PGP Encryption and Decryption With Apache Camel
Learn how to implement PGP security to encrypt and decrypt files with Apache Camel to protect sensitive files, emails, and other information.
Join the DZone community and get the full member experience.
Join For Free1.0 Overview
PGP (Pretty Good Privacy) encryption is used for encrypting, signing, and decrypting data like emails, text, files, directories, and whole disk partitions. It also increases the security of email communication and it can be used to authenticate digital certificates. Public and private keys play a vital role in PGP to encrypt and decrypt the data. Generally, a public key is used to encrypt the data and it is always shared with end users. The private key is used to decrypt the data and it is never shared with anyone.
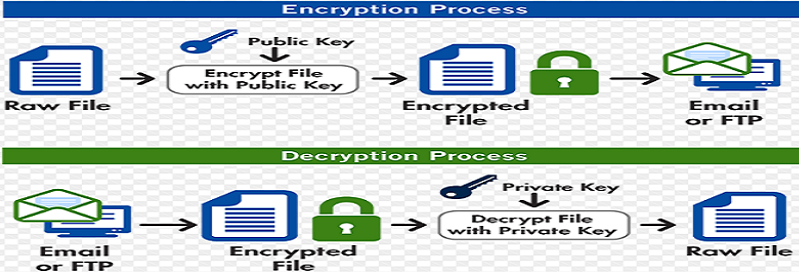
2.0 How Does PGP Work?
The process of converting plaintext into ciphertext is known as encryption, and converting ciphertext into plaintext is known as decryption. Ciphertext is nothing but unreadable gibberish.
Encrypting an entire message can be time-consuming. PGP uses a faster encryption algorithm to encrypt the messages and then uses the public key to encrypt the shorter key that was used to encrypt the entire message. Both the encrypted data and the short key are sent to the receiver, who first uses the receiver's private key to decrypt the short key and then uses that key to decrypt the message.
For example, Alice will use the public key to encrypt the data and send it to Bob. Now, Bob will decrypt the data using the private key.
3.0 Advantages of PGP Security
Sensitive information can be protected; others cannot view it and cannot be stolen over the internet.
Information can be shared securely within a group of users or company departments.
Files are compressed to a smaller size before being sent over the network.
There is no need to purchase private key or certificates.
Secure mail and text cannot be infiltrated by hackers or infected and misused through email attacks.
Future-proof technology and complete compatibility with other applications.
In-built key manager to securely manage yours and others' keys.
Provides absolute assurance that data receives or sent has not been modified in transit.
Provides protection against viruses and the newest blended email threat.
4.0 Generating Private and Public Keys
There are many tools available to generate PGP private and public keys. In this article, we will use Kleopatra to generate the private and public keys.
4.1 Generate the Private and Public Keys
Go to File > New Certificate > Create a personal OpenPGP key pair.
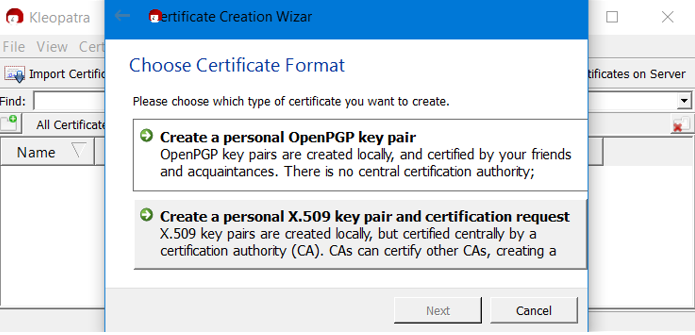
Provide Name and Email in the mandatory fields.
Click Next and Create Key. Provide a Passphrase and don’t forget the passphrase. Finally, click on Finish. It will generate a public key and private key.
4.2 Exporting the Public Key
Right click on the certificate and Export Certificates. Save the public key in .gpg format to some folder location on your disk.
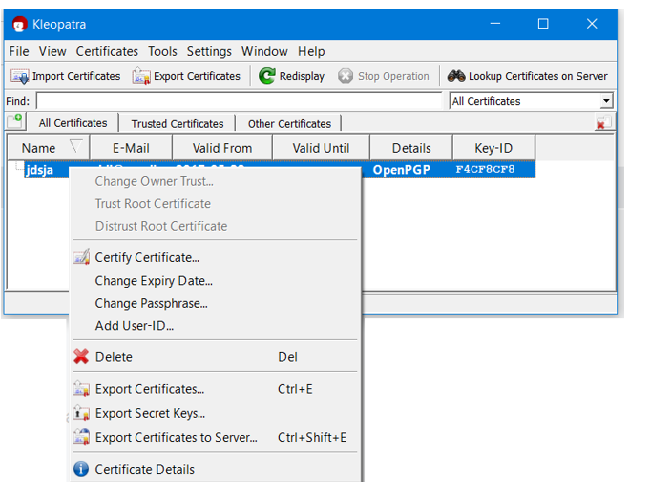
4.3 Exporting the Secret (Private) Key
Right click on the certificate and Export Secret Keys. Save the private or secret key in .gpg format to some folder location on your disk.
5.0 Implementing PGP Security With Apache Camel
The PGP Data Format integrates the Java Cryptographic Extension into Camel, allowing simple and flexible encryption and decryption of messages using Camel’s familiar marshall and unmarshal formatting mechanism. It assumes marshalling to mean encryption to ciphertext and unmarshalling to mean decryption back to the original plaintext. This data format implements only symmetric (shared-key) encryption and decryption.
| Name | Data Type | Description |
keyUserid |
String |
The userid of the key in the PGP keyring. |
password |
String |
Password used when opening the private key (not used for encryption). |
keyFileName |
String |
Filename of the keyring, must be accessible as classpathresource. |
armored |
boolean |
This option will cause pop to base64 encode the encrypted text, making it available for copy/paste, etc. |
integrity |
boolean |
add a integrity check/sign into the encryption file. |
5.1 PGP Encryption
Create empty java application and add class PGPEncrypter.java. Here we will use the public key to encrypt the message.
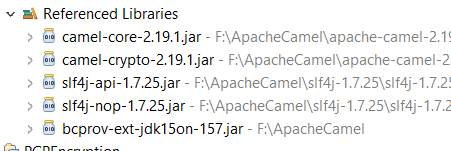
Download bcprov-ext-jdk15on-157.jar and bcg-jdk15on-157.jar from http://www.bouncycastle.org/latest_releases.html and add it to the build path of your application.
Add camel-core-x.xx.x.jar to build path of your application.
Below is the code for PGP encryption with Apache Camel.
package com.pgp.encrypt;
import org.apache.camel.CamelContext;
import org.apache.camel.builder.RouteBuilder;
import org.apache.camel.impl.DefaultCamelContext;
public class PGPEncrypter {
public static void main(String [] args) throws Exception
{
CamelContext camelContext=new DefaultCamelContext();
camelContext.addRoutes(new RouteBuilder(){
public void configure() throws Exception
{
final String publicKeyFileName="file:C:\\Users\\XYZ\\Desktop\\Camel_Certificate\\publickey.gpg";
final String keyUserid="jdsja <[email protected]>";
from("file:F:\\Apache_Camel_Test\\IN?noop=true;delete=true")
.marshal().pgp(publicKeyFileName, keyUserid)
.to("file:F:\\Apache_Camel_Test\\OUT");
}
});
camelContext.start();
Thread.sleep(5000);
camelContext.stop();
}
}
5.2 PGP Decryption
Create an empty Java application and add class PGPDecrypter.java. Here we will use the private or secret key to decrypt the message.
Download bcprov-ext-jdk15on-157.jar and bcg-jdk15on-157.jar from http://www.bouncycastle.org/latest_releases.html and add it to the build path of your application.
Add camel-core-x.xx.x.jar to the build path of your application.
Below is the code for PGP decryption with Apache Camel.
package com.pgp.encrypt;
import org.apache.camel.CamelContext;
import org.apache.camel.builder.RouteBuilder;
import org.apache.camel.impl.DefaultCamelContext;
public class PGPDecrypter {
public static void main(String [] args) throws Exception
{
CamelContext camelContext=new DefaultCamelContext();
camelContext.addRoutes(new RouteBuilder(){
public void configure() throws Exception
{
final String secretKeyFileName="file:C:\\Users\\XYZ\\Desktop\\Camel_Certificate\\secretkey.gpg";
final String keyUserid="jdsja <[email protected]>";
final String keyPassword="123456789";
from("file:F:\\Apache_Camel_Test\\IN?noop=true;delete=true")
.unmarshal().pgp(secretKeyFileName,keyUserid,keyPassword)
.to("file:F:\\Apache_Camel_Test\\OUT");
}
});
camelContext.start();
Thread.sleep(5000);
camelContext.stop();
}
}
6.0 Testing
To test the encryption, just drop the file to the input directory and run the PGPEncrypter program. It will encrypt the file and save to the output directory.
To test the decryption, just drop the file to the input directory and run the PGPDecrypter program. It will decrypt the file and save to the output directory.
7.0 Conclusion
PGP security is widely used for securing the sensitive data in emails, documents, and files; it secures the information from various cyber threats or hackers when sending data over the network. PGP doesn't just secure your data, it also compresses the data while sending it over the network. Apache Camel has provided simple steps to use PGP security in your applications.
Now you know how to implement PGP security with Apache Camel.
Opinions expressed by DZone contributors are their own.

Comments