How to Resolve an SSL Handshake Error With Mule
With these tips, you should be good sending requests to your Mule application again.
Join the DZone community and get the full member experience.
Join For FreeWhen you are running or deploying Mule 3.8 applications, you should note that TLSV1 is disabled by default, as it has security vulnerabilities. So, any application that you develop should be supporting only TLS1.1 and TLS1.2. If you have an HTTPS listener in your application and you want to send a request using the Fiddler, it may complain the following error:
org.mule.module.http.internal.listener.grizzly.MuleSslFilter: SSL handshake error: Client requested protocol TLSv1 not enabled or not supportedThe fix for the error is:
- Make sure that the Fiddler version is latest (>= .NET 4.0).
- By default, Fiddler supports only TLSV1, so we need to add TLS1.1 and TLS1.2 so that Fiddler sends the request using the server supported TLS version (in our case, it is our Mule runtime).
- Go to the Tools option in the menu item and click Fiddler Options.
- Select HTTPS folder.
- If the checkbox Decrypt HTTPS traffic is not checked, then check it.
- You should see Protocols with a hyperlink to click.
- Click on the link and add this text or append to the existing text: <client>;ssl3;tls1.0;tls1.1;tls1.2.
- Then close and reopen the Fiddler. You should be good sending requests to your Mule application now.
Here are the screenshots:
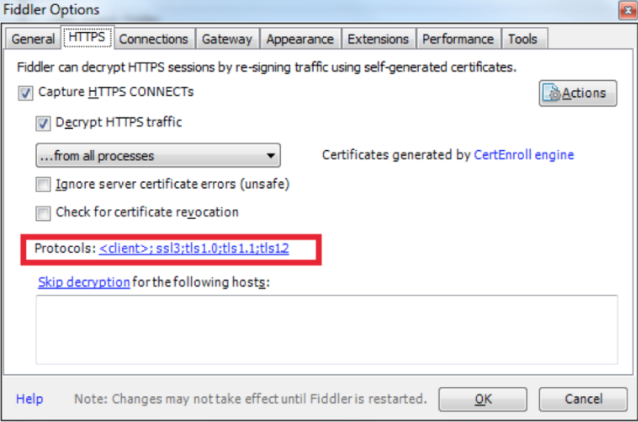
Figure 1

Figure 2
Hope this helps!
Published at DZone with permission of Akkiraju Ivaturi. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments