be easily integrated with existing services. Furthermore, the technical support is good. However, it's worth mentioning that the setup is slightly complicated, and AWS manages the WAF, which leaves users with minimal control over blocking.
Cloudflare WAF
It is another popular web application firewall that comes with rich features. You can configure it using APIs, and it offers good technical support. That said, documentation and integration with other services could be improved. Also, the WAF feature is only available with the paid versions of Cloudflare.
While AWS WAF is more customizable, Cloudflare offers more automation. AWS WAF best suits teams with technical expertise, whereas Cloudflare aims for mass and consumer-grade markets.
Considering the above, AWS WAF is well suited for AWS-heavy environments. On the other hand, Cloudflare's free version is good for CDN tasks, and its paid version can help with WAF tasks.
13. Enable Logging for Server, App, and Cloud (Bonus)
To improve security posture, gain better control over storage, analysis, and remediation tasks, and enable logging for servers, apps, and the cloud. By logging and monitoring API calls, organizations improve security and operational troubleshooting and comply with industry regulations and audit purposes.
AWS CloudTrail
It is a popular logging and risk-monitoring service offered by Amazon. With this tool, users can seamlessly log, monitor and analyze all activities across the AWS infrastructure using AWS SDKs, management console, program line tools, and other services. AWS CloudTrail performs well regarding security analysis, operational issue troubleshooting, compliance, and data exfiltration.
CloudTrial
It is a web service automatically enabled when a free tier is created. The centralized log data is stored in an S3 bucket, and events are delivered within 15 minutes of an API call. Best of all, CloudTrail is free, easy to implement, and offers good support, including multi-language support. However, the interface could be improved, and log analysis is complex.
CloudTrial is not to be confused with CloudWatch. While CloudWatch monitors apps and resources, CloudTrail monitors activities. CloudWatch is more popular for performance monitoring and offers higher-level monitoring of AWS apps and resources from multiple accounts. Data is retained for 15 days. Furthermore, CloudWatch offers static graphs and limited default graphs. All of this being said, it's important to optimize costs when using this service, seeing as they quickly go up as you scale.
VPC Flow Logs is a useful feature of Amazon Virtual Private Cloud that allows users to monitor and analyze IP traffic through all network interfaces within the VPC. You can publish this log data to S3 buckets or CloudWatch logs to analyze traffic to instances or identify restrictive security group rules and determine the performance and security posture of apps and the AWS environment. However, VPC flow logs cannot capture the traffic of AWS DNS services, DHCP, multiple IP addresses, and legacy instances.
Regarding application performance monitoring, New Relic and Datadog are two of the most popular DevOps security tools. Both come with an extensive ARM capability set and reporting features. However, New Relic is strong in monitoring apps, while Datadog excels in infrastructure monitoring. Both tools offer an intuitive web interface, are easy to use, and have good community support, API, and Extensibility. They also make it easy for third-party integrations and have good email security and website perimeter.
Basic DevOps Security Reference Architecture
AWS DevOps Security Framework: AWS Well-Architected
AWS Well-Architected Tool is an amazing tool from Amazon that helps organizations review their IT environments and implement architectural best practices. It's based on the AWS Well-Architected Framework and AWS-developed lenses that help you quickly build resilient, scalable, secure, and high-performing app infrastructures. You can add your questions and evaluate your workloads as per governing regulations and technology requirements. Moreover, it's free to use and comes with the AWS Management Console.
AWS's Well-Architected framework is built on the six following pillars:
1. Operational Excellence: Continuous systems, processes, and procedures monitoring.
2. Security: Protecting systems and information.
3. Reliability: Evaluating workload performance against intended functions.
4. Performance Efficiency: Structured and streamlined allocation of IT resources.
5. Cost Optimization: Optimizing costs.
6. Sustainability: Minimizing environmental impacts of workloads.
To improve DevOps security, explore the security pillar of the AWS Well-Architected framework. The security pillar focuses on best practices and current recommendations for securely designing, deploying, and managing IT workloads. It helps you improve your security posture and protect systems, assets, and data by leveraging cloud technologies.
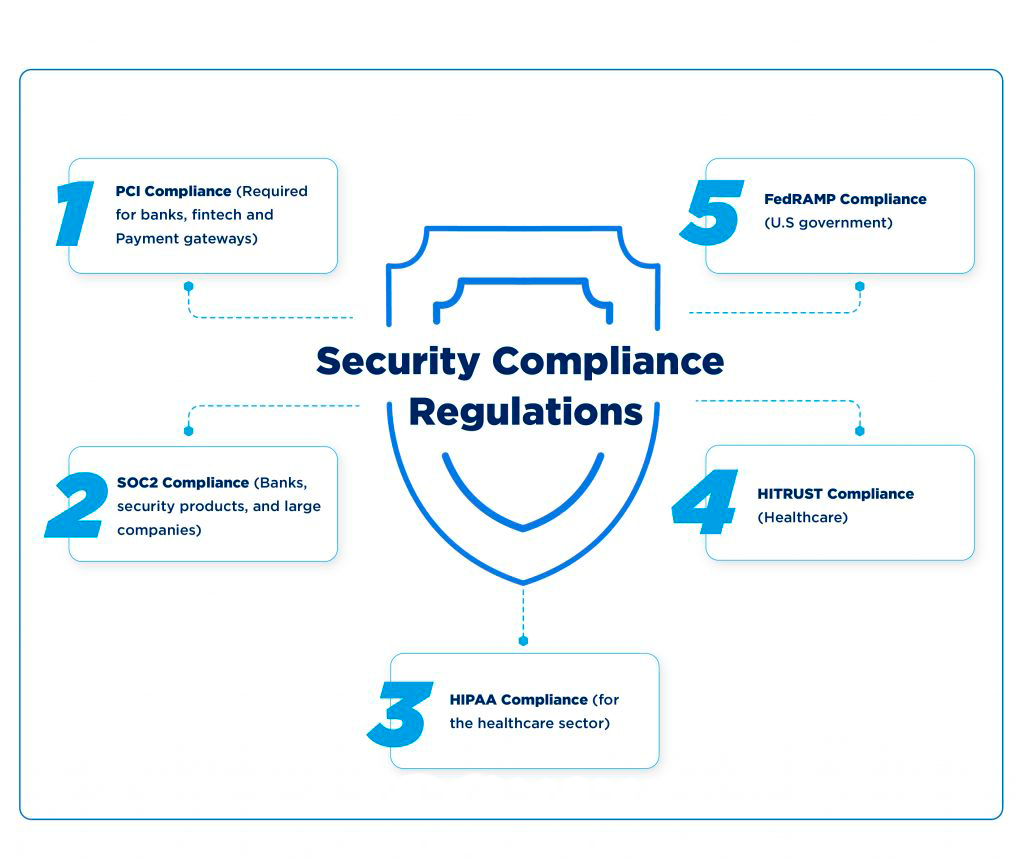
Security Compliance Regulations
1. PCI Compliance (Required for banks, fintech, and Payment gateways)
PCI compliance requires all organizations with debit or credit cards to adhere to certain regulations to ensure they operate in a secure environment. An independent body Security Standards Council (PCI SSC), comprising MasterCard, American Express, Visa, JCB, and Discover, manages and administers the enforcement of these regulations.
To comply with PCI regulations, organizations must ensure that the following requirements are met:
- Password Protection
- Firewall Protection
- Anti-Virus Protection
- Data Encryption
- Role-based Data Access
- Frequent software updates
- Physical Access restriction
- Access Logs
- Vulnerability Assessments
- Policy Documentation
For your information, AWS is a PCI DSS Level 1 Service Provider.
2. SOC2 Compliance (Banks, security products, and large companies)
SOC 2 is a security audit developed by the American Institute of CPAs that ensures a high level of information security for an organization. The audit is based on the five following trust principles:
- Security
- Privacy
- Availability
- Processing
- Confidentiality
SOC 2 compliance not only ensures that the highest information security practices are used but also gives a competitive advantage to organizations seeing as it is very trusted among consumers. However, it's a voluntary compliance standard.
3. HIPAA Compliance (for the Healthcare Sector)
The Health Insurance Portability and Accountability Act (HIPAA) is a regulatory standard that prescribes regulatory standards for the usage and disclosure of protected health information. It's enforced by the Office of Civil Rights (OCR) and regulated by the Department of Health and Human Services (HHS). HIPAA applies to healthcare providers, health insurance providers, healthcare clearinghouses, and businesses that encounter ePHI in their operations.
HIPAA regulations include:
- Policies, Procedures, and Employee Training
- Self-Audits
- Remediation Plans
- Incident Management
- Documentation
4) HITRUST Compliance (Healthcare)
Health Information Trust Alliance (HITRUST) is a standardized framework that helps organizations demonstrate compliance with HIPAA. While this framework is designed to manage data, information security, and compliance for healthcare organizations, it can also be implemented in other sectors.
The HITRUST checklist includes:
- Defining protection information
- Understanding the movement of data across infrastructures.
- Visualizing protected data volume
- Understanding the implications of data leaving the protected environment.
- Reviewing system inventory
- Documenting everything
5. FedRAMP Compliance (U.S government)
FedRAMP stands for Federal Risk and Management Program. It's a cybersecurity risk management program implemented by US federal agencies for purchasing and using cloud products and services. Organizations that intend to work with government agencies are required to comply with FedRAMP regulations.
FedRAMP's authorization and compliance requirements are as follows:
- FedRAMP Documentation and FedRAMP SSP
- Plan of Action and Milestones Development (POA&M)
- Joint Authorization Board Provisional ATO
- Continuous Monitoring Program with vulnerability scans.
FedRAMPthird party assessment (3PAO) assesses commercial cloud offerings. Moreover, AWS follows the FedRAMP process to obtain authorization for its cloud service products.
CyberSecurity Frameworks
NIST Framework
NIST stands for National Institute of Standards and Technology. The NIST framework is a set of guidelines that helps organizations mitigate cybersecurity risks. The framework core material is divided into five functions, namely Identify, Protect, Detect, Respond, and Recover. These five functions are further divided into 23 categories and 108 subcategories. To be noted: NIST is a voluntary framework.
CIS Framework
CIS stands for Center for Internet Security. It's a non-profit organization that offers a set of cybersecurity standards for IT products and services. CIS develops benchmarks as baseline configurations for ensuring security compliance when configuring IT products and services.
CIS framework benchmarks cover seven main areas:
- Server Software
- Operating System
- Multi-Functional Printers
- Mobile Devices
- Cloud Infrastructure
- Network Devices
- Desktop Software
Conclusion
DevOps, coupled with microservices and cloud-native architecture, has changed the way IT security operates. DevOps environments comprise hundreds of microservices, diverse sets of DevOps security tools, code repositories, increased levels of automation, instantly spinning containers, and shorter deployment cycles with rapidly changing configurations. This shows that more services, tools, and processes must be protected. With the number of new risks and challenges involved, long-term security deployment strategies just don't fit into the DevOps realm. These days, security should be integrated into development and operations processes at the beginning and throughout the product life cycle. Implementing the AWS mentioned above DevOps security best practices is the best thing you can do to keep your DevOps environments agile and secure.
Published at DZone with permission of William Talluri. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments