Authentication and Authorization: Mastering Security
Your one-stop-shop for all things authentication and authorization.
Join the DZone community and get the full member experience.
Join For Free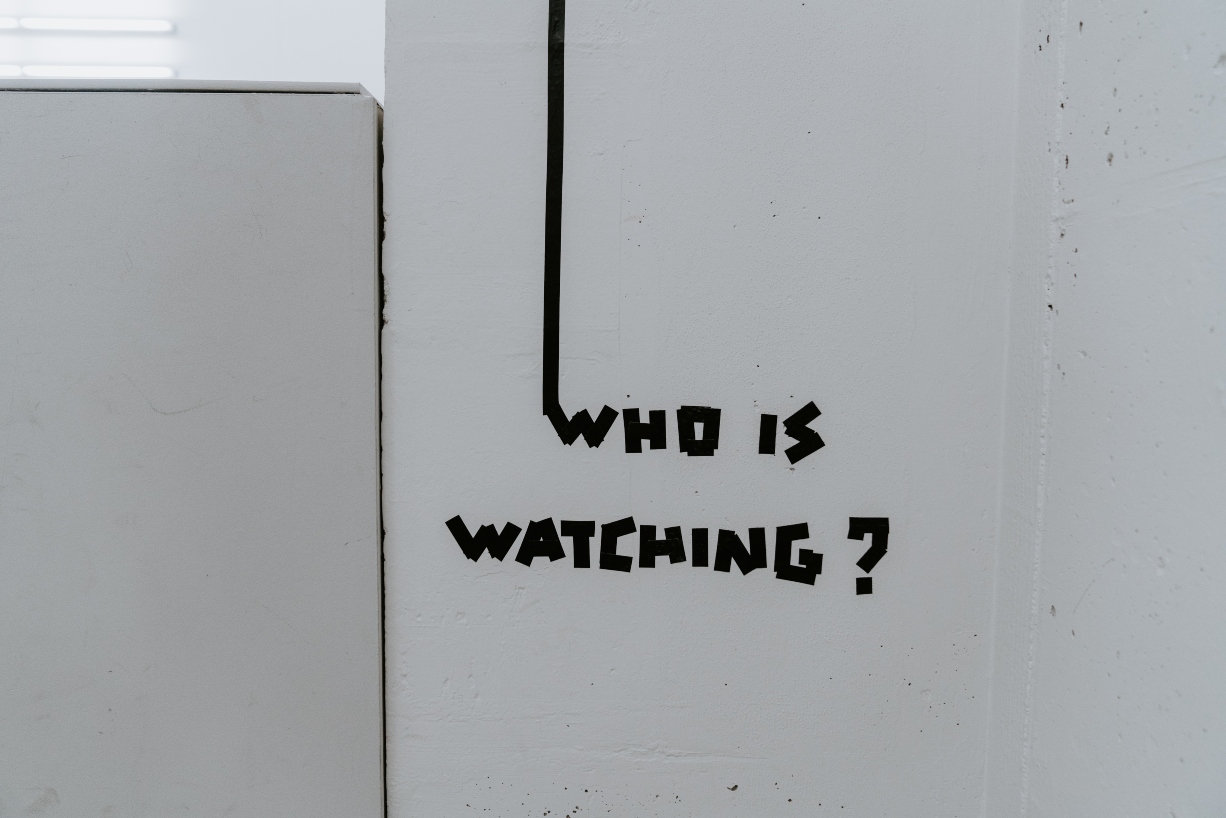
In this edition of "Best of DZone," we dive into a topic that's forgotten all too often during software development: security. So, strap in, close the blinds, and, as our CTO likes to say, "Put on your tin foil hats," as we dive into all things authentication and authorization.
Whether it be auth basics, adding auth to your web apps, microservices, or APIs, or getting started with JSON Web Tokens (JWTs), we (meaning our amazing community of contributors) have your back to make sure your next project is completely secure, no matter the situation.
Let's get started!
Cyber Security Basics
In Modern Authentication and Authorization: A Brief Introduction, developer Christopher Lamb gives readers a brief overview of key security concepts and tools, such as SAML, OAuth, OpenID, and CAS. Additionally, he describes some common issues that developers run into when first implementing authentication and authorization.
Introduction to SAML for Managers by Brett Crawley walks readers through the functionality and core concepts in SAML for those looking to get started managing their application's security.
Then, for getting started with the XML-based framework, see How SAML Authentication Works by Prosper Otemuyiwa for more information on how the protocol works, requests are generated and read, and what tools can you keep projects secure.
In OAuth 2.0 Beginner's Guide by Suraj Kumar, get a step-by-step overview of getting started with the security framework.
In this final part of this four-part series by Vladimir Pecanac, check out an in-depth look at HTTP authentication and how you can use it in your next application.

Authentication Basics
In How Authentication Works in Encryption, developer Anastasios Arampatzis discusses major factors involved with authentication (knowledge, possession, inherence) and describes the role digital certificates and signatures play in authentication.
In this article by Bozhidar Bozhanov, take a look at how to enable two-factor authentication for your next web application with Google Authenticator, which uses TOTP for generating verification codes.
Getting Started With OAuth
Dive further into OAuth with Spring Boot and Spring Security with author, Andrew Hughes, as he describes how to build an OAuth authorization server in a Java application.
In this OAuth tutorial, see how to secure a Spring REST API using OAuth2 and a PostgreSQL database by configuring an authorization and resource server.
Role-Based Access Control
In this two-part series, developer, Matthew Groves, walks readers through how to add Role-Based Access Control with Couchbase Server in order to better manage user authorization in your web application.
A Spring Security Tutorial for Everyone
Follow along with MVB, Duncan Brown, as he shows readers how to integrate authentication into a Spring MVC with the many different Authentication Manager classes that Spring provides.
Get the low-down on all things Okta in this tutorial, as Lindsay Brunner provides a tutorial on how to use Okta's authentication API with Java servlets in order to better secure your Java application.
Learn how to determine if a user logs in from a new device or location with Spring Security in Chirag Thumar's article, Device Authentication: Notify User of Login From New Device or Location.
Follow along with Rida Shaikh in this tutorial, as she presents readers with a "Hello, World" tutorial with Spring Boot Security and JWTs.
If you're in a pinch and need to add a login page to your Spring application, then this tutorial is perfect for you. Andrews Hughes has you covered with this tutorial that covers various ways that you can add a login feature for SSO with Spring.
Nadyen Gochev offers readers the opportunity to learn all about how to use Spring's RestTemplate to add client certificate authentication to your Spring application.
Still looking for more on Spring security? Check out these Refcardz by Willie Wheeler (Expression-Based Authorization With Spring Security) and Arjan Tijms and Masoud Kalali (Java EE Security Essentials) for in-depth looks into securing your Java applications.

ASP.NET Security
In Facebook Authentication and Authorization in Server-Side Blazor Application by Ankit Sharma, learn how to use Facebook to implement authentication and authorization in your ASP.NET application.
Secure authentication is only half the battle. In this post by Lee Brandt, readers will learn how to implement authorization in an ASP.NET Core MVC application with Okta. Then, see how to add user authorization with OIDC and OAuth with another tutorial by Lee Brandt, Build Secure User Authentication in ASP.NET Core With OIDC and OAuth.
API Security
The world of APIs is growing very fast. You use many of them and (probably) you provide some of them.
Need to add authentication to your REST APIs? Check out Steps to Build Authentication and Authorization for RESTful APIs by Derric Gilling, in which he shows readers the necessary steps to add token-based authentication to RESTful APIs.
In Ensure the Security of APIs, Vivek Yadav discusses different types of APIs, clients, and techniques for protecting API data.
Microservices Authentication and Authorization
Looking for more well-defined patterns for adding authentication and authorization to microservices? Look no further than this article by Sibanjan Das, as he describes the basics of securing microservices with authentication and authorization protocols and how security fits into this architecture.
Following along with Oren Eini in Authentication and Authorization in Microservice Architecture, as he describes how to manage the pitfalls associated with adding authentication and authorization in Microservices to allow for better UI.
Take a look at this step-by-step tutorial by Juan Ignacio to see how EKS interacts with Kubernetes to secure your containers.

JWT Authentication
Still not quite sure you have all the basics behind JWTs down? Check out What Is a JWT Token by Prathap Givantha Kalansuriya to get started adding JWTs to your security protocol.
Start building your own JWTs with Lindsay Brunner's article, Create Your JWTs From Scratch. (If you're looking for a Spring Boot-specific tutorial, check out Bruno Krebs' article, Implementing JWT Authentication on Spring Boot APIs.)
If you're looking to go even deeper with JWTs, look no further than Yos Riady's article, Stateless Authentication With JSON Web Tokens.
Misceallaneous
See how blockchain can make yet another impact on the security industry with Jakub Ner's article, Introduction to Overhide-Ledger and Ledger-Based Authentication.
Having trouble finding a resource on adding authentication and authorization to Amazon Cognito? (The author of this article did too.)
Opinions expressed by DZone contributors are their own.

Comments