XData and SambaCry Add to the Whopping Number of Data Breaches This Year
While the repercussions of WannaCry have finally been dealt with, a whole new batch of ransomware and malware is lurking right around the corner.
Join the DZone community and get the full member experience.
Join For Free
Weeks after WannaCry appeared center stage, networks around the world are still being bombarded with clusters of cyber threats including Adlykuzz and EternalRocks. But is that all? Nope. Two more threats, XData and SamabaCry, are already doubling the number of existing threats. Since WannaCry, almost half of all data breaches have affected the business sector, causing headaches for enterprises.
XData, which was first discovered by malware security researcher S!Ri, is eerily similar to WannaCry; XData even targets EternalBlue, the same exploit that WannaCry used. Like typical ransomware, XData encrypts the victim's files and then asks for a ransom to decrypt them. After encrypting the files, XData appends those files' names with the suffix XData (e.g.,"demo.jpg-xdata-"). It also creates a new file in each folder called "How_can_I_decrypt_my_files.txt," which is the XData ransom note shown below.
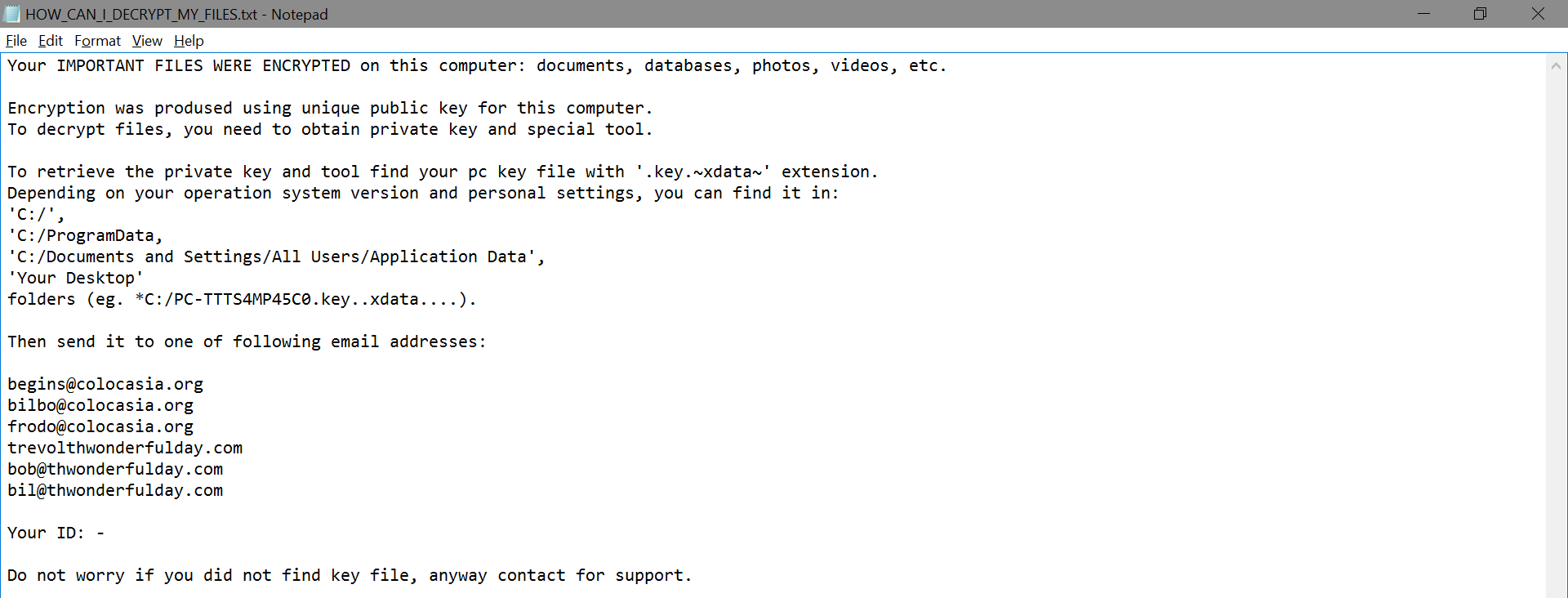
XData employs asymmetric cryptography, requiring both public and private keys to decrypt the files. Victims have to pay a ransom, usually between $500 and $1,000 to receive this private key from the XData developers. In most cases, however, paying the ransom hasn't gotten victims their files back. Cybersecurity researchers have stated that 90 percent of attacks related to XData have targeted individuals in Ukraine, but that doesn't mean individuals in other countries are safe. XData also has a lot of other ransomware variants like Stampado, ONYONLOCK, Cryptoviki, and Spora.
Even though these ransomware attacks have primarily targeted Windows users, Linux users are no longer an exclusion. Many Linux users rely on Samba, an open-source software suite, to seamlessly transfer files and print services to SMB/CIFS clients. Similar to how WannaCry exploited the SMB vulnerability in Windows, this new malware (nicknamed SambaCry) exploits a seven-year-old vulnerability in Samba. This vulnerability—indexed as CVE-2017-7494—affects how Unix machines communicate with Microsoft systems.
SambaCry uses three loopholes to exploit Linux systems:
- smbd running on TCP port 443.
- "nt pipe support" setting enabled in smb.conf.
- A writeable share is accessible by an attacker.
To initiate an attack, the hacker uploads a shared object to the writeable share and executes a small command to make the smbd execute that shared object. This allows the hacker to attain root privileges, granting them access to the entire system. In a strategic move, hackers released SambaCry during a major U.S. holiday, making the attack more difficult to resolve. Samba has already issued a patch to resolve the issue. Apart from this, users can avoid SambaCry by disabling the "nt pipe support" setting or by blocking their TCP port 445 from untrusted sources.
SambaCry is just the beginning for Linux users. Now, Linux users face another malware threat: LuaBot. This multicomponent trojan is said to detect honeypots, which makes it smarter than previous threats. LuaBot is an interconnected trojan that uses a pool of IP addresses to launch a brute force attack, targeting Telnet and SSH protocols. A detailed technical analysis explaining how this attack works is available from Dr.Web.
Patching is often the first line of defense against cyber threats, but when system administrators are firefighting on a daily basis, they don't have time to bolster their defenses. Some enterprises even temporarily shut off their network due to the amount of issues that can pile up. So, if you've got a moment to catch your breath between fires, ensure that all your linux patches are up to date. Complete tranquility cannot be realistically expected in the cybersecurity sector, but if we work together, we can stamp out threats before they spread like wildfire.
Opinions expressed by DZone contributors are their own.

Comments