Spring Boot 2 Applications and OAuth 2 - Legacy Approach
In today's post, we explore a legacy Spring Boot 2/Spring Security 5 approach to enabling an OAuth2-based authentication mechanism for an application.
Join the DZone community and get the full member experience.
Join For FreeThis post is the second part of a 3 post series exploring ways to enable SSO with an OAuth2 provider for Spring Boot 2 based applications. The 3 posts are:
- Ways to bootstrap an OpenID Connect compliant OAuth2 Authorization Server/OpenID Provider
- Legacy Spring Boot/Spring 5 approach to integrating with an OAuth2 Authorization Server/OpenID Provider - this post
- Newer Spring Boot 2/Spring 5 approach to integrating with an OAuth2 Authorization Server/OpenID Connect Provider - coming soon
This post will explore a legacy Spring Boot 2/Spring Security 5 approach to enabling an OAuth2-based authentication mechanism for an application. This post assumes that all the steps in the previous blog post have been followed and UAA is up and running.
A question that probably comes to mind is why am I talking about legacy in the context of Spring Boot 2/Spring Security 5 when this should have been the new way of doing SSO? The reason is, as developers, we have been using an approach with Spring Boot 1.5.x that is now considered deprecated. There are features in it, however, that have not been completely ported over to the new approach (the ability to spin up an OAuth2 authorization server and the ability to create an OAuth2 resource server, are examples). In the interim, Spring Security developers (thanks, Rob Winch and Joe Grandja) provided a bridge to the legacy approach in the form of a spring-security-oauth2-boot project.
Approach
So what does the legacy approach look like? I have detailed it once before here, but, to recap, it works on the basis of an annotation called @EnableOAuth2SSO and a set of properties supporting this annotation. A sample security configuration looks like this:
import org.springframework.boot.autoconfigure.security.oauth2.client.EnableOAuth2Sso;
import org.springframework.context.annotation.Configuration;
import org.springframework.security.config.annotation.web.builders.HttpSecurity;
import org.springframework.security.config.annotation.web.builders.WebSecurity;
import org.springframework.security.config.annotation.web.configuration.WebSecurityConfigurerAdapter;
@EnableOAuth2Sso
@Configuration
public class OAuth2SecurityConfig extends WebSecurityConfigurerAdapter {
@Override
public void configure(WebSecurity web) throws Exception {
super.configure(web);
web.ignoring()
.mvcMatchers("/favicon.ico", "/webjars/**", "/css/**");
}
@Override
protected void configure(HttpSecurity http) throws Exception {
http.csrf().disable();
http.authorizeRequests()
.antMatchers("/secured/**")
.authenticated()
.antMatchers("/")
.permitAll()
.anyRequest()
.authenticated();
}
}And the set of supporting properties to point to the UAA is the following:
ssoServiceUrl: http://localhost:8080/uaa
security:
oauth2:
client:
client-id: client1
client-secret: client1
access-token-uri: ${ssoServiceUrl}/oauth/token
user-authorization-uri: ${ssoServiceUrl}/oauth/authorize
resource:
jwt:
key-uri: ${ssoServiceUrl}/token_key
user-info-uri: ${ssoServiceUrl}/userinfoWith the spring-security-oauth2-boot project pulled in as a dependency:
compile 'org.springframework.cloud:spring-cloud-starter-oauth2'
compile("org.springframework.security.oauth.boot:spring-security-oauth2-autoconfigure:2.0.0.BUILD-SNAPSHOT")These annotations only work for a Spring Boot 2 application. Note, however, that Spring Boot 2 supports two distinct Web Frameworks - Spring Web and Spring Webflux, and this approach pulls in Spring Web transitively which forces Spring Web to act as the default framework.
The sample in its entirety, with ways to start it up, is available on my GitHub repo here.
Testing
Any URI starting with "/secured/**" is SSO enabled. If the index page is accessed it is displayed without the need to provide any authentication:

Now, clicking through to a URI starting with "/secured/**" should trigger an OAuth2 Authorization Code flow:

The user should be presented with a login screen via UAA:

Logging in with the credentials that were created before - user1/user1 should redirect the user back to the Spring Boot 2 legacy version of the app and should display the secured page:
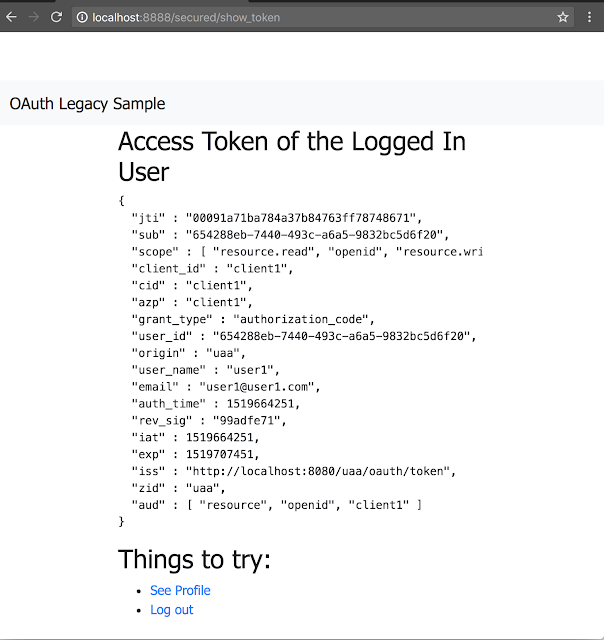
This completes the legacy approach to SSO with Spring Boot 2. Note that this is just pseudo-authentication, OAuth2 is meant more for authorization to access a user's resource than authentication the way it is used here. An article which clarifies this is available here. The next post with native Spring Security 5/Spring Boot2 will provide a cleaner authentication mechanism using OpenID Connect.
Published at DZone with permission of Biju Kunjummen. See the original article here.
Opinions expressed by DZone contributors are their own.

Comments