Beyond IAM: Implementing a Zero-Trust Data Plane With Service Account Identity Federation in GCP
Eliminate the number one cause of GCP breaches — stolen Service Account keys — by enforcing the Secure Token Service (STS) for all data-plane authentication
Join the DZone community and get the full member experience.
Join For FreeWhy IAM Alone Is No Longer Sufficient for Cloud Security
Organizations now process and move data differently because of modern, cloud-native platforms. Workloads such as Spark jobs, Kafka streams, Snowflake queries, and ML pipelines run continuously in short-lived environments. IAM systems are still important, but they were primarily built to secure the control plane and determine who can log in, manage resources, and set policies. IAM was not designed to control what running workloads can do.
Security models have shifted from perimeter-based defenses to zero trust. Relying on network location or long-lived credentials is now seen as risky. Today, the data plane, where jobs interact with data, is the primary target of attacks. Data-plane identities often use static service account keys, OAuth tokens, or shared secrets. These are usually long-lasting, have too many permissions, are hard to rotate, and are reused in many places, which increases risk if they are stolen.
Google Cloud was quick to recognize this shift and adopted the BeyondCorp zero-trust model, which assumes no implicit trust and enforces identity at every access point to resources. GCP, on this basis, provides native workload identity federation, enabling workloads to authenticate using short-lived, verifiable identities instead of static secrets.
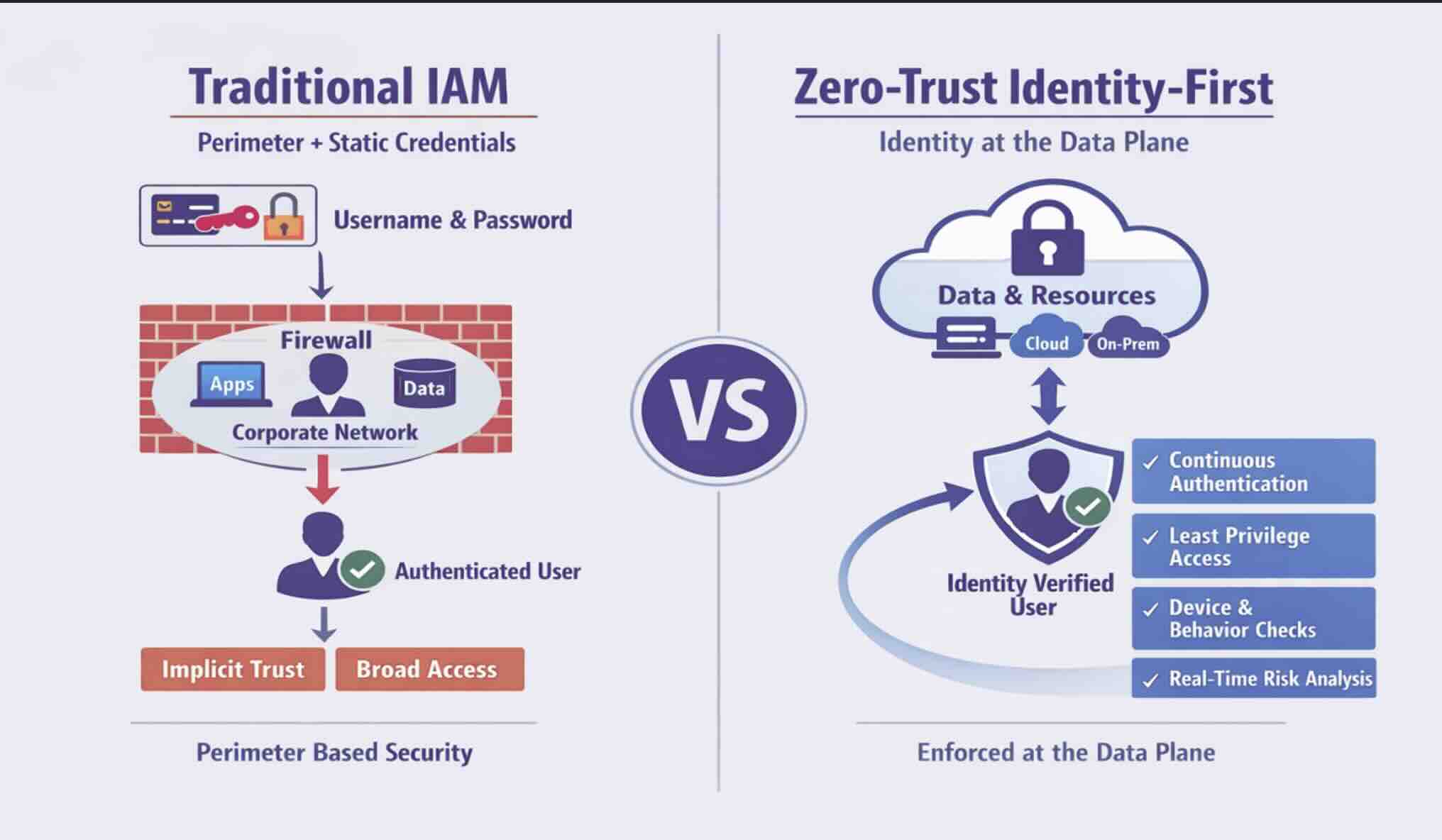
Zero-Trust Principles Applied to the Cloud Data Plane
Zero-trust security (ZTS) is the model that does not initially trust anything. It embodies a model that necessitates every request, every identity, and all workloads to continuously undergo verification. The most important points are: distrust always, verify always; concentrate on identity, not the network location; apply ongoing authentication; access only has to be given just in time and with the least privileges needed. Though these ideas are mostly associated with the control plane, implementing them in the data plane carries new challenges.
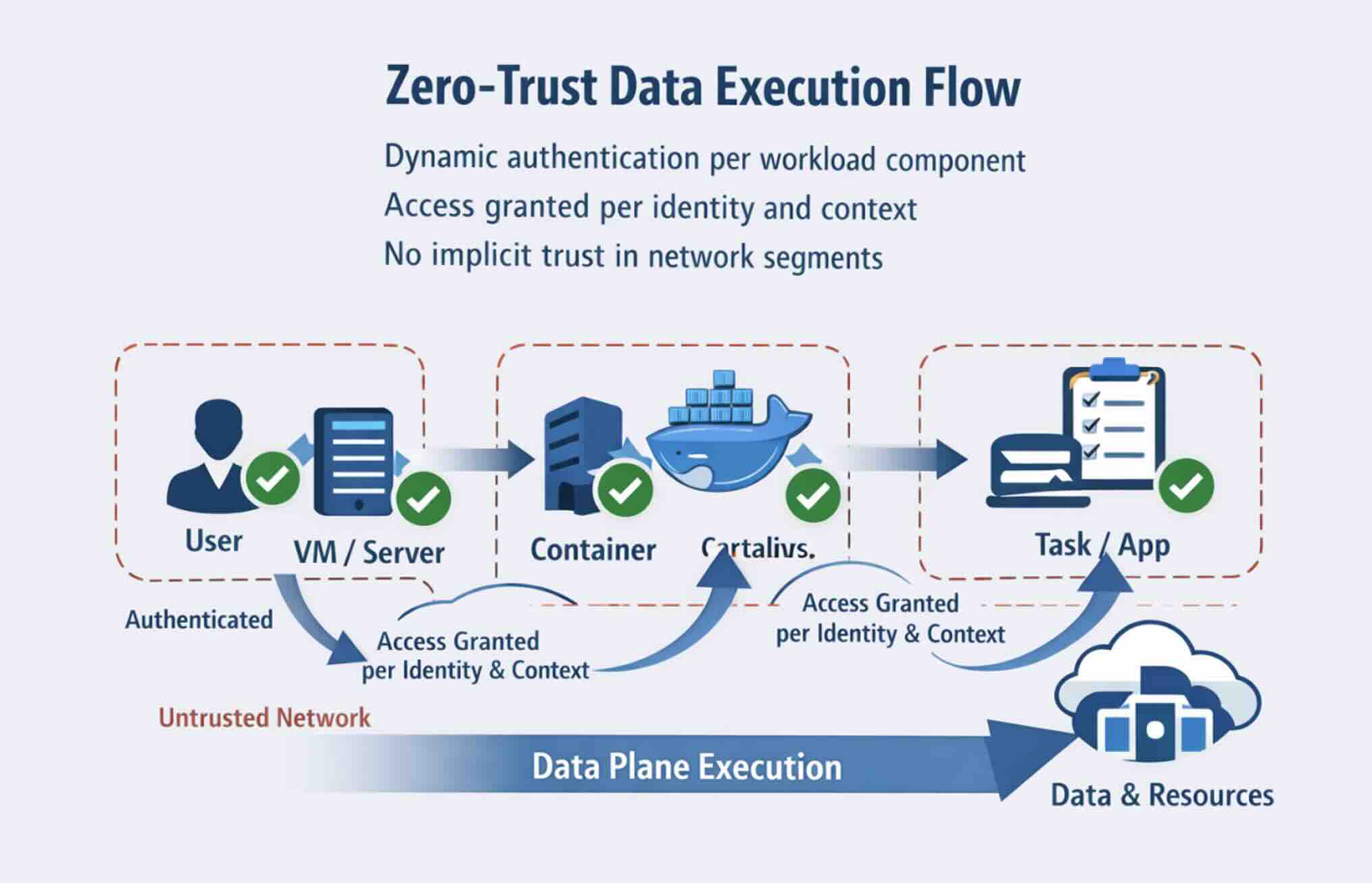
The data plane workloads are temporary in nature, which makes them hard to manage, being distributed in clusters and clouds and communicating with on-premises and Software as a Service (SaaS) systems. Most of the data-plane identities are machine accounts that are typically assigned to applications or services. In particular, in the scenarios of machine identities, they frequently possess a long life, too many permissions, and the rotation process is complicated, which consequently makes them appealing to attackers.
To impose zero trust for data workloads, give every workload the vision of a separate entity that can be identified. Spark executors, Kafka consumers, and Snowflake queries must use identity-based credentials that are transient. The rights should be assigned based on the current context of the workload rather than being either fixed or preset.
Google Cloud provides a practical approach to this through its BeyondCorp. ZT-seeding is highly pragmatic. It maintains an identity-aware access system without relying on network trust. Additionally, the combination of workload identity federation and short-lived tokens used by GCP not only secures distributed data pipelines but also reduces the chance of credentials being stolen.
What Is Service Account Identity Federation?
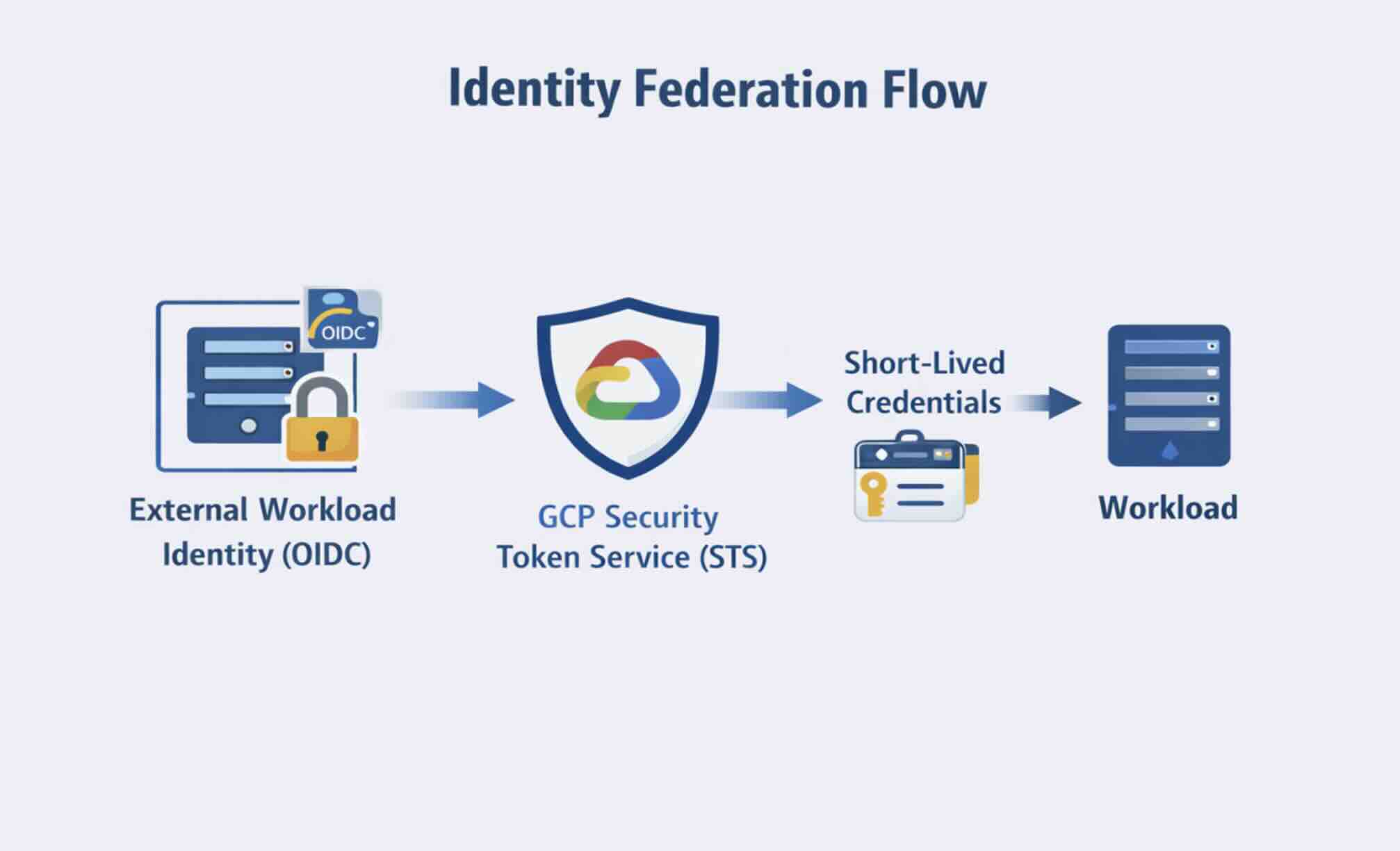
Service Account Identity Federation is a paradigm shift in security with the use of containerization and Deployment on External Workloads without service account keys, which are hard to change and long-automated. This is possible through the use of a valid external identity that is exchanged for a relative credential, not secret ones kept in the code, configuration files, or cloud pipelines. Therefore, the actual exposure of the code with keys stored in it, key theft, or mismanagement is significantly reduced due to the smaller attack surface.
How It Works (High Level)
- Workload presents an identity token, which is legible by the cloud, usually these tokens are supplied by an external identity provider like OIDC, AWS IAM, or Azure AD.
- The Cloud IAM verifies the trust relationship between the external identity provider and it, and confirms the request is from an authorized source.
- After the request is valid, the cloud gives the user short-lived credentials for the specific permission.
- The credentials automatically bloom; there is no risk for hard, long-living secrets to be harvested by the time they age.
Google Cloud Deep Dive
Google Cloud's workload identity federation (WIF) is the happiest and most efficient system that serves this purpose with no problems. WIF has the following applications:
- That no service account keys are ever kept or sent by any means.
- External workloads in environments, clouds, or CI/CD pipelines can get Google Cloud credentials in a secure manner.
- You can rely on OIDC providers, AWS IAM roles, or Azure AD for the establishment of trust; it is cloud-agnostic.
Contrast
- Federation vs. static service account keys: Federation is the elimination of the tedious paperwork of dealing with long-term key management, such as manual rotation and securing treasured keys.
- Federation vs. personal access tokens (PATs): Federated credentials are opposed to PATs because they are short-lived, scoped, and auditable; therefore, they counteract misuse and lateral movement systematically.
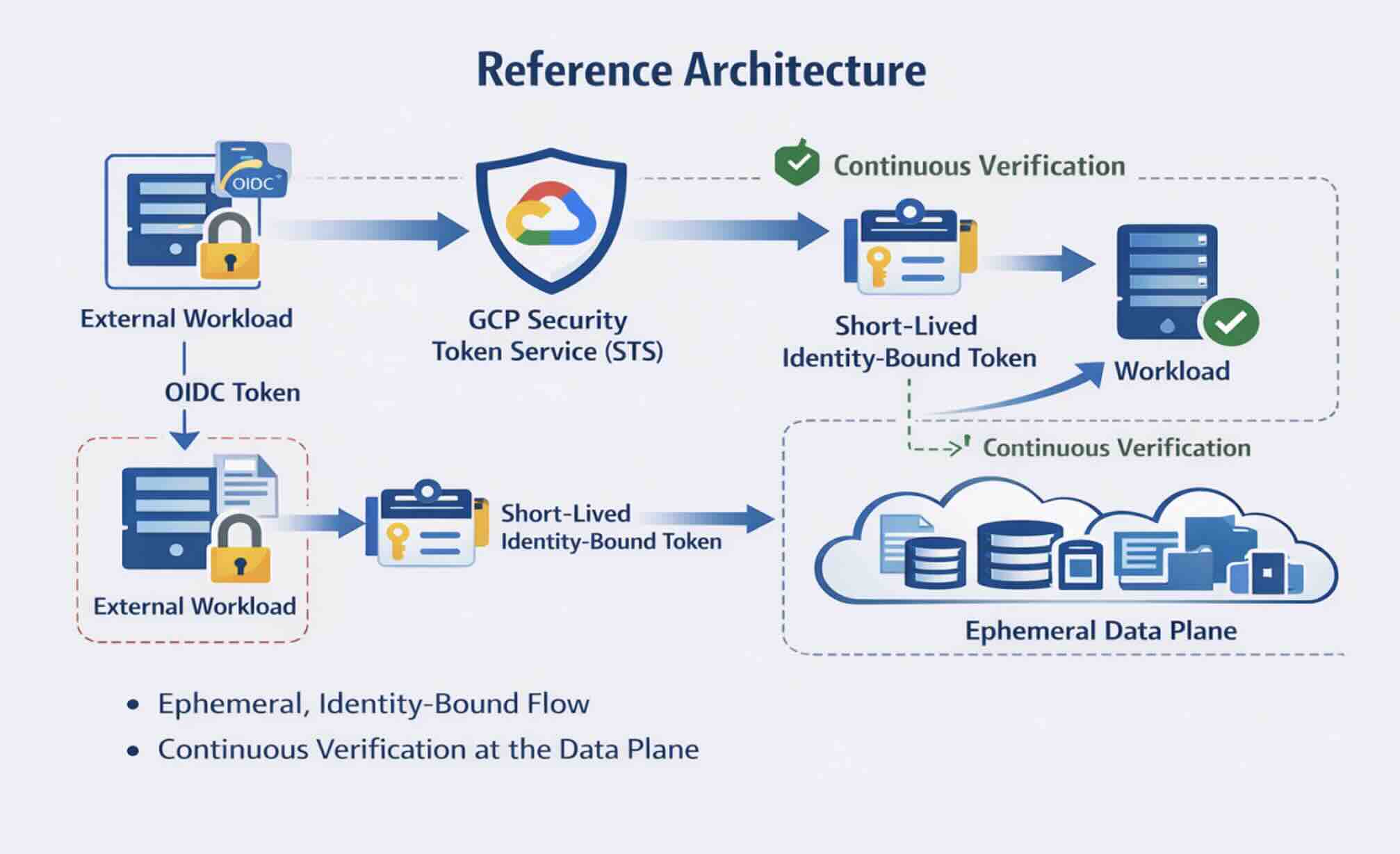
Google Cloud's Zero-Trust Data Plane Architecture
A zero-trust data plane is a self-sufficient entity that needs to be defined, visualized, constructed, provisioned, operated, and maintained. The Google Cloud Authoritative Architecture is a document that indicates how these concepts can be deployed by means of specialized components.
Core Pieces
- Google Cloud IAM: The identity and access management (IAM) solution is an all-encompassing service that addresses human and automated identities. It is the IAM service that lays down the law.
- Workload Identity Federation (WIF): This is a platform that empowers answers on items that the Service can authorize to share OIDC tokens or AWS/Azure credentials that are not only in Google Cloud, but also do not use static keys.
- Secure Token Service (STS): This solution provides users with temporary tokens that they can use for a specific period of time only. Therefore, in the end, the tokens get expired, which significantly lessens the chances of credential theft.
- IAM Conditions: They are the motive that allows an application to grant the least privilege by first taking the decision on the operating context of the application, the user of the application, and the conditions of the environment.
- Cloud Activity Logs: This tool is able to provide a complete view of the access policy, the credentials that are used, and the rules that are applied, which is vital for compliance and incident response activities.
Some end-to-end flow examples:
- In GKE, a Spark executor job accessing BigQuery receives access. The job then shows the OIDC token to GCP STS through WIF. The STS verifies the token and sends a token with a very short lifespan, which is only valid for the requested BigQuery dataset.
- A workload on Databricks, which is accessing GCS, is using the same pattern of OIDC token → STS → temporary credential → IAM policies to control access.
- A Kafka consumer that is publishing to Pub/Sub is using federated identities for dynamic authentication, with permissions applied per topic and per consumer.
Common Scenarios: Identity Federation in Action
The data plane's zero-trust enforcement applies different methods based on workloads. Here are three frequently seen situations that represent how static credentials are substituted with short-term, verifiable identities through identity federation.
GKE Spark Going to BigQuery (GCP-Native)
Context:
The executors of the Spark program in GKE are associated with Kubernetes Service Accounts that connect to Google Cloud Service Accounts by using Workload Identity. Therefore, JSON keys and static credentials are neither present nor required.
Pseudocode/config:
apiVersion: v1
kind: ServiceAccount
metadata:
name: spark-executor
annotations:
iam.gke.io/gcp-service-account: [email protected]Security benefits:
- Pod-level identity: Each executor has a separate identity.
- Automatic rotation: Credentials are short-lived and automatically rotated.
- Blast radius containment: Compromised pods cannot access data beyond their scoped permissions.
Databricks → GCS via Workload Identity Federation
Context:
A read-only long-lived secret in the Databricks GCS makes rotation a nightmare and, moreover, makes the GCS very susceptible to the token leak issue, badly affecting the whole system.
Solution:
By regulating the OIDC-based federation between Databricks and GCP, the workloads utilize OIDC tokens to impress them into the GCP Secure Token Service (STS) that issues scoped, short-lived credentials for GCS.
Flow:
Databricks job → OIDC token → STS → temporary GCS credentials → enforced by IAM policies.Kafka Consumers → GCP Services
Context:
The standard Kafka authentication processes mainly hinge upon the distribution of the SASL secret, which indirectly raises the risk of credentials being used erroneously across connections.
Solution:
Instead, using a per-consumer, federated issuance of short-lived credentials, based on identity schemes, ensures it is the only way that users can access Pub/Sub or BigQuery, as the case may be, without the need for static secrets. Thus, in a case of security risk, the usage risk is reduced substantially.
The linking of the short-term workloads to the use of federated identities and by way of short-lived credentials ,organizations can virtually at all times rotate credentials, implement least privilege full access control, auto-rotate, and granularity. The demonstrations of these feats illustrate how zero trust can pervade across any kind of workload and milieu.
Cross-Cloud Comparison: Identity Federation Approaches
As businesses mature with multi-cloud and hybrid technologies, the best practice of identity federation depends on the platform-specific treatment to manage a zero-trust data plane. Each platform has its own way to manage workload identity, which sometimes is more or less secure but always different in terms of complexity.
Comparison table:
| Platform | Identity Model | Strengths | Weaknesses |
|---|---|---|---|
|
GCP |
Native Workload Identity Federation | Keyless, mature, fine-grained | Steeper learning curve |
|
AWS |
IAM Roles + OIDC | Widely supported | Role sprawl, policy complexity |
|
Snowflake |
OAuth / External OAuth | SaaS-friendly | Limited workload granularity |
|
Databricks |
PAT → OIDC (newer) | Improving security | Legacy token reliance |
|
Kafka |
SASL / mTLS | High performance | Operationally heavy |
Insights:
- GCP: It has the most extensive and integrated support for workload identity federation, allowing the use of no-key, ephemeral credentials in case of temporary workloads. Its reference architecture empowers the full-scale deployment of zero trust across the entire organization without restrictions
- AWS: It allows OIDC-based federation via IAM roles, but the intricacy of overseeing roles and policies might cause the operating costs to go up
- Snowflake: It relies on OAuth and external identity providers for its SaaS workloads, but is limited by the non-human identities detail, which makes it difficult to apply fine-grained data plane enforcement.
- Databricks: Moving from conventional Personal Access Tokens (PATs) to OIDC has positively transformed the security posture; nonetheless, the usage of legacy tokens still poses a threat.
- Kafka:It offers both SASL and mTLS as authentication methods alongside the guarantee of high throughput and performance, yet the handling of identity for each consumer is quite a strenuous task.
GCP has delivered the most complete and detailed reference model along the lines of zero trust. Through the mixture of Workload Identity Federation, short-lived credentials issued by STS, and IAM policy conditions, enterprises are able to dynamically impose the least privilege, decrease the blast radius, and protect ephemeral workloads that traverse the data pipelines. The comparison shows that even if multi-cloud federation is possible, the maturity and embedded support of each platform will significantly determine how effective zero trust can be in the data plane.
Engineering Challenges and Practical Solutions
Laying a zero-trust data plane is, in theory, a straightforward task, but the execution is impeded by several technical issues, which are challenging. These problems generally fall into a few categories:
- Identity management issues: Having numerous service accounts, workload identities, and external tokens is a normal feature of complex deployments, and this situation can make managing these things hard.
- Debugging federated auth failures: Federation operates a validation layer and, thus, it is not easy to identify if errors occurred during the token exchange or in the IAM policy.
- Legacy workloads: Some of the older pipelines or tools may be using static keys only or be compatible with certain authentication flows, and as a result, migration becomes difficult.
- Policy complexity: The IAM policies for fine-grained access control applied to temporary workloads, multi-cloud environments, and many services frequently become extremely complicated.
- Observability gaps: The use of short-lived credentials and transient identities makes it harder to identify access patterns and to track audit events.
Practical Measures
- Centralized identity taxonomy: Formulate a standardized naming and mapping for workloads and identities so as to cut down the sprawl and ease the management of policies.
- IAM conditions and attributes: Deploy contextual attributes — like workload type, location, or environment—to impose fine-grained,least-privilege access in real time, that is, dynamically.
- Short-lived credentials with strict TTL: Reduce the chance of credential compromise by the issuance of tokens that are programmed to expire and rotate automatically.
- Event logs + SIEM integration: Channel all usage of credentials and events of access to a central observability platform for the purposes of detecting anomalies,compliance,and forensic analysis.
- Gradual migration from keys to federation: The replacement of static credentials will be done gradually, beginning with the highest-risk workloads to ensure business continuity and also cut down the attack surface.
Stepping individually through these issues, organizations can, in this way, harden their workloads, make them efficient and robust, and implement zero trust even in complicated, dispersed data pipelines.
Key Takeaways and Best Practices
Main Takeaways
- Critical IAM is just one of many. The traditional IAM resolves the control plane issue, but it does not protect the data plane
- Only identity-led security can protect data planes. Each workload, job, or service shall have a mandate to represent itself as an individual and reliable identity to authenticate.
- Federation beats static secrets. Transitioning to a federated model from long-term keys not only lowers the risk but also reduces the risk of operations.
- Short-lived credentials significantly broaden the security perimeter. Automated and prompt rotation and expiration practices restrict any possible intrusion damage to a minor area.
Best Practices Checklist
- Dispose of all long-term service account keys and follow this guideline strictly.
- Enable each workload to have a separate identity, not just across computing, streaming, and data jobs, but also beyond them.
- Use IAM conditions to enforce least privilege by confining access based on context, environment, and workload attributes.
- Keep conducting persistent monitoring and auditing with Cloud Activity Logs and SIEM integration for anomaly detection and compliance assurance.
Last Thoughts
Zero trust is not a final point; it's a choice of architecture. By making identity the main security barrier, using continuous verification, and adopting short-lived, federated credentials, organizations can secure, audit, and scale their data plane without extra costs or new cloud risks.
Opinions expressed by DZone contributors are their own.

Comments