Vulnerability Management in DevOps Environments
Vulnerability management in DevOps integrates security into the development workflow to identify and fix vulnerabilities throughout the software lifecycle.
Join the DZone community and get the full member experience.
Join For FreeDevOps has become the groundwork for delivering top-notch applications quickly and efficiently in today’s agile development. Its efficiency and speed can also cause notable security threats if vulnerabilities are not managed properly.
Sixty percent of data breaches succeed because organizations fail to apply known, available patches before the weaknesses are exploited.
This piece explores the key importance vulnerability management plays in DevOps infrastructure, spotlighting methods to incorporate resilient defenses while retaining the swiftness and creativity provided by DevOps.
The Essentials of Vulnerability Management
Vulnerability management is an indispensable part of the security measures of an organization. It is a preventive method that spots, examines, handles, and reviews the security weaknesses in systems and software.
Unpatched vulnerabilities played a role in 60% of data breaches. vulnerability management aims to alleviate the chances threat actors may have for exploitation. It consists of key components which include:
- Identification: This involves scanning software and systems to find weaknesses.
- Evaluation: This has to do with reviewing the strengths and expected outcomes of the weaknesses found.
- Treatment: Taking steps to amend vulnerabilities
- Reporting: Noting and communicating the position and advancement of security enhancement efforts
Common Types of Vulnerabilities in Software and Infrastructure
Weaknesses within infrastructure and software can prevail in numerous forms, common types include:
- Code flaws: Problems in software code can be taken advantage of.
- Configuration issues: Errors in applications or security can make security vulnerable.
- Outdated software: Operating outmoded editions with confirmed flaws
- Weak authentication: Inadequate security measures that can be evaded very easily
- Third-party components: Weaknesses in external dependencies incorporated in the software.
The Impact of Unmanaged Vulnerabilities on DevOps Workflows
Unmanaged weaknesses can have a significant influence on DevOps workflow. This can lead to critical repercussions, including leveraging weaknesses to breach systems causing severe financial and reputational damage.
Operational disruption is also an impact of unmanaged vulnerabilities. When an attack targets a weak spot it can disrupt services and lead to a system downtime which will affect the continuity of business.
Incapacity to handle vulnerabilities can result in non-compliance with the regulatory framework, attracting legal consequences. Lastly, the market position and reliability of an organization are also at stake here, unwavering security problems can deplete customers’ and stakeholders’ trust.
Integration of Vulnerability Management in DevOps
DevSecOps involves adding security measures to every software development phase. This method includes cooperation between operation, development, and security teams, making security a collective obligation.
Focusing on security from the start enables identifying and resolving issues early to prevent them from becoming hurdles at a later time. This strategy helps reduce the risk associated with security issues later on when the software is completed.
CI/CD pipelines are pivotal, they automate integration and deliver code changes. Including security scans in these pipelines can allow for consistent weakness tests, making sure that upon modification it is put to test for security issues. Running these automated tests alongside normal tests gives quick responses to developers to resolve issues that can become a roadblock to the development process.
Automated Tools
To manage security vulnerabilities, it is important to use automated tools. Different types of tools apply to different phases.
- Static Application security testing (SAST): These tools check the code for weaknesses before it is deployed.
- Dynamic Application Security Testing (DAST): Dast tools find vulnerabilities in an application or system that is already executed.
- Software Composition Analysis (SCA): Software composition analysis tools observe external dependencies used in the project for identified security problems.
In addition, GitLab CI, Jenkins, and CircleCI are tools that can easily combine security checks into the creation process. It allows for constant observation and quick patches to any security risks.
Comprehensive Vulnerability Management Strategy
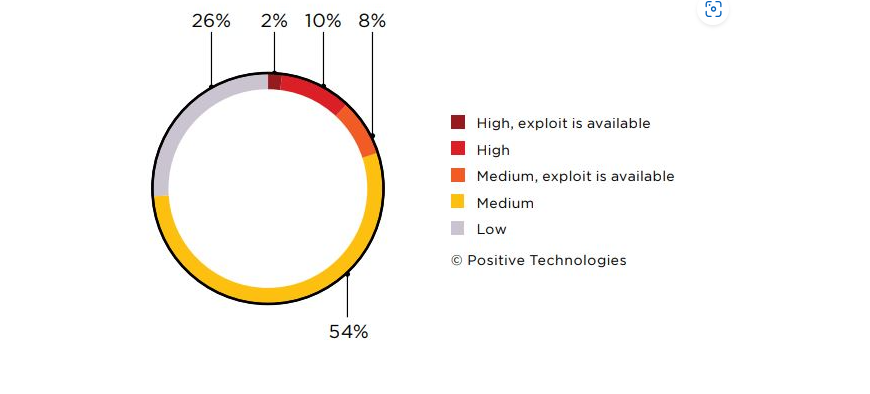
According to research by Positive Technologies, 84 percent of companies have high-risk vulnerabilities on their external networks. The research also hinted that more than half of these weaknesses can be erased simply by installing updates.
The first step in comprehensive vulnerability management is carrying out rigorous tests that involve discovering susceptibilities that exist within software and systems. Once these weaknesses have been identified, rank them in order of priority; that is, focus on the most critical exposure first, as high-risk vulnerabilities can cause greater damage. Lower risks should be resolved later.
Setting up well-defined vulnerability management rules is indispensable. This guideline should draft how weaknesses will be identified, reported, and reviewed. The obligation of team members should also be clarified to make sure everyone knows the role they play in security upkeep.
A sophisticated framework includes:
- Patch management
- Regular vulnerability scan
- Incident response plan to manage any data breach that could happen regardless of safety measures
The value of an enlightened team cannot be overstated. To keep your DevOps team updated on new security risks and their model procedures, regular training and awareness programs are needed.
These programs should address how to discover susceptibilities in code and software, how security tools can be used efficiently, and the benefits of compliance with vulnerability management policy. When your team is enhanced with the right skills and knowledge, vulnerabilities will be preemptively identified and alleviated before they are capitalized on.
Security is a continuous operation, not a task to be performed once. To adjust to new risks and weaknesses, security baselines should be regularly updated and maintained. This involves:
- Monitoring systems and software regularly
- Applying updates and patches instantly
- Revising security policies as necessary
- Conducting audits and assessments to ensure compliance with security standards and discover the areas that need improvement
Embracing a Proactive Security Culture in DevOps
To maintain the integrity and security of cutting-edge programming, effective vulnerability management in a DevOps environment is crucial. Integrating security practices into every phase of DevOps development can help organizations preemptively uncover and mitigate weaknesses ensuring a robust and resilient infrastructure.
DevOps continues to evolve and so do cyber threats. To maintain reliability and be safe from unfolding risks in the virtual terrain prioritize security, and embrace a culture of continuous progress.
Opinions expressed by DZone contributors are their own.

Comments