Generating a Trusted SSL Certificate (Node Example)
Join the DZone community and get the full member experience.
Join For Free
An SSL Certificate is a file that helps browsers recognize that a domain name belongs to a server owner (as well as it's information like name, location, company, etc).
So, if you host your website without certificates, browsers will show users that the site is unsafe and might block the site itself or disable video/audio on it.
Ways to Generate SSL Certificates
1. Self-Signed Certificate
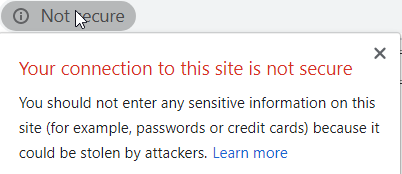
Such a certificate also won't be trusted by browsers. And you would need to ask all users to add that certificate in a trusted list in your browser's settings. It might work only for internal users. Otherwise, users will see something like this:
2. Generate a Certificate Signed by a Certificate Authority
The Let's Encrypt Foundation helps generate certificates that will be recognized as trusted in all browsers. In order to simplify certificate generation, you can use a fully automated service called certbot. Here's what you need to do to generate a certificate with cerbot:
- Attach your domain name to your server.
- Login to your server via ssh as root.
- Install certbot on your server and execute a set of commands.
- Wait until your certificate being recognized by browser (10 mins or so).
You may also like: Everything About HTTPS and SSL (Java).
Depending on your web server and operating system, you fill find the corresponding set of instructions in certbot's documentation.
Once you install certbot and execute the commands to generate your certificate, you will find certificate files in the /etc/letsencrypt/live/domain folder.
For your HTTPS server, you only need two files: cert.pem and privkey.pem.
You can then use those files to create a secure server with Node.js with the following script:
var nodeStatic = require('node-static');
var https = require('https');
var file = new (nodeStatic.Server)();
const fs = require('fs');
const options = {
key: fs.readFileSync('/etc/letsencrypt/live/domain/privkey.pem'),
cert: fs.readFileSync('/etc/letsencrypt/live/domain/cert.pem')
};
var app = https.createServer(options, function (req, res) {
file.serve(req, res);
}).listen(443);
Save that file as server.js and execute it.
xxxxxxxxxx
node server.js
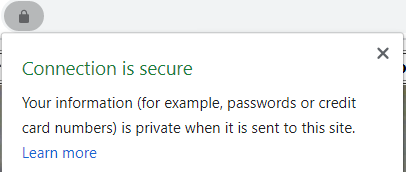
Wait until your certificate is synchronized and open your website. Now, your connection should be trusted:
Further Reading
Opinions expressed by DZone contributors are their own.

Comments