SAML Single Sign-On With JBoss Wildfly and PicketLink
To enable SAML Single Sign-On in Wildfly, you also need to enable SSL for the inbound connection / call back when the users browser sends their token supplied by the Identity Provider to avoid man in the middle attacks. Read on for more information.
Join the DZone community and get the full member experience.
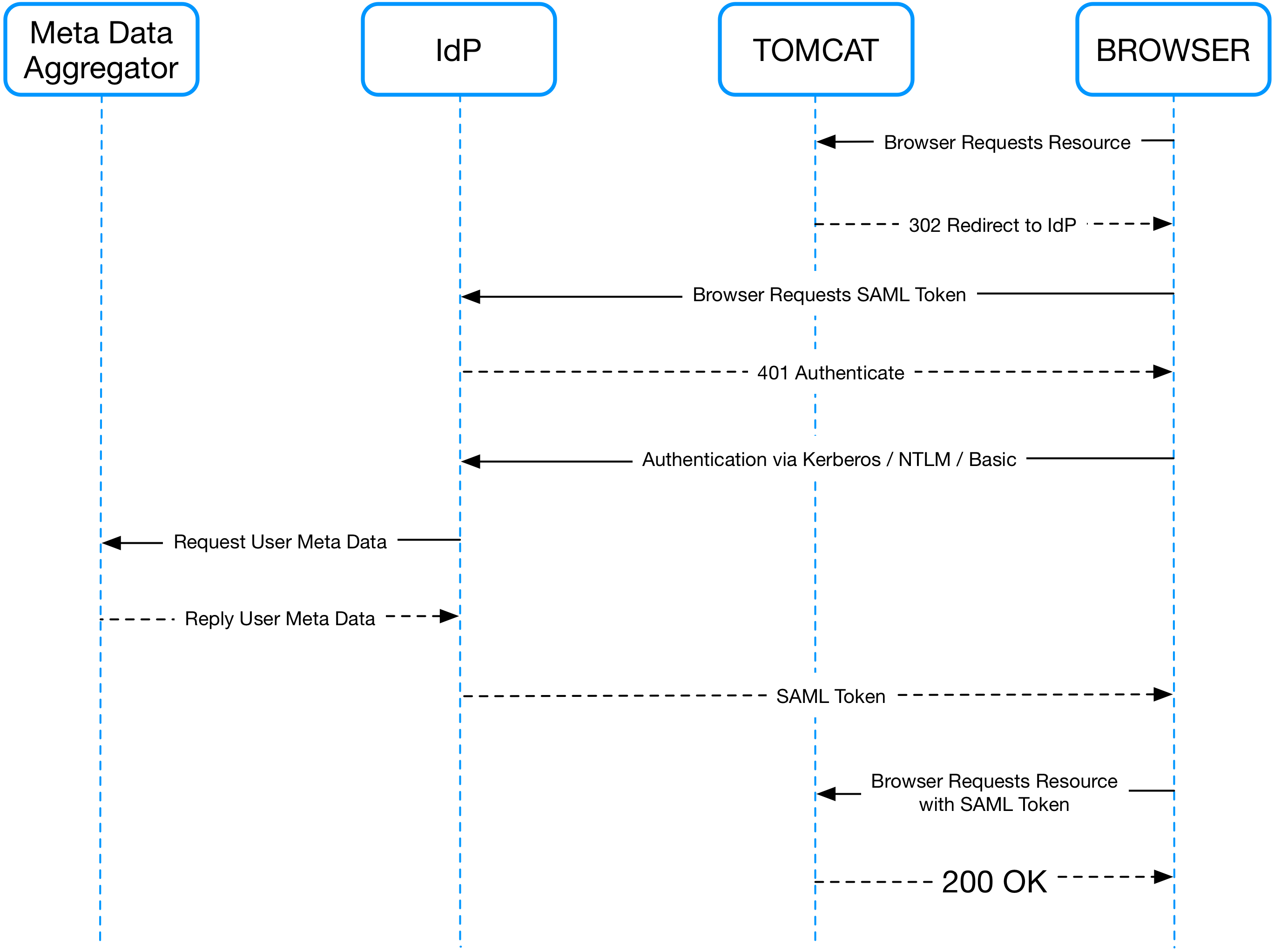
Join For FreeFor those of you who didn’t read my article about "Single Sign-On Made Easy: SAML With Tomcat and PicketLink" I will include the sequence diagram for SAML Single Sign-On here as well. For a detailed explanation of the diagram see my previous article.
To enable SAML Single Sign-On in Wildfly, you also need to enable SSL for the inbound connection / call back when the users browser sends their token supplied by the Identity Provider to avoid man in the middle attacks.
Commands for setting up SSL on JBoss (wildfly_ssl.cli)
create the script below and execute it with this command ”’ $JBOSS_HOME/bin/jboss-cli.sh –connect –file=wildfly_ssl.cli ”’
# Batch script to add and configure the quickstart-domain security domain in the JBoss server
# Start batching commands
batch
# Add and configure the security domain, then add the PicketLink SAML2LoginModule. Which wil be used to extract user's information from the SAML Assertion and authenticate the user.
/core-service=management/security-realm=SSLRealm:add()
/core-service=management/security-realm=SSLRealm/server-identity=ssl:add(keystore-path=ssl-keystore.jks, keystore-relative-to=jboss.server.config.dir,keystore-password=changeit, alias=myhostname.local, key-password=changeit)
/subsystem=security/security-domain=sp:add(cache-type=default)
/subsystem=security/security-domain=sp/authentication=classic:add
/subsystem=security/security-domain=sp/authentication=classic/login-module=org.picketlink.identity.federation.bindings.wildfly.SAML2LoginModule:add(code=org.picketlink.identity.federation.bindings.wildfly.SAML2LoginModule,flag=required)
# Run the batch commands
run-batch
# Reload the server configuration
:reload
/subsystem=undertow/server=default-server/https-listener=https:add(socket-binding=https, security-realm=SSLRealm)
Libs
It isn’t necessary to install PicketLink libraries on JBOSS because they are preinstalled.
Custom handlers may need to be installed depending on the configuration of the identity provider.
For one identity provider, I had to implement a handler for splitting a list of roles because they were stored in a single assertion attribute. In another case it was necessary to retrieve the the username from an assertion attribute and then change the user principal to reflect this name.
Web Application / Web Archive Structure
Here, our web app config will end up with the following structure:
/myapp
index.jsp
/META-INF
jboss-deployment-structure.xml
/WEB-INF
/classes
/META-INF
/services
io.undertow.servlet.ServletExtension
jboss-web.xml
picketlink.xml
web.xml
Changes to the web.xml
You must define the role names used in LDAP within the web.xml like this:
<security-role>
<description>App Users</description>
<role-name>BasicUser</role-name>
</security-role>
These roles will then need to be specified within the SecurityConstraints within the web.xml as well, like this:
<security-constraint>
<web-resource-collection>
<web-resource-name>User Space</web-resource-name>
<url-pattern>/internal/*</url-pattern>
<http-method>GET</http-method>
<http-method>POST</http-method>
<http-method>PUT</http-method>
<http-method>HEAD</http-method>
<http-method>TRACE</http-method>
<http-method>DELETE</http-method>
<http-method>OPTIONS</http-method>
</web-resource-collection>
<auth-constraint>
<role-name>BasicUser</role-name>
</auth-constraint>
<user-data-constraint>
<transport-guarantee>NONE</transport-guarantee>
</user-data-constraint>
</security-constraint>
However, do not remove the login-config section because unlike in Tomcat here it is required even if never used.
<login-config>
<auth-method>FORM</auth-method>
<form-login-config>
<form-login-page>/login</form-login-page>
<form-error-page>/login?error=true</form-error-page>
</form-login-config>
</login-config>
Add picketlink.xml to the WEB-INF Folder
<?xml version="1.0" encoding="UTF-8"?>
<PicketLink xmlns="urn:picketlink:identity-federation:config:2.1">
<PicketLinkSP xmlns="urn:picketlink:identity-federation:config:2.1" BindingType="POST">
<IdentityURL>${idp.url::https://dc.mydomain.com/adfs/ls/}</IdentityURL>
<ServiceURL>${myapp.url::https://jboss.mydomain.com:8443/myapp/internal/}</ServiceURL>
<Trust>
<Domains>localhost,mydomain.com</Domains>
</Trust>
</PicketLinkSP>
<Handlers xmlns="urn:picketlink:identity-federation:handler:config:2.1">
<Handler class="org.picketlink.identity.federation.web.handlers.saml2.SAML2IssuerTrustHandler" />
<Handler class="org.picketlink.identity.federation.web.handlers.saml2.SAML2LogOutHandler" />
<Handler class="org.picketlink.identity.federation.web.handlers.saml2.SAML2AuthenticationHandler">
<Option Key="ROLE_KEY" Value="http://schemas.microsoft.com/ws/2008/06/identity/claims/role"/>
</Handler>
<Handler class="org.picketlink.identity.federation.web.handlers.saml2.RolesGenerationHandler" />
</Handlers>
</PicketLink>
Valves and Realms
Unlike Tomcat, here a valve is not required and, apart from the SSLRealm we configured earlier, there isn’t any need for a specific realm for SAML
JBoss Does Require a jboss-web.xml in the WEB-INF Folder
In this file is specified the Security Domain for the web app, the one configured previously in the cli file. We also define the context root of the web app which should match the prefix in the picketlink file when referring to the ServiceURL e.g. if the context is myapp the service URL is prefixed with “${myapp.url::”
<jboss-web>
<security-domain>sp</security-domain>
<context-root>myapp</context-root>
</jboss-web>
jboss-deployment-structure.xml
In the META-INF folder add a file called jboss-deployment-structure.xml. This file should contain the module dependencies of the web app. In this case, we have added org.picketlink as a dependency.
<?xml version="1.0" encoding="UTF-8"?>
<jboss-deployment-structure>
<deployment>
<dependencies>
<module name="org.picketlink"/>
</dependencies>
</deployment>
</jboss-deployment-structure>
SPServletExtension
Now we should add a service definition to the war, telling it to use the SPServletExtension. You do this by creating a file called io.undertow.servlet.ServletExtension in the folder WEB-INF/classes/META-INF/services/
The file should contain the following class name:
org.picketlink.identity.federation.bindings.wildfly.sp.SPServletExtensionTroubleshooting
Useful command for checking out the log files which you use from the JBoss command line interface $JBOSS_HOME/bin/jboss-cli.sh –connect:
/subsystem=logging:read-log-file(name=server.log,lines=200)Opinions expressed by DZone contributors are their own.

Comments