TEE in Android Development
This overview of TEE, or Trusted Execution Environments, will show you how they are used to secure sensitive information on Android devices.
Join the DZone community and get the full member experience.
Join For FreeThe Trusted Execution Environment (TEE) is a technique for securing the content on Android devices via securing the area of the main processor, to protect sensitive information. This helps in providing an isolated execution environment, and can further have Trusted Applications (TA) loaded into a separate space of execution to maintain trust, confidentiality, and integrity.
Challenge
The sensitive information on an Android device is vulnerable as it is comparatively easy to disassemble and extract the required information if the apps are executed in an insecure environment, and not much of an effort is required from hackers to achieve their goals.
Solution
Basically, TEE runs its own Trusted OS, which helps to process its own set of instructions, provide higher security for mobile solutions, and protect the Android app's sensitive information, which is executed, processed, and stored in this highly secure area.
Normally, a mobile device’s main OS can have weak links, which can be exploited by a hacker in order to attack the apps. By executing and processing the code and data in TEE, we can help maintain the confidentiality and integrity of the apps, which can be isolated and executed in the secure environment.
The following diagram compares the TEE (Trusted Execution Environment) and REE (Rich Execution Environment).
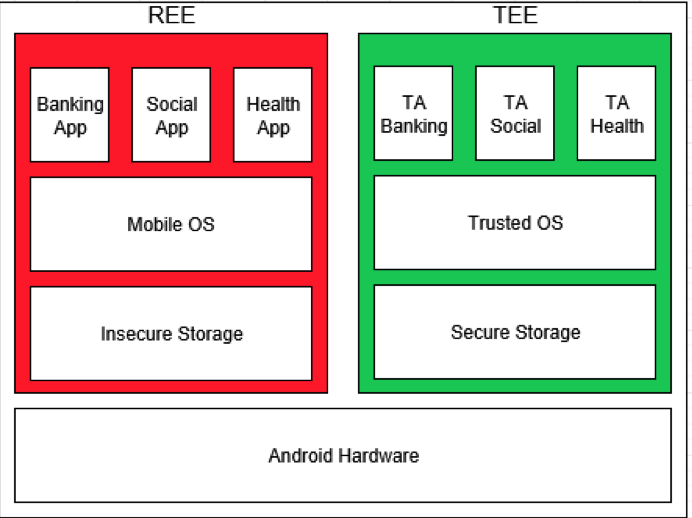
Trusted OS & Secure Storage: This contains the functionality of a kernel (like a filesystem call) in a secure and isolated environment. As part of the implementation details, the chunk of memory could be allocated by the exposed Trusted OS API in order to allocate the secure storage, which could be further used by Trusted Applications to protect their sensitive data.
Trusted Application (TA): All the TA code is executed and processed under the Trusted OS, and TA data is stored in secure storage, which helps maintain the confidentiality and integrity of the TA. In order to protect Android apps, we can have them executed as a Trusted Application under TEE.
Conclusion
TEE helps code and data loaded inside to be protected in a secure environment and allow only Trusted Applications to be executed.
Opinions expressed by DZone contributors are their own.

Comments